
2022 Annual Repor
Leveraging our
assets for B2B
opporunities
Customer and
Member Value
Best, first
place to shop
Health and
Wellness
Lower
Cost
Financial
Services
Even more
items and
services
B
u
i
l
d
i
n
g
o
u
r
F
l
y
w
h
e
e
l

$572.8 BILLION
in revenue
Key Financial Metrics
6.4%
Walmar U.S.
comp sales
$24.2 BILLION
in operating
cash flow
$15.9 BILLION
returns to
shareholders
A focused international
business with
NET SALES OF
$101 BILLION
Fiscal 2022
Highlights
Invested
$13 BILLION
in CapEx for growth
Revenue grew
$14 BILLION YOY
INCREASED THE
DIVIDEND
for the 49th
consecutive year in
February 2022
eCommerce business
$73 BILLION
IN NET SALES
A $74 BILLION
CLUB BUSINESS –
in one of retail’s fastest
growing formats
U.S. Marketplace added
more than
20 THOUSAND
new sellers and
~75 MILLION
additional SKUs

UNITED STATES
SECURITIES AND EXCHANGE COMMISSION
Washington, D.C. 20549
___________________________________________
FORM 10-K
___________________________________________
☒
Annual report pursuant to section 13 or 15(d) of the Securities Exchange Act of 1934
For the fiscal year ended January 31, 2022, or
☐
Transition report pursuant to section 13 or 15(d) of the Securities Exchange Act of 1934
Commission file number 001-06991.
___________________________________________
WALMART INC.
(Exact name of registrant as specified in its charter)
___________________________________________
DE 71-0415188
(State or other jurisdiction of
incorporation or organization)
(IRS Employer Identification No.)
702 S.W. 8th Street
72716Bentonville, AR
(Address of principal executive offices) (Zip Code)
Registrant's telephone number, including area code: (479) 273-4000
Securities registered pursuant to Section 12(b) of the Act:
Title of each class Trading Symbol(s) Name of each exchange on which registered
Common Stock, par value $0.10 per share WMT NYSE
1.900% Notes Due 2022 WMT22 NYSE
2.550% Notes Due 2026 WMT26 NYSE
Securities registered pursuant to Section 12(g) of the Act: None
___________________________________________
Indicate by check mark if the registrant is a well-known seasoned issuer, as defined in Rule 405 of the Securities Act.
Yes ý No ¨
Indicate by check mark if the registrant is not required to file reports pursuant to Section 13 or Section 15(d) of the
Exchange Act.
Yes ¨ No ý

Indicate by check mark whether the registrant (1) has filed all reports required to be filed by Section 13 or 15(d) of the
Securities Exchange Act of 1934 during the preceding 12 months (or for such shorter period that the registrant was required to
file such reports), and (2) has been subject to such filing requirements for at least the past 90 days.
Yes ý No ¨
Indicate by check mark whether the registrant has submitted electronically every Interactive Data File required to be submitted
pursuant to Rule 405 of Regulation S-T (§232.405 of this chapter) during the preceding 12 months (or for such shorter period
that the registrant was required to submit such files).
Yes ý No ¨
Indicate by check mark whether the registrant is a large accelerated filer, an accelerated filer, a non-accelerated filer, a smaller
reporting company or an emerging growth company. See the definitions of "large accelerated filer," "accelerated filer,"
"smaller reporting company" and "emerging growth company" in Rule 12b-2 of the Exchange Act.
Large Accelerated Filer
☒
Accelerated Filer
☐
Non-Accelerated Filer
☐
Smaller Reporting Company
☐
Emerging Growth Company
☐
If an emerging growth company, indicate by check mark if the registrant has elected not to use the extended transition period
for complying with any new or revised financial accounting standards provided pursuant to Section 13(a) of the Exchange Act.
☐
Indicate by check mark whether the registrant has filed a report on and attestation to its management's assessment of the
effectiveness of its internal control over financial reporting under Section 404(b) of the Sarbanes-Oxley Act (15 U.S.C.
7262(b)) by the registered public accounting firm that prepared or issued its audit report. ☒
Indicate by check mark whether the registrant is a shell company (as defined in Rule 12b-2 of the Exchange Act).
Yes ☐ No ☒
As of July 31, 2021, the aggregate market value of the voting common stock of the registrant held by non-affiliates of the
registrant, based on the closing sale price of those shares on the New York Stock Exchange reported on July 30, 2021, was
$206,032,159,403. For the purposes of this disclosure only, the registrant has assumed that its directors, executive officers (as
defined in Rule 3b-7 under the Exchange Act) and the beneficial owners of 5% or more of the registrant's outstanding common
stock are the affiliates of the registrant.
The registrant had 2,751,779,629 shares of common stock outstanding as of March 16, 2022.
DOCUMENTS INCORPORATED BY REFERENCE
Document Parts Into Which Incorporated
Portions of the registrant's Proxy Statement for the Annual
Meeting of Shareholders to be held June 1, 2022 (the "Proxy
Statement")
Part III

Walmart Inc.
Form 10-K
For the Fiscal Year Ended January 31, 2022
Table of Contents
Page
Part I
Item 1 Business 6
Item 1A Risk Factors 15
Item 1B Unresolved Staff Comments 26
Item 2 Properties 27
Item 3 Legal Proceedings 30
Item 4 Mine Safety Disclosures 31
Part II
Item 5 Market for Registrant's Common Equity, Related Stockholder Matters and Issuer Purchases of Equity Securities 32
Item 6 Reserved 33
Item 7 Management's Discussion and Analysis of Financial Condition and Results of Operations 34
Item 7A Quantitative and Qualitative Disclosures About Market Risk 47
Item 8 Financial Statements and Supplementary Data 49
Item 9 Changes in and Disagreements with Accountants on Accounting and Financial Disclosure 80
Item 9A Controls and Procedures 80
Item 9B Other Information 80
Item 9C Disclosure Regarding Foreign Jurisdictions that Prevent Inspections 80
Part III
Item 10 Directors, Executive Officers and Corporate Governance 81
Item 11 Executive Compensation 81
Item 12 Security Ownership of Certain Beneficial Owners and Management and Related Stockholder Matters 81
Item 13 Certain Relationships and Related Transactions, and Director Independence 81
Item 14 Principal Accounting Fees and Services 81
Part IV
Item 15 Exhibits, Financial Statement Schedules 82
Item 16 Form 10-K Summary 84
Signatures 85

WALMART INC.
ANNUAL REPORT ON FORM 10-K
FOR THE FISCAL YEAR ENDED JANUARY 31, 2022
All references in this Annual Report on Form 10-K, the information incorporated into this Annual Report on Form 10-K by
reference to information in the Proxy Statement of Walmart Inc. for its Annual Shareholders' Meeting to be held on June 1,
2022 and in the exhibits to this Annual Report on Form 10-K to "Walmart Inc.," "Walmart," "the Company," "our Company,"
"we," "us" and "our" are to the Delaware corporation named "Walmart Inc." and, except where expressly noted otherwise or the
context otherwise requires, that corporation's consolidated subsidiaries.
PART I
Cautionary Statement Regarding Forward-Looking Statements
This Annual Report on Form 10-K and other reports, statements, and information that Walmart Inc. (which individually or
together with its subsidiaries, as the context otherwise requires, is referred to as "we," "Walmart" or the "Company") has filed
with or furnished to the Securities and Exchange Commission ("SEC") or may file with or furnish to the SEC in the future, and
prior or future public announcements and presentations that we or our management have made or may make, include or may
include, or incorporate or may incorporate by reference, statements that may be deemed to be "forward-looking statements"
within the meaning of Section 21E of the Securities Exchange Act of 1934, as amended (the "Act"), that are intended to enjoy
the protection of the safe harbor for forward-looking statements provided by the Act as well as protections afforded by other
federal securities laws.
Nature of Forward-Looking Statements
Such forward-looking statements are not statements of historical facts, but instead express our estimates or expectations for our
consolidated, or one of our segment's, economic performance or results of operations for future periods or as of future dates or
events or developments that may occur in the future or discuss our plans, objectives or goals. These forward-looking
statements may relate to:
• the growth of our business or change in our competitive position in the future or in or over particular periods;
• the amount, number, growth, increase, reduction or decrease in or over certain periods, of or in certain financial items
or measures or operating measures, including our earnings per share, net sales, comparable store and club sales, our
Walmart U.S. operating segment's eCommerce sales, liabilities, expenses of certain categories, expense leverage,
operating income, returns, capital and operating investments or expenditures of particular types and new store
openings;
• investments and capital expenditures we will make and how certain of those investments and capital expenditures are
expected to be financed;
• our increasing investments in eCommerce, technology, supply chain, store remodels and other omni-channel customer
initiatives, such as same day pickup and delivery;
• our workforce strategy;
• volatility in currency exchange rates affecting our or one of our segments' results of operations;
• the Company continuing to provide returns to shareholders through share repurchases and dividends, the use of share
repurchase authorization over a certain period or the source of funding of a certain portion of our share repurchases;
• our sources of liquidity, including our cash, continuing to be adequate or sufficient to fund our operations, finance our
global investment and expansion activities, pay dividends and fund share repurchases;
• cash flows from operations, our current cash position and access to capital markets will continue to be sufficient to
meet our anticipated operating cash needs;
• the reclassification of amounts related to our derivatives;
• our effective tax rate for certain periods and the realization of certain net deferred tax assets and the effects of
resolutions of tax-related matters;
• the effect of adverse decisions in, or settlement of, litigation or other proceedings or investigations to which we are
subject;
• the effect on the Company's results of operations or financial position of the Company's adoption of certain new, or
amendments to existing, accounting standards; or
• our commitments, intentions, plans or goals related to environmental, sustainability, and governance ("ESG")
priorities, including, but not limited to, the sustainability of our environment and supply chains, the promotion of
economic opportunity or other societal initiatives.
Our forward-looking statements may also include statements of our strategies, plans and objectives for our operations, including
areas of future focus in our operations, and the assumptions underlying any of the forward-looking statements we make. The
forward-looking statements we make can typically be identified by the use therein of words and phrases such as "aim,"
4
"anticipate," "believe," "could be," "could increase," "could occur," "could result," "continue," "estimate," "expansion,"
"expect," "expectation," "expected to be," "focus," "forecast," "goal," "grow," "guidance," "intend," "invest," "is expected,"
"may continue," "may fluctuate," "may grow," "may impact," "may result," "objective," "plan," "priority," "project," "strategy,"
"to be," "we'll," "we will," "will add," "will allow," "will be," "will benefit," "will change," "will come in at," "will continue,"
"will decrease," "will grow," "will have," "will impact," "will include," "will increase," "will open," "will remain," "will result,"
"will stay," "will strengthen," "would be," "would decrease" and "would increase," variations of such words or phrases, other
phrases commencing with the word "will" or similar words and phrases denoting anticipated or expected occurrences or results.
The forward-looking statements that we make or that are made by others on our behalf are based on our knowledge of our
business and our operating environment and assumptions that we believe to be or will believe to be reasonable when such
forward-looking statements were or are made. As a consequence of the factors described above, the other risks, uncertainties
and factors we disclose below and in the other reports as mentioned above, other risks not known to us at this time, changes in
facts, assumptions not being realized or other circumstances, our actual results may differ materially from those discussed in or
implied or contemplated by our forward-looking statements. Consequently, this cautionary statement qualifies all forward-
looking statements we make or that are made on our behalf, including those made herein and incorporated by reference herein.
We cannot assure you that the results or developments expected or anticipated by us will be realized or, even if substantially
realized, that those results or developments will result in the expected consequences for us or affect us, our business, our
operations or our operating results in the manner or to the extent we expect. We caution readers not to place undue reliance on
such forward-looking statements, which speak only as of their dates. We undertake no obligation to revise or update any of the
forward-looking statements to reflect subsequent events or circumstances except to the extent required by applicable law.
5

ITEM 1. BUSINESS
General
Walmart Inc. ("Walmart," the "Company" or "we") helps people around the world save money and live better – anytime and
anywhere – by providing the opportunity to shop in both retail stores and through eCommerce, and to access our other service
offerings. Through innovation, we strive to continuously improve a customer-centric experience that seamlessly integrates our
eCommerce and retail stores in an omni-channel offering that saves time for our customers. Each week, we serve
approximately 230 million customers who visit more than 10,500 stores and numerous eCommerce websites under 46 banners
in 24 countries.
Our strategy is to make every day easier for busy families, operate with discipline, sharpen our culture and become more digital,
and make trust a competitive advantage. Making life easier for busy families includes our commitment to price leadership,
which has been and will remain a cornerstone of our business, as well as increasing convenience to save our customers time.
By leading on price, we earn the trust of our customers every day by providing a broad assortment of quality merchandise and
services at everyday low prices ("EDLP"). EDLP is our pricing philosophy under which we price items at a low price every
day so our customers trust that our prices will not change under frequent promotional activity. Everyday low cost ("EDLC") is
our commitment to control expenses so our cost savings can be passed along to our customers.
Our operations comprise three reportable segments: Walmart U.S., Walmart International and Sam's Club. Our fiscal year ends
on January 31 for our United States ("U.S.") and Canadian operations. We consolidate all other operations generally using a
one-month lag and on a calendar year basis. Our discussion is as of and for the fiscal years ended January 31, 2022 ("fiscal
2022"), January 31, 2021 ("fiscal 2021") and January 31, 2020 ("fiscal 2020"). During fiscal 2022, we generated total revenues
of $572.8 billion, which was comprised primarily of net sales of $567.8 billion.
We maintain our principal offices in Bentonville, Arkansas. Our common stock trades on the New York Stock Exchange under
the symbol "WMT."
The Development of Our Company
The businesses conducted by our founders began in 1945 when Sam M. Walton opened a franchise Ben Franklin variety store
in Newport, Arkansas. In 1946, his brother, James L. Walton, opened a similar store in Versailles, Missouri. Until 1962, our
founders' business was devoted entirely to the operation of variety stores. In 1983, we opened our first Sam's Club, and in 1988,
we opened our first supercenter. In 1998, we opened our first Walmart Neighborhood Market. In 1991, we began our first
international initiative when we entered into a joint venture in Mexico and, as of January 31, 2022, our Walmart International
segment conducted business in 23 countries.
In 2000, we began our first eCommerce initiative by creating both walmart.com and samsclub.com. Since then, our
eCommerce presence has continued to grow. In 2007, leveraging our physical stores, walmart.com launched its Site to Store
service, enabling customers to make a purchase online and pick up merchandise in stores. To date, we now have over 8,000
pickup and 6,000 delivery locations globally. In recent years, we have heavily invested in omni-channel and eCommerce
innovation, as well as made several eCommerce acquisitions to better serve our customers. These investments have enabled us
to leverage technology, talent and expertise, incubate digitally-native brands, and expand our assortment and service offerings.
We have also continued to enhance our eCommerce initiatives internationally, such as with our acquisition of a majority stake
of Flipkart Private Limited ("Flipkart"), which is our ecosystem in India that includes eCommerce platforms of Flipkart and
Myntra as well as PhonePe, a digital transaction platform.
We are enhancing our ecosystem with our omni-channel capabilities, stores, service offerings, eCommerce websites and
marketplaces as well as our supply chain combined with approximately 2.3 million associates as of January 31, 2022 to better
serve our customers. Together, we believe these elements produce a flywheel effect which creates relationships where
customers view Walmart as their primary destination. In the U.S., our Walmart+ membership incorporates several service
offerings which provide enhanced omni-channel shopping experiences and benefits for members. As we execute on our
strategy, our flywheel is accelerating through offerings such as our Walmart Connect advertising business, Walmart Fulfillment
Services, our health and wellness business, including Walmart Health, and our financial services business. These offerings
represent mutually reinforcing pieces of our flywheel centered around our customers around the world who are increasingly
seeking convenience.
6

Information About Our Segments
We are engaged in global operations of retail, wholesale and other units, as well as eCommerce, located throughout the U.S.,
Africa, Canada, Central America, Chile, China, India and Mexico. We also previously operated in Argentina prior to the sale of
Walmart Argentina in fiscal 2021 and operated in the United Kingdom and Japan prior to the sale of those operations in the first
quarter of fiscal 2022. Refer to Note 12 to our Consolidated Financial Statements for information on these divestitures. Our
operations are conducted in three reportable segments: Walmart U.S., Walmart International and Sam's Club, which are further
described below. Each segment contributes to the Company's operating results differently. However, each has generally
maintained a consistent contribution rate to the Company's net sales and operating income in recent years other than minor
changes to the contribution rate for the Walmart International segment due to fluctuations in currency exchange rates.
Additional information on our operating segments and geographic information is contained in Note 13 to our Consolidated
Financial Statements.
Walmart U.S. Segment
Walmart U.S. is our largest segment and operates in the U.S., including in all 50 states, Washington D.C. and Puerto Rico.
Walmart U.S. is a mass merchandiser of consumer products, operating under the "Walmart" and "Walmart Neighborhood
Market" brands, as well as walmart.com and other eCommerce brands. Walmart U.S. had net sales of $393.2 billion for fiscal
2022, representing 69% of our fiscal 2022 consolidated net sales, and had net sales of $370.0 billion and $341.0 billion for
fiscal 2021 and 2020, respectively. Of our three segments, Walmart U.S. has historically had the highest gross profit as a
percentage of net sales ("gross profit rate"). In addition, Walmart U.S. has historically contributed the greatest amount to the
Company's net sales and operating income.
Omni-channel. Walmart U.S. provides an omni-channel experience to customers, integrating retail stores and eCommerce,
through services such as pickup and delivery, ship-from-store, and digital pharmacy fulfillment options. As of January 31,
2022, we had approximately 4,600 pickup locations and more than 3,500 same-day delivery locations. Our Walmart+
membership offering provides enhanced omni-channel shopping benefits that currently include unlimited free shipping on
eligible items with no order minimum, unlimited delivery from store, fuel and pharmacy discounts, and mobile scan & go for a
streamlined in-store shopping experience. We have several eCommerce websites, the largest of which is walmart.com. We
define eCommerce sales as sales initiated by customers digitally and fulfilled by a number of methods including our dedicated
eCommerce fulfillment centers and leveraging our stores. The following table provides the approximate size of our retail stores
as of January 31, 2022:
Minimum
Square Feet
Maximum
Square Feet
Average
Square Feet
Supercenters (general merchandise and grocery) 69,000 260,000 178,000
Discount stores (general merchandise and limited grocery) 30,000 221,000 105,000
Neighborhood markets
(1)
(grocery) 28,000 65,000 42,000
(1)
Excludes other small formats.
Merchandise. Walmart U.S. does business in three strategic merchandise units, listed below:
• Grocery consists of a full line of grocery items, including dry grocery, snacks, dairy, meat, produce, deli & bakery,
frozen foods, alcoholic and nonalcoholic beverages, as well as consumables such as health and beauty aids, pet
supplies, household chemicals, paper goods and baby products;
• General merchandise includes:
◦ Entertainment (e.g., electronics, toys, seasonal merchandise, wireless, video games, movies, music and
books);
◦ Hardlines (e.g., automotive, hardware and paint, sporting goods, outdoor living and stationery);
◦ Apparel (e.g., apparel for men, women, girls, boys and infants, as well as shoes, jewelry and accessories); and
◦ Home (e.g., housewares and small appliances, bed & bath, furniture and home organization, home
furnishings, home decor, fabrics and crafts).
• Health and wellness includes pharmacy, over-the-counter drugs and other medical products, optical services and other
clinical services.
Brand name merchandise represents a significant portion of the merchandise sold in Walmart U.S. We also market lines of
merchandise under our private brands, including brands such as: "Allswell," "Athletic Works," "Bonobos Fielder," "Eloquii
Elements," "Equate," "Free Assembly," "Freshness Guaranteed," "George," "Great Value," "Holiday Time," "Hyper Tough,"
"Mainstays," "Marketside," "No Boundaries," "onn.," "Ozark Trail," "Parent's Choice," "Sam's Choice," "Scoop," "Spring
Valley," "Time and Tru," "Way to Celebrate" and "Wonder Nation." The Company also markets lines of merchandise under
licensed brands, some of which include: "Avia," "Better Homes & Gardens," "Pioneer Woman" and "Sofia Jeans by Sofia
Vergara."
7

Periodically, revisions are made to the categorization of the components comprising our strategic merchandise units. When
revisions are made, the previous periods' presentation is adjusted to maintain comparability.
The Walmart U.S. business also includes an in-house advertising offering via Walmart Connect, supply chain and fulfillment
capabilities to online marketplace sellers via Walmart Fulfillment Services, and access to quality, affordable healthcare via
Walmart Health. In Fiscal 2022, Walmart U.S. initiatives also included the launch of a B2B last mile delivery service platform
via Walmart GoLocal, and Walmart Luminate which provides a suite of data products to merchants and suppliers. Additional
service offerings include fuel, financial services and related products (including through our digital channels, stores and clubs
as well as our previously announced fintech joint venture), such as money orders, prepaid access, money transfers, check
cashing, bill payment, and certain types of installment lending. Combined, these offerings do not currently represent a
significant portion of annual segment revenues.
Operations. Walmart U.S. is available to customers through supercenters, discount stores and neighborhood markets, as well
as online or through the mobile application 24 hours a day. Consistent with its strategy, Walmart U.S. continues to develop
technology tools and services to better serve customers and help stores operate more efficiently, such as pickup and delivery,
Walmart+, ship-from-store and other initiatives which provide convenient and seamless omni-channel shopping experiences.
Seasonal Aspects of Operations. Walmart U.S.'s business is seasonal to a certain extent due to calendar events and national
and religious holidays, as well as different weather patterns. Historically, its highest sales volume has occurred in the fiscal
quarter ending January 31.
Competition. Walmart U.S. competes with brick and mortar, eCommerce, and omni-channel retailers operating discount,
department, retail and wholesale grocers, drug, dollar, variety and specialty stores, supermarkets, hypermarkets and
supercenter-type stores, eCommerce retailers, as well as companies that offer services in digital advertising, fulfillment and
delivery services, health and wellness, and financial services. Each of these landscapes is highly competitive and rapidly
evolving, and new business models and the entry of new, well-funded competitors continue to intensify this competition. Some
of our competitors have longer histories in these lines of business, more customers, and greater brand recognition. They may be
able to obtain more favorable terms from suppliers and business partners and to devote greater resources to the development of
these businesses. In addition, for eCommerce and other internet-based businesses, newer or smaller businesses may be better
able to innovate and compete with us.
Our ability to develop and operate units at the right locations and to deliver a customer-centric omni-channel experience largely
determines our competitive position within the retail industry. We compete in a variety of ways, including the prices at which
we sell our merchandise, merchandise selection availability, services offered to customers, location, store hours, in-store
amenities, the shopping convenience and overall shopping experience we offer, the attractiveness and ease of use of our digital
platforms, cost and speed of and options for delivery to customers of merchandise purchased through our digital platforms or
through our omni-channel integration of our physical and digital operations. We employ many strategies and programs
designed to meet competitive pressures within our industry. These strategies include the following:
• EDLP: our pricing philosophy under which we price items at everyday low prices so our customers trust that our
prices will not change under frequent promotional activity;
• EDLC: everyday low cost is our commitment to control expenses so our cost savings can be passed along to our
customers;
• Omni-channel offerings such as pickup and delivery and our Walmart+ membership offering, all of which enhance
convenience and seek to serve customers in the ways they want to be served; and
• Expanding our flywheel and the products and services we offer in areas such as digital advertising, fulfillment
services, health and wellness, and financial services.
Distribution. We utilize a total of 157 distribution facilities which are located strategically throughout the U.S. For fiscal
2022, the majority of Walmart U.S.'s purchases of store merchandise were shipped through these facilities, while most of the
remaining store merchandise we purchased was shipped directly from suppliers. General merchandise and dry grocery
merchandise is transported primarily through the segment's private truck fleet; however, we contract with common carriers to
transport the majority of our perishable grocery merchandise. We ship merchandise purchased by customers on our
eCommerce platforms by a number of methods from multiple locations including from our 31 dedicated eCommerce fulfillment
centers, as well as leveraging our ability to ship or deliver directly from more than 3,500 stores.
Walmart International Segment
Walmart International is our second largest segment and operated in 23 countries outside of the U.S. as of January 31, 2022.
Walmart International operates through our wholly-owned subsidiaries in Canada, Chile, and China, and our majority-owned
subsidiaries in Africa (which includes Botswana, Ghana, Kenya, Lesotho, Malawi, Mozambique, Namibia, Nigeria, South
Africa, Swaziland, Tanzania, Uganda and Zambia), India, as well as Mexico and Central America (which includes Costa Rica,
El Salvador, Guatemala, Honduras and Nicaragua). Walmart International previously operated in Argentina prior to the sale of
8

Walmart Argentina in fiscal 2021 and operated in the United Kingdom and Japan prior to the sale of those operations in the first
quarter of fiscal 2022. Refer to Note 12 to our Consolidated Financial Statements for discussion of recent divestitures.
Walmart International includes numerous formats divided into two major categories: retail and wholesale. These categories
consist of many formats, including: supercenters, supermarkets, hypermarkets, warehouse clubs (including Sam's Clubs) and
cash & carry, as well as eCommerce through walmart.com.mx, walmart.ca, flipkart.com and other sites. Walmart International
had net sales of $101.0 billion for fiscal 2022, representing 18% of our fiscal 2022 consolidated net sales, and had net sales of
$121.4 billion and $120.1 billion for fiscal 2021 and 2020, respectively. The gross profit rate is lower than that of Walmart
U.S. primarily because of its format mix.
Walmart International's strategy is to create strong local businesses powered by Walmart which means being locally relevant
and customer-focused in each of the markets it operates. We are being deliberate about where and how we choose to operate
and continue to re-shape the portfolio to best enable long-term, sustainable and profitable growth. As such, we have taken
certain strategic actions to strengthen our Walmart International portfolio for the long-term, which include the following
highlights over the last three years:
• Divestiture of Walmart Argentina in November 2020.
• Divestiture of Asda Group Limited ("Asda"), our retail operations in the U.K., in February 2021.
• Divestiture of a majority stake in Seiyu, our retail operations in Japan, in March 2021.
Omni-channel. Walmart International provides an omni-channel experience to customers, integrating retail stores and
eCommerce, such as through pickup and delivery services in most of our markets, our marketplaces such as Flipkart in India,
and a digital transaction platform anchored in payments such as PhonePe in India. Same-day delivery capacity continues to
expand in Mexico, including our recent launch of a membership model which provides unlimited same-day delivery from
stores, and in China, our partnerships with JD.com and JD Daojia provide customers one-hour delivery by leveraging Walmart
stores as fulfillment centers. A value-based internet and telephone service was recently launched in Mexico allowing customers
to enjoy digital connectivity.
Generally, retail units' selling areas range in size from 1,400 square feet to 186,000 square feet. Our wholesale stores' selling
areas generally range in size from 24,000 square feet to 158,000 square feet. As of January 31, 2022, Walmart International
had approximately 2,900 pickup and over 1,900 delivery locations.
Merchandise. The merchandising strategy for Walmart International is similar to that of our operations in the U.S. in terms of
the breadth and scope of merchandise offered for sale. While brand name merchandise accounts for a majority of our sales, we
have both leveraged U.S. private brands and developed market specific private brands to serve our customers with high quality,
low priced items. Along with the private brands we market globally, such as "Equate," "George," "Great Value," "Holiday
Time," "Mainstays," "Marketside" and "Parent's Choice," our international markets have developed market specific brands
including "Aurrera," "Cambridge," "Extra Special," "Lider," "Myntra," and "PhonePe." In addition, we have developed and
continue to grow our relationships with regional and local suppliers in each market to ensure reliable sources of quality
merchandise that is equal to national brands at low prices.
Walmart International also offers advertising, financial services and related products in various markets. Our businesses in
Mexico and Canada, for example, offer prepaid cards and money transfers, and our PhonePe business in India provides a
platform that offers mobile and bill payment, person-to-person (P2P) payment, investment and insurance solutions, financial
services and advertising. Combined, these offerings did not represent a significant portion of annual segment revenues.
Operations. The hours of operation for operating units in Walmart International vary by country and by individual markets
within countries, depending upon local and national ordinances governing hours of operation. Consistent with its strategy,
Walmart International continues to develop technology tools and services to better serve customers and help its various formats
operate more efficiently, as well as to provide convenient and seamless omni-channel shopping experiences.
Seasonal Aspects of Operations. Walmart International's business is seasonal to a certain extent. Historically, its highest sales
volume has occurred in the fourth quarter of our fiscal year. The seasonality of the business varies by country due to different
national and religious holidays, festivals and customs, as well as different weather patterns.
Competition. Walmart International competes with brick and mortar, eCommerce, and omni-channel retailers who operate
department, drug, discount, variety and specialty stores, supermarkets, hypermarkets and supercenter-type stores, wholesale
clubs, home-improvement stores, specialty electronics stores, cash & carry operations and convenience stores, and eCommerce
retailers, as well as catalog businesses. Our ability to develop and operate units at the right locations and to deliver a customer-
centric omni-channel experience largely determines our competitive position within the retail industry. We believe price
leadership is a critical part of our business model and we continue to focus on moving our markets towards an EDLP approach.
Additionally, our ability to operate food departments effectively has a significant impact on our competitive position in the
markets where we operate. Each of these landscapes is highly competitive and rapidly evolving, and new business models and
the entry of new, well-funded competitors continue to intensify this competition. Some of our competitors have longer histories
9

in these lines of business, more customers, and greater brand recognition. They may be able to obtain more favorable terms
from suppliers and business partners and to devote greater resources to the development of these businesses. In addition, for
eCommerce and other internet-based businesses, newer or smaller businesses may be better able to innovate and compete with
us.
Distribution. We utilize a total of 179 distribution facilities located in Canada, Central America, Chile, China, India, Mexico
and South Africa. Through these facilities, we process and distribute both imported and domestic products to the operating
units of the Walmart International segment. During fiscal 2022, the majority of Walmart International's purchases passed
through these distribution facilities. Suppliers ship the remainder of Walmart International's purchases directly to our stores in
the various markets in which we operate. Across the segment, we have efficient networks connecting physical stores and
distribution and fulfillment centers which facilitate the movement of goods to where our customers live. We ship merchandise
purchased by customers on our eCommerce platforms by a number of methods from multiple locations including from our 83
dedicated eCommerce fulfillment centers, more than 3,400 eCommerce sort centers and last-mile delivery facilities in India, as
well as our physical retail stores.
Sam's Club Segment
Sam's Club operates in 44 states in the U.S. and in Puerto Rico. Sam's Club is a membership-only warehouse club that also
operates samsclub.com. Sam's Club had net sales of $73.6 billion for fiscal 2022, representing 13% of our consolidated fiscal
2022 net sales, and had net sales of $63.9 billion and $58.8 billion for fiscal 2021 and 2020, respectively. As a membership-
only warehouse club, membership income is a significant component of the segment's operating income. Sam's Club operates
with a lower gross profit rate and lower operating expenses as a percentage of net sales than our other segments.
Membership. The following two options are available to members:
Plus Membership Club Membership
Annual Membership Fee $100 $45
Number of Add-on Memberships ($40 each) Up to 16 Up to 8
All memberships include a spouse/household card at no additional cost. Plus Members are also eligible for free shipping on the
majority of merchandise, with no minimum order size, and receive discounts on prescriptions and glasses. Beginning in fiscal
2023, Sam's Club launched a single loyalty rewards currency called Sam's Cash which merges and replaces existing Cash
Rewards for Plus members and Cash Back for Sam's Club Mastercard holders. Members may redeem Sam's Cash on purchases
in the club and online, to pay for membership fees or for cash in clubs. Sam's Cash does not expire and is available for monthly
redemption.
Omni-channel. Sam's Club provides an omni-channel experience to customers, integrating retail stores and eCommerce
through such services as Curbside Pickup, mobile Scan & Go, ship-from-club, and delivery-from-club. Members have access
to a broad assortment of merchandise and services, including those not found in our clubs, online at samsclub.com and through
our mobile commerce applications. The warehouse facility sizes generally range between 32,000 and 168,000 square feet, with
an average size of approximately 134,000 square feet.
Merchandise. Sam's Club offers merchandise in the following five merchandise categories:
• Grocery and consumables includes dairy, meat, bakery, deli, produce, dry, chilled or frozen packaged foods, alcoholic
and nonalcoholic beverages, floral, snack foods, candy, other grocery items, health and beauty aids, paper goods,
laundry and home care, baby care, pet supplies and other consumable items;
• Fuel, tobacco and other categories;
• Home and apparel includes home improvement, outdoor living, gardening, furniture, apparel, jewelry, tools and power
equipment, housewares, toys, seasonal items, mattresses, and tire and battery centers;
• Technology, office and entertainment includes consumer electronics and accessories, software, video games, office
supplies, appliances, and third-party gift cards; and
• Health and wellness includes pharmacy, optical and hearing services and over-the-counter drugs.
In addition, the Member's Mark private label brand continues to expand its assortment and deliver member value.
Operations. Operating hours for Sam's Clubs are generally Monday through Friday from 10:00 a.m. to 8:00 p.m., Saturday
from 9:00 a.m. to 8:00 p.m. and Sunday from 10:00 a.m. to 6:00 p.m. Additionally, most club locations offer Plus Members the
ability to shop before the regular operating hours Monday through Saturday, starting at 8:00 a.m. Consistent with its strategy,
Sam's Club continues to develop technology tools to drive a great member experience. Curbside Pickup is available at all clubs
to help provide fast, easy and contact-free shopping for members. Sam's Club also offers "Scan & Go," a mobile checkout and
payment solution, which allows members to bypass the checkout line.
10

Seasonal Aspects of Operations. Sam's Club's business is seasonal to a certain extent due to calendar events and national and
religious holidays, as well as different weather patterns. Historically, its highest sales volume has occurred in the fiscal quarter
ending January 31.
Competition. Sam's Club competes with other membership-only warehouse clubs, the largest of which is Costco, as well as
with discount retailers, retail and wholesale grocers, general merchandise wholesalers and distributors, gasoline stations as well
as omni-channel and eCommerce retailers and catalog businesses. At Sam's Club, we provide value at members-only prices, a
quality merchandise assortment, and bulk sizing to serve both our Plus and Club members. Our eCommerce website and
mobile commerce applications have increasingly become important factors in our ability to compete.
Distribution. We utilize 28 dedicated distribution facilities located strategically throughout the U.S., as well as some of the
Walmart U.S. segment's distribution facilities which service the Sam's Club segment for certain items. During fiscal 2022, the
majority of Sam's Club's non-fuel club purchases were shipped from these facilities, while the remainder of our purchases were
shipped directly to Sam's Club locations by suppliers. Sam's Club ships merchandise purchased on samsclub.com and through
its mobile commerce applications by a number of methods including shipments made directly from clubs, 12 dedicated
eCommerce fulfillment centers and other distribution centers.
Sam's Club uses a combination of our private truck fleet, as well as common carriers, to transport non-perishable merchandise
from distribution facilities to clubs. The segment contracts with common carriers to transport perishable grocery merchandise
from distribution facilities to clubs.
Intellectual Property
We regard our trademarks, service marks, copyrights, patents, domain names, trade dress, trade secrets, proprietary
technologies, and similar intellectual property as important to our success, and with respect to our associates, customers and
others, we rely on trademark, copyright, and patent law, trade-secret protection, and confidentiality and/or license agreements to
protect our proprietary rights. We have registered, or applied for the registration of, a number of U.S. and international domain
names, trademarks, service marks and copyrights. Additionally, we have filed U.S. and international patent applications
covering certain of our proprietary technology. We have licensed in the past, and expect that we may license in the future,
certain of our proprietary rights to third parties.
Suppliers and Supply Chain
As a retailer and warehouse club operator, we utilize a global supply chain that includes both U.S. and international suppliers
from whom we purchase the merchandise that we sell in our stores, clubs and online. In many instances, we purchase
merchandise from producers located near the stores and clubs in which such merchandise will be sold, particularly products in
the "fresh" category. We offer our suppliers the opportunity to efficiently sell significant quantities of their products to us.
These relationships enable us to obtain pricing that reflects the volume, certainty and cost-effectiveness these arrangements
provide to such suppliers, which in turn enables us to provide low prices to our customers. Our suppliers are subject to
standards of conduct, including requirements that they comply with local labor laws, local worker safety laws and other
applicable laws. Our ability to acquire from our suppliers the assortment and volume of products we wish to offer to our
customers, to receive those products within the required time through our supply chain and to distribute those products to our
stores and clubs, determines, along with other supply chain logistics matters (such as containers or port access for example), in
part, our in-stock levels in our stores and clubs and the attractiveness of our merchandise assortment we offer to our customers
and members.
Government Regulation
As a company with global operations, we are subject to the laws of the United States and multiple foreign jurisdictions in which
we operate and the rules and regulations of various governing bodies, which may differ among jurisdictions. For additional
information, see the risk factors herein in "Item 1A. Risk Factors" under the sub-caption "Legal, Tax, Regulatory, Compliance,
Reputational and Other Risks."
Environmental, Social and Governance ("ESG") Priorities
Our ESG strategy is centered on the concept of creating shared value: we believe we maximize long-term value and create
competitive advantage for the Company by serving our stakeholders, including our customers, associates, shareholders,
suppliers, business partners, and communities. We believe that addressing such societal needs builds the value of our business,
including by enhancing customer and associate trust, creating new revenue streams, managing cost and risk, building
capabilities for future advantage, and strengthening the underlying systems we all rely on.
We prioritize the ESG issues that offer the greatest potential for Walmart to create shared value: issues that rank high in
relevance to our business and stakeholders and which Walmart is positioned to make a positive impact. Our current ESG
priorities are categorized into four broad themes: opportunity, sustainability, community, and ethics and integrity.
11

• Opportunity. Retail can be a powerful engine for inclusive economic opportunity. We aim to advance diversity,
equity, and inclusion, and to provide opportunity for Walmart associates (as further described in the Human Capital
Management section below), our supply chain and the communities we're in to fulfill our customer mission, strengthen
our business and help people build a better life for themselves and their families.
• Sustainability. Walmart's sustainability efforts focus on our ability to create and preserve long-term value for both
people and planet. With respect to people, our sustainability efforts focus on sourcing responsibly, helping prevent
forced labor, empowering women, creating inclusive economic opportunity and selling safer, healthier products. With
respect to the planet, our efforts aim to enhance the sustainability of product supply chains by reducing emissions,
protecting and restoring nature, and reducing waste. To help address the effects of climate change, Walmart has set
science-based targets for emissions reduction, including our goal to achieve zero emissions in our operations by 2040
—without offsets—and to reduce or avoid one billion metric tons of emissions in our value chain by 2030 under our
Project Gigaton™ initiative.
• Community. Walmart aims to serve and strengthen communities by operating our business in a way that meets the
needs of our customer and community stakeholder groups, including by providing safer, healthier and more affordable
food and other products, disaster support, associate volunteerism, local grant programs and community cohesion
initiatives.
• Ethics and Integrity. At every level of our Company, we work to create a culture that inspires trust among our
associates, with our customers, and in the communities we serve.
We periodically publish information on our ESG priorities, strategies, and progress on our corporate website and may update
those disclosures from time to time. Nothing on our website, including our ESG reporting, documents or sections thereof, shall
be deemed incorporated by reference into this Annual Report on Form 10-K.
Human Capital Management
Our commitment to help people around the world save money and live better is delivered by our associates who make the
difference for our customers every day. As of the end of fiscal 2022, we employed approximately 2.3 million associates
worldwide, with approximately 1.7 million associates in the U.S. and approximately 0.6 million associates internationally. In
the U.S., approximately 94% of these associates are hourly and approximately 69% are full-time.
We believe the strength of our workforce, our associates, is a significant contributor to our success. Walmart is a place of
opportunity, not only as a foundational entry point to develop critical skills that are relevant for a variety of careers, but also a
place where people can grow in their careers across our global omni-channel business. As customer expectations and
technology change the nature of work, we are focused on attracting, developing, rewarding, and retaining associates to thrive in
an ever-changing environment. Approximately 75% of our U.S. salaried store, club and supply chain management started their
careers in hourly positions. Our focus on providing a path of career opportunity for our associates through robust training,
competitive wages and benefits, and opportunities for advancement creates a strong associate value proposition. The
COVID-19 pandemic and the related reassessment taking place across the workforce had an impact on our retention of
associates and as a result turnover in the U.S. increased compared to the previous fiscal year.
Our workforce strategy includes the following strategic priorities:
Inclusion - Build a Walmart for everyone: a diverse, equitable and inclusive company, where associates' ideas and opinions
matter. We are focused on creating an inclusive culture and a diverse associate base. Creating an environment where all
associates believe they belong and are empowered to be themselves, which we believe is essential in serving our customers now
and in the future. We publish our diversity representation twice yearly, and hold ourselves accountable to providing recurring
culture, diversity, equity, and inclusion updates to senior leadership, including our President and CEO, and members of the
Board of Directors. Of the approximately 2.3 million associates employed worldwide, 53% identify as women. In the U.S.,
49% of the approximately 1.7 million associates identify as people of color.
We review our processes regarding our commitment to fair-pay practices. We are committed to creating a performance culture
where associates are rewarded based on meaningful factors such as qualifications, experience, performance, and the work they
do.
To build a company where associates feel engaged, valued and heard, we gather and respond to associates' feedback in a variety
of ways, including but not limited to an anonymous, periodic associate engagement survey, our Open Door process, and one-
on-one interactions. Management reviews the results of feedback obtained from our formal associate engagement survey.
Feedback and suggestions received through these channels have led to meaningful changes in our business.
Well-being - Focus on the physical, emotional, and financial well-being of our associates. We invest in our associates by
offering competitive wages, as well as a broad range of benefits that vary based on customary local practices and statutory
requirements, and we believe these investments in our associates are important to our future. In the U.S., we offer affordable
healthcare coverage to our full-time and eligible part-time associates as well as company paid benefits such as 401(k) match,
12

maternity leave, a paid parental leave program to all full-time associates, paid time off, Associate Stock Purchase Plan match,
life insurance, behavioral health services, and a store discount card or Sam's Club membership. Additional information about
how we invest in our associates' well-being, including wage structure and pay, can be found in our Human Capital brief in our
most recent ESG reporting, which is available on our corporate website. Nothing on our website, including our ESG reporting
documents, or sections thereof, shall be deemed incorporated by reference into this Annual Report on Form 10-K or
incorporated by reference into any of our other filings with the Securities and Exchange Commission. Certain information
relating to retirement-related benefits we provide to our associates is included in Note 11 to our Consolidated Financial
Statements.
The health and safety of our associates remain our biggest priorities and we continue to focus on enabling access to vaccines,
providing safeguards within facilities, and supporting associates. We encourage all associates to consider the COVID-19
vaccine and provide access to make the decision easier. Associates can become vaccinated while on the clock or receive paid
time off to do so. Our COVID-leave policy, which was implemented in March 2020 to support associates during the pandemic,
has been extended through March 31, 2022.
Growth - Provide ongoing growth, development and learning opportunities for associates and continue to attract talent with
new skills. We are invested in the growth of our associates in support of our business and their success. We invest in associate
development – including new roles and career paths, cross-training, on-the-job learning and coaching, and formal, classroom-
style training such as Walmart Academy in the U.S. We also provide access to educational opportunities for our eligible
associates through our Live Better U program, which provides a pathway to earn a high school diploma or a college degree at
no cost, as well as multiple digital learning opportunities.
Digital - Accelerate digital transformation and ways of working to improve the associate experience and drive business results.
To deliver a seamless customer and associate experience, we continue to invest in digital tools to improve associate
productivity, engagement, and performance. As more customers shop digitally, we have adapted by adding more roles in
eCommerce fulfillment and our home office associates have accelerated tech-based solutions that enhance the customer and
associate experiences.
13

Information About Our Executive Officers
The following chart names the executive officers of the Company as of the date of the filing of this Annual Report on Form 10-
K with the SEC, each of whom is elected by and serves at the pleasure of the Board of Directors. The business experience
shown for each officer has been his or her principal occupation for at least the past five years, unless otherwise noted.
Name Business Experience
Current
Position
Held Since Age
Daniel J. Bartlett Executive Vice President, Corporate Affairs, effective June 2013. From
November 2007 to June 2013, he served as the Chief Executive Officer and
President of U.S. Operations at Hill & Knowlton, Inc., a public relations
company.
2013 50
M. Brett Biggs Executive Vice President and Chief Financial Officer, effective January 2016.
From January 2014 to December 2015, he served as Executive Vice President
and Chief Financial Officer of Walmart International.
2016 53
Rachel Brand Executive Vice President, Global Governance, Chief Legal Officer and
Corporate Secretary, effective April 2018. From May 2017 to February 2018,
she served as Associate Attorney General in the United States Department of
Justice. From January 2017 to May 2017, Ms. Brand was an Associate
Professor of Law at George Mason University Antonin Scalia Law School.
From August 2012 to February 2017, she served as a board member on the
Privacy and Civil Liberties Oversight Board of the U.S. government.
2018 48
David M. Chojnowski Senior Vice President and Controller effective January 2017. From October
2014 to January 2017, he served as Vice President and Controller, Walmart
U.S.
2017 52
John Furner Executive Vice President, President and Chief Executive Officer, Walmart U.S.
effective November 2019. From February 2017 until November 2019, he
served as President and Chief Executive Officer, Sam's Club. From October
2015 to January 2017, he served as Executive Vice President and Chief
Merchandising Officer of Sam's Club.
2019 47
Suresh Kumar Executive Vice President, Global Chief Technology Officer and Chief
Development Officer effective July 2019. From February 2018 until June 2019,
Mr. Kumar was Vice President and General Manager at Google LLC. From
May 2014 until February 2018, he was Corporate Vice President at Microsoft
Corporation.
2019 57
Judith McKenna Executive Vice President, President and Chief Executive Officer, Walmart
International, effective February 2018. From February 2015 to January 2018,
she served as Executive Vice President and Chief Operating Officer of
Walmart U.S.
2018 55
Kathryn McLay Executive Vice President, President and Chief Executive Officer, Sam's Club
effective November 15, 2019. From February 2019 to November 2019, she
served as Executive Vice President, Walmart U.S. Neighborhood Markets.
From December 2015 until February 2019, she served as Senior Vice President,
U.S. Supply Chain. Ms. McLay originally joined the Company in April 2015 as
Vice President of U.S. Finance and Strategy.
2019 48
C. Douglas McMillon President and Chief Executive Officer, effective February 2014. From February
2009 to January 2014, he served as Executive Vice President, President and
Chief Executive Officer, Walmart International.
2014 55
Donna Morris Executive Vice President, Global People, and Chief People Officer, effective
February 2020. From April 2002 to January 2020, she worked at Adobe Inc. in
various roles, including most recently, Chief Human Resources Officer and
Executive Vice President, Employee Experience.
2020 54
14

Our Website and Availability of SEC Reports and Other Information
Our corporate website is located at www.stock.walmart.com. We file with or furnish to the SEC Annual Reports on Form 10-
K, Quarterly Reports on Form 10-Q, Current Reports on Form 8-K, amendments to those reports, proxy statements and annual
reports to shareholders, and, from time to time, other documents. The reports and other documents filed with or furnished to
the SEC are available to investors on or through our corporate website free of charge as soon as reasonably practicable after we
electronically file them with or furnish them to the SEC. The SEC maintains a website that contains reports, proxy and
information statements and other information regarding issuers, such as the Company, that file electronically with the SEC.
The address of that website is www.sec.gov. Our SEC filings, our Reporting Protocols for Senior Financial Officers and our
Code of Conduct can be found on our website at www.stock.walmart.com. These documents are available in print to any
shareholder who requests a copy by writing or calling our Investor Relations Department, which is located at our principal
offices.
A description of any substantive amendment or waiver of Walmart's Reporting Protocols for Senior Financial Officers or our
Code of Conduct for our chief executive officer, our chief financial officer and our controller, who is our principal accounting
officer, will be disclosed on our website at www.stock.walmart.com under the Corporate Governance section. Any such
description will be located on our website for a period of 12 months following the amendment or waiver.
ITEM 1A. RISK FACTORS
The risks described below could, in ways we may or may not be able to accurately predict, materially and adversely affect our
business, results of operations, financial position and liquidity. Our business operations could also be affected by additional
factors that apply to all companies operating in the U.S. and globally. The following risk factors do not identify all risks that we
may face.
Strategic Risks
Failure to successfully execute our omni-channel strategy and the cost of our investments in eCommerce and technology
may materially adversely affect our market position, net sales and financial performance.
The retail business continues to rapidly evolve and consumers increasingly embrace digital shopping. As a result, the portion of
total consumer expenditures with retailers and wholesale clubs occurring through digital platforms is increasing and the pace of
this increase could continue to accelerate.
Our strategy, which includes investments in eCommerce, technology, talent, supply chain automation, acquisitions, joint
ventures, store remodels and other customer initiatives, may not adequately or effectively allow us to continue to grow our
eCommerce business, increase comparable sales, maintain or grow our overall market position or otherwise offset the impact on
the growth of our business of a moderated pace of new store and club openings. The success of this strategy will depend in
large measure on our ability to continue building and delivering a seamless omni-channel shopping experience and
interconnected ecosystem for our customers that deepens our relationships with our customers across our various businesses
and partnerships and reinforces our overall flywheel strategy. The success of this strategy is further subject to the related risks
discussed in this Item 1A. With the interconnected components of this flywheel strategy and an increasing allocation of capital
expenditures focused on these initiatives, our failure to successfully execute on individual components of this strategy may
adversely affect our market position, net sales and financial performance which could also result in impairment charges to
intangible assets or other long-lived assets. In addition, a greater concentration of eCommerce sales, including increasing
online grocery sales, could result in a reduction in the amount of traffic in our stores and clubs, which would, in turn, reduce the
opportunities for cross-store or cross-club sales of merchandise that such traffic creates and could reduce our sales within our
stores and clubs and materially adversely affect our financial performance.
Furthermore, the cost of certain investments in eCommerce, technology, talent, automation, including any operating losses
incurred, will adversely impact our financial performance in the short-term and failure to realize the benefits of these
investments may adversely impact our financial performance over the longer term.
If we do not timely identify or effectively respond to consumer trends or preferences, it could negatively affect our
relationship with our customers, demand for the products and services we sell, our market share and the growth of our
business.
It is difficult to predict consistently and successfully the products and services our customers will demand and changes in their
shopping patterns. The success of our business depends in part on how accurately we predict consumer demand, availability of
merchandise, the related impact on the demand for existing products and services and the competitive environment. Price
transparency, assortment of products, customer experience, convenience, ease and the speed and cost of shipping are of primary
importance to customers and continue to increase in importance, particularly as a result of digital tools and social media
available to consumers and the choices available to consumers for purchasing products. Our failure to adequately or effectively
respond to changing consumer tastes, preferences (including those related to ESG issues) and shopping patterns, or any other
failure on our part to timely identify or effectively respond to changing consumer tastes, preferences and shopping patterns
15

could negatively affect our reputation and relationship with our customers, the demand for the products we sell or services we
offer, our market share and the growth of our business.
We face strong competition from other retailers, wholesale club operators, omni-channel retailers, and other businesses
which could materially adversely affect our financial performance.
Each of our segments competes for customers, employees, digital prominence, products and services and in other important
aspects of its business with many other local, regional, national and global physical, eCommerce and omni-channel retailers,
wholesale club operators and retail intermediaries, as well as companies that offer services in digital advertising, fulfillment and
delivery services, health and wellness, and financial services. The omni-channel retail landscape is highly competitive and
rapidly evolving, and the entry of new, well-funded competitors may increase competitive pressures. In addition, for
eCommerce and other internet-based businesses, newer or smaller businesses may be better able to innovate and compete with
us.
We compete in a variety of ways, including the prices at which we sell our merchandise, merchandise selection and availability,
services offered to customers, location, store hours, in-store amenities, the shopping convenience and overall shopping
experience we offer, the attractiveness and ease of use of our digital platforms, cost and speed of and options for delivery to
customers of merchandise purchased through our digital platforms or through our omni-channel integration of our physical and
digital operations.
A failure to respond effectively to competitive pressures and changes in the retail and other markets in which we operate, omni-
channel innovations and omni-channel ecosystems developed by our competitors or delays or failure in execution of our
strategy could materially adversely affect our financial performance. See "Item 1. Business" above for additional discussion of
the competitive situation of each of our reportable segments.
Certain segments of the retail industry are undergoing consolidation or substantially reducing operations, whether due to
bankruptcy, consolidation or other factors. Such consolidation, or other business combinations or alliances, competitive omni-
channel ecosystems, or reductions in operations may result in competitors with greatly improved financial resources, improved
access to merchandise, greater market penetration and other improvements in their competitive positions. Such business
combinations or alliances could allow these companies to provide a wider variety of products and services at competitive prices,
which could adversely affect our financial performance.
General or macro-economic factors, both domestically and internationally, may materially adversely affect our financial
performance.
General economic conditions and other economic factors, globally or in one or more of the markets we serve, may adversely
affect our financial performance. Higher interest rates, lower or higher prices of petroleum products, including crude oil,
natural gas, gasoline, and diesel fuel, higher costs for electricity and other energy, weakness in the housing market, inflation,
deflation, increased costs of essential services, such as medical care and utilities, higher levels of unemployment, decreases in
consumer disposable income, unavailability of consumer credit, higher consumer debt levels, changes in consumer spending
and shopping patterns, fluctuations in currency exchange rates, higher tax rates, imposition of new taxes or other changes in tax
laws, changes in healthcare laws, other regulatory changes, the imposition of tariffs or other measures that create barriers to or
increase the costs associated with international trade, overall economic slowdown or recession and other economic factors in
the U.S. or in any of the other markets in which we operate could adversely affect consumer demand for the products and
services we sell in the U.S. or such other markets, change the mix of products we sell to one with a lower average gross margin,
cause a slowdown in discretionary purchases of goods, adversely affect our net sales and result in slower inventory turnover and
greater markdowns of inventory, or otherwise materially adversely affect our operations and operating results and could result
in impairment charges to intangible assets, goodwill or other long-lived assets.
In addition, the economic factors listed above, any other economic factors or circumstances resulting in higher transportation,
labor, insurance or healthcare costs or commodity prices, and other economic factors in the U.S. and other countries in which
we operate can increase our cost of sales and operating, selling, general and administrative expenses and otherwise materially
adversely affect our operations and operating results.
The economic factors that affect our operations may also adversely affect the operations of our suppliers, which can result in an
increase in the cost to us of the goods we sell to our customers or, in more extreme cases, in certain suppliers not producing
goods in the volume typically available to us for sale.
The performance of strategic alliances and other business relationships to support the expansion of our business could
materially adversely affect our financial performance.
We may enter into strategic alliances and other business relationships in the countries in which we have existing operations or
in other markets to expand our business. These arrangements may not generate the level of sales we anticipate when entering
into the arrangement or may otherwise adversely impact our business and competitive position relative to the results we could
16

have achieved in the absence of such alliance. In addition, any investment we make in connection with a strategic alliance,
business relationship or in certain of our recently divested markets, could materially adversely affect our financial performance.
Operational Risks
The impact of the COVID-19 pandemic on our business, financial position and results of operations continues to be
unpredictable, and we may be unable to sustain our revenue growth rate in the future.
The impacts of the COVID-19 pandemic continue to be highly unpredictable and volatile in light of the potential for a
resurgence of infection rates or as a result of future mutations, variants, or related strains of the virus. Recent years have
demonstrated the widespread and varying impacts of the pandemic on certain business operations, demand for our products and
services, in-stock positions, costs of doing business, access to inventory, supply chain operations, the extent and duration of
measures to try to contain the virus (such as travel bans and restrictions, quarantines, shelter-in-place orders, business and
government shutdowns, and other restrictions on retailers), our ability to predict future performance, exposure to litigation, and
our financial performance, among other things.
Customer behaviors have changed rapidly during the course of the COVID-19 pandemic. In the event of a resurgence of
infections or future mutations, variants or related strains of the virus become prevalent, customer demand for certain products
may fluctuate and customer behaviors may change, which may challenge our ability to anticipate and/or adjust inventory levels
to meet that demand. These factors may result in higher out-of-stock positions in certain products, as well as delays in
delivering those products, and could impact inventory levels in the future.
Other factors and uncertainties include, but are not limited to: the severity and duration of the pandemic, including whether
there are additional outbreaks or spikes in the number of COVID-19 cases, future mutations or related strains of the virus in
areas in which we and our suppliers operate; further increased operational costs associated with operating during a global
pandemic; evolving macroeconomic factors, including general economic uncertainty, unemployment rates, and recessionary
pressures; unknown consequences on our business performance and initiatives stemming from the substantial investment of
time, capital and other resources to the pandemic response; the effectiveness and extent of administration of vaccinations and
medical treatments for COVID-19 or other variants; the pace of recovery when the pandemic subsides; and the long-term
impact of the COVID-19 pandemic on our business, including consumer behaviors. These risks and their impacts are difficult
to predict and could otherwise disrupt and adversely affect our operations and our financial performance.
The COVID-19 pandemic has led to increased revenue growth relative to historic trends, and has particularly accelerated our
eCommerce growth. These results, as well as those of other metrics such as net income and other financial and operating data,
may not be indicative of results for future periods. Once the impact of the COVID-19 pandemic subsides, particularly as
vaccines become more widely available, and customers return to work or school or are otherwise no longer subject to the
aforementioned containment directives and similar mandates, a failure by us to continue capitalizing on growth opportunities
may result in declining revenue and future operating results may fall below expectations.
To the extent that the COVID-19 pandemic continues to adversely affect the U.S. and the global economy, it may also heighten
other risks described in this section, including but not limited to those related to consumer behavior and expectations,
competition, our reputation, implementation of strategic initiatives, cybersecurity threats, payment-related risks, technology
systems disruption, supply chain disruptions, labor availability and cost, litigation, and regulatory requirements.
Natural disasters, climate change, geopolitical events, global health epidemics or pandemics and catastrophic events
could materially adversely affect our financial performance.
The occurrence of one or more natural disasters, such as hurricanes, tropical storms, floods, fires, earthquakes, tsunamis,
cyclones, typhoons; weather conditions such as major or extended winter storms, droughts and tornadoes, whether as a result of
climate change or otherwise; geopolitical events; global health epidemics or pandemics or other contagious outbreaks such as
the ongoing COVID-19 pandemic; and catastrophic events, such as war, civil unrest, terrorist attacks or other acts of violence,
including active shooter situations (such as those that have occurred in our U.S. stores), in countries in which we operate, in
which our suppliers are located, or in other areas of the world (such as in Ukraine where armed hostilities currently exist
between Ukraine and Russia) could adversely affect our operations and financial performance.
Such events could result in physical damage to, or the complete loss of, one or more of our properties, the closure of one or
more stores, clubs and distribution or fulfillment centers, limitations on store or club operating hours, the lack of an adequate
work force in a market, the inability of customers and associates to reach or have transportation to our stores and clubs affected
by such events, the evacuation of the populace from areas in which our stores, clubs and distribution and fulfillment centers are
located, the unavailability of our digital platforms to our customers, changes in the purchasing patterns of consumers (including
the frequency of visits by consumers to physical retail locations, whether as a result of limitations on large gatherings, travel
and movement limitations or otherwise) and in consumers' disposable income, the temporary or long-term disruption in the
supply of products from some suppliers, the disruption in the transport of goods from overseas, the disruption or delay in the
delivery of goods to our distribution and fulfillment centers or stores within a country in which we are operating, the reduction
in the availability of products in our stores, increases in the costs of procuring products as a result of either reduced availability
17
or economic sanctions, increased transportation costs (whether due to fuel prices, fuel supply, or otherwise), the disruption
(whether directly or indirectly) of critical infrastructure systems, banking systems, utility services or energy availability to our
stores, clubs and our facilities, and the disruption in our communications with our stores, clubs and our other facilities.
Furthermore, the long-term impacts of climate change, whether involving physical risks (such as extreme weather conditions,
drought, or rising sea levels) or transition risks (such as regulatory or technology changes) are expected to be widespread and
unpredictable. Certain impacts of physical risk may include: temperature changes that increase the heating and cooling costs at
stores, clubs, and distribution or fulfillment centers; extreme weather patterns that affect the production or sourcing of certain
commodities; flooding and extreme storms that damage or destroy our buildings and inventory; and heat and extreme weather
events that cause long-term disruption or threats to the habitability of the communities in which Walmart operates. Relative to
transition risk, certain impacts may include: changes in energy and commodity prices driven by climate-related weather events;
prolonged climate-related events affecting macroeconomic conditions with related effects on consumer spending and
confidence; stakeholder perception of our engagement in climate-related policies; and new regulatory requirements resulting in
higher compliance risk and operational costs.
We bear the risk of losses incurred as a result of physical damage to, or destruction of, any stores, clubs and distribution or
fulfillment centers, loss or spoilage of inventory and business interruption caused by such events. These events and their
impacts could otherwise disrupt and adversely affect our operations and could materially adversely affect our financial
performance.
Risks associated with our suppliers could materially adversely affect our financial performance.
The products we sell are sourced from a wide variety of domestic and international suppliers. Global sourcing of many of the
products we sell is an important factor in our financial performance. We expect our suppliers to comply with applicable laws,
including labor, safety, anti-corruption and environmental laws, and to otherwise meet our required supplier standards of
conduct. Our ability to find qualified suppliers who uphold our standards, and to access products in a timely and efficient
manner and in the large volumes we may demand, is a significant challenge, especially with respect to suppliers located and
goods sourced outside the U.S.
Political and economic instability, as well as other impactful events and circumstances in the countries in which our suppliers
and their manufacturers are located (such as the ongoing COVID-19 pandemic), the financial instability of suppliers, suppliers'
failure to meet our terms and conditions or our supplier standards (including our responsible sourcing standards), labor
problems experienced by our suppliers and their manufacturers, the availability of raw materials to suppliers, merchandise
safety and quality issues, disruption or delay in the transportation of merchandise from the suppliers and manufacturers to our
stores, clubs, and other facilities, including as a result of labor slowdowns at any port at which a material amount of
merchandise we purchase enters into the markets in which we operate, currency exchange rates, transport availability and cost,
transport security, inflation and other factors relating to the suppliers and the countries in which they are located are beyond our
control.
In addition, the U.S. foreign trade policies, tariffs and other impositions on imported goods, trade sanctions imposed on certain
countries and entities, the limitation on the importation of certain types of goods or of goods containing certain materials from
other countries and other factors relating to foreign trade are beyond our control. These and other factors affecting our
suppliers and our access to products could adversely affect our financial performance.
If the products we sell are not safe or otherwise fail to meet our customers' expectations, we could lose customers, incur
liability for any injuries suffered by customers using or consuming a product we sell or otherwise experience a material
impact to our brand, reputation and financial performance. We are also subject to reputational and other risks related
to third-party sales on our digital platforms.
Our customers count on us to provide them with safe products. Concerns regarding the safety of food and non-food products
that we source from our suppliers or that we prepare and then sell could cause customers to avoid purchasing certain products
from us, or to seek alternative sources of supply for all of their food and non-food needs, even if the basis for the concern is
outside of our control. Any lost confidence on the part of our customers would be difficult and costly to reestablish and such
products also expose us to product liability or food safety claims. As such, any issue regarding the safety of any food or non-
food items we sell, regardless of the cause, could adversely affect our brand, reputation and financial performance. In addition,
third-parties sell goods on some of our digital platforms, which we refer to as marketplace transactions. Whether laws related
to these marketplace transactions apply to us is currently unsettled and any unfavorable changes could expose us to loss of
sales, reduction in transactions and deterioration of our competitive position. In addition, we may face reputational, financial
and other risks, including liability, for third-party sales of goods that are controversial, counterfeit, pirated, or stolen, or
otherwise fail to comply with applicable law or the proprietary rights of others. Although we impose contractual terms on
sellers that are intended to prohibit sales of certain type of products, we may not be able to detect, enforce, or collect sufficient
damages for breaches of such agreements. Any of these events could have a material adverse impact on our business and results
of operations and impede the execution of our eCommerce growth and flywheel strategy.
18

We rely extensively on information systems to process transactions, summarize results and manage our business.
Disruptions in our systems could harm our ability to conduct our operations.
Given the number of individual transactions we have each year, it is crucial that we maintain uninterrupted operation of our
business-critical information systems. Our information systems are subject to damage or interruption from power outages,
computer and telecommunications failures, computer viruses, worms, other malicious computer programs, denial-of-service
attacks, security incidents and breaches (through cyberattacks, which may be from cybercriminals or sophisticated state-
sponsored threat actors), catastrophic events such as fires, major or extended winter storms, tornadoes, earthquakes and
hurricanes, usage errors by our associates or contractors, civil or political unrest, or armed hostilities. Our information systems
are essential to our business operations, including the processing of transactions, management of our associates, facilities,
logistics, inventories, physical stores and clubs and our online operations. Our information systems are not fully redundant and
our disaster recovery planning cannot account for all eventualities. If our systems are damaged, breached, attacked, or cease to
function properly, we may have to make a significant investment to repair or replace them, and may experience loss or
corruption of critical data as well as suffer interruptions in our business operations in the interim. Any interruption to our
information systems may have a material adverse effect on our business or results of operations. In addition, we frequently
update our information technology hardware, software, processes and systems. The risk of system disruption is increased when
significant system changes are undertaken. If we fail to timely integrate and update our information systems and processes, we
may fail to realize the cost savings or operational benefits anticipated to be derived from these initiatives.
If the technology-based systems that give our customers the ability to shop with us online do not function effectively, our
operating results, as well as our ability to grow our omni-channel business globally, could be materially adversely
affected.
Increasingly, customers are using computers, tablets, and smart phones to shop with us and with our competitors and to do
comparison shopping. We use social media, online advertising, and email to interact with our customers and as a means to
enhance their shopping experience. As a part of our omni-channel sales strategy, we offer various pickup, delivery and
shipping programs including options where many products available for purchase online can be picked up by the customer or
member at a local Walmart store or Sam's Club, which provides additional customer traffic at such stores and clubs. Omni-
channel retailing is a rapidly evolving part of the retail industry and of our operations around the world. We must anticipate and
meet our customers' changing expectations while adjusting for technology investments and developments in our competitors'
operations through focusing on the building and delivery of a seamless shopping experience across all channels by each
operating segment. Any failure on our part to provide attractive, user-friendly secure digital platforms that offer a wide
assortment of merchandise at competitive prices and with low cost and rapid delivery options and that continually meet the
changing expectations of online shoppers and developments in online and digital platform merchandising and related
technology could place us at a competitive disadvantage, result in the loss of eCommerce and other sales, harm our reputation
with customers, have a material adverse impact on the growth of our eCommerce business globally and have a material adverse
impact on our business and results of operations.
Our digital platforms, which are increasingly important to our business and continue to grow in complexity and scope, and the
systems on which they run, including those applications and systems in our acquired eCommerce businesses, are regularly
subject to cyberattacks. Those attacks involve attempts to gain unauthorized access to our eCommerce websites (including
marketplace platforms) or mobile commerce applications to obtain and misuse customers' or members' information including
payment information and related risks discussed in this Item 1A. Such attacks, if successful, in addition to potential data misuse
and/or loss, may also create denials of service or otherwise disable, degrade or sabotage one or more of our digital platforms or
otherwise significantly disrupt our customers' and members' shopping experience, our supply chain integrity and continuity, and
our ability to efficiently operate our business. If we are unable to maintain the security of our digital platforms and keep them
operating within acceptable parameters, we could suffer loss of sales, reductions in transactions, reputational damage and
deterioration of our competitive position and incur liability for any damage to customers or others whose personal or
confidential information is unlawfully obtained and misused, any of which events could have a material adverse impact on our
business and results of operations and impede the execution of our strategy for the growth of our business.
Any failure to maintain the privacy or security of the information relating to our company, customers, members,
associates and vendors, whether as a result of cyberattacks on our information systems or otherwise, could damage our
reputation, result in litigation or other legal actions against us, cause us to incur substantial additional costs, and
materially adversely affect our business and operating results.
Like most retailers, we receive and store in our information systems personal information about our customers and members,
and we receive and store information concerning our associates and vendors. Some of that information is stored digitally in
connection with the digital platforms that we use to conduct and facilitate our various businesses. In addition, we and our third-
party service providers store and maintain health-related personal information, pharmacy, and medical records in connection
with our health and wellness and pharmacy business. We also utilize third-party service providers for a variety of reasons,
including, without limitation, for digital storage technology, content delivery to customers and members, back-office support,
and other functions. Such providers may have access to information we hold about our customers, members, associates or
19
vendors. In addition, our eCommerce operations depend upon the secure transmission of confidential information over public
networks, including information permitting cashless payments.
Cyber threats are rapidly evolving and those threats and the means for obtaining access to information in digital and other
storage media are becoming increasingly sophisticated and frequent. Attacks against information systems and devices, whether
our own or those of our third-party service providers, create risk of cybersecurity incidents, including ransomware, malware,
phishing incidents. We expect to continue to experience such attempted attacks in the future. Cyberattacks and threat actors can
be sponsored by particular countries or sophisticated criminal organizations or be the work of hackers with a wide range of
motives and expertise. We and the businesses with which we interact have experienced and continue to experience threats to
data and systems, including by perpetrators of random or targeted malicious cyberattacks, computer viruses, phishing incidents,
worms, bot attacks, ransomware or other destructive or disruptive software and attempts to misappropriate customer
information, including credit card and payment information, and cause system failures and disruptions. Mitigation and
remediation recommendations continue to evolve, and addressing vulnerabilities is a priority for us. The increased use of
remote work infrastructure due to the COVID-19 pandemic has also increased the possible attack surfaces. Some of our systems
and third-party service providers' systems have experienced security incidents or breaches and although they did not have a
material adverse effect on our operating results, there can be no assurance of a similar result in the future.
Associate error or malfeasance, faulty password management, social engineering or other vulnerabilities and irregularities may
also result in a defeat of our or our third-party service providers' security measures and a compromise or breach of our or their
information systems. Moreover, hardware, software or applications we use may have inherent vulnerabilities or defects of
design, manufacture or operations or could be inadvertently or intentionally implemented or used in a manner that could
compromise information security.
Any compromise of our data security systems or of those of businesses with which we interact, which results in confidential
information being accessed, obtained, damaged, disclosed, destroyed, modified, lost or used by unauthorized persons could
harm our reputation and expose us to regulatory actions (including, with respect to health information, liability under the Health
Insurance Portability and Accountability Act of 1996, or "HIPAA"), customer attrition, remediation expenses, and claims from
customers, members, associates, vendors, financial institutions, payment card networks and other persons, any of which could
materially and adversely affect our business operations, financial position and results of operations. Because the techniques
used to obtain unauthorized access, disable or degrade service, or sabotage systems change frequently and may not immediately
produce signs of a compromise, we may be unable to anticipate these techniques or to implement adequate preventative
measures and we or our third-party service providers may not discover any security event, breach, vulnerability or compromise
of information for a significant period of time after the security incident occurs. To the extent that any cyberattack, ransomware
or incursion in our or one of our third-party service provider's information systems results in the loss, damage, misappropriation
or other compromise of information, we may be materially adversely affected by claims from customers, financial institutions,
regulatory authorities, payment card networks and others.
Our compliance programs, information technology, and enterprise risk management efforts cannot eliminate all systemic risk.
Disruptions in our systems caused by security incidents, breaches or cyberattacks – including attacks on those parties we do
business with (such as strategic partners, suppliers, banks, or utility companies) – could harm our ability to conduct our
operations, which may have a material effect on us, may result in losses that could have a material adverse effect on our
financial position or results of operations, or may have a cascading effect that adversely impacts our partners, third-party
service providers, customers, financial services firms, and other third parties that we interact with on a regular basis.
In addition, such security-related events could be widely publicized and could materially adversely affect our reputation with
our customers, members, associates, vendors and shareholders, could harm our competitive position particularly with respect to
our eCommerce operations, and could result in a material reduction in our net sales in our eCommerce operations, as well as in
our stores thereby materially adversely affecting our operations, net sales, results of operations, financial position, cash flows
and liquidity. Such events could also result in the release to the public of confidential information about our operations and
financial position and performance and could result in litigation or other legal actions against us or the imposition of penalties,
fines, fees or liabilities, which may not be covered by our insurance policies. Moreover, a security compromise or ransomware
event could require us to devote significant management resources to address the problems created by the issue and to expend
significant additional resources to upgrade further the security measures we employ to guard personal and confidential
information against cyberattacks and other attempts to access or otherwise compromise such information and could result in a
disruption of our operations, particularly our digital operations.
We accept payments using a variety of methods, including cash, checks, credit and debit cards, and our private label credit
cards and gift cards, and we may offer new payment options over time, which may have information security risk implications.
As a retailer accepting debit and credit cards for payment, we are subject to various industry data protection standards and
protocols, such as payment network security operating guidelines and the Payment Card Industry Data Security Standard. We
cannot be certain that the security measures we maintain to protect all of our information technology systems are able to
prevent, contain or detect cyberattacks, cyberterrorism, security incidents, breaches, or other compromises from known
malware or ransomware or other threats that may be developed in the future. In certain circumstances, our contracts with
20
payment card processors and payment card networks (such as Visa, Mastercard, American Express and Discover) generally
require us to adhere to payment card network rules which could make us liable to payment card issuers and others if
information in connection with payment cards and payment card transactions that we process is compromised, which liabilities
could be substantial.
Additionally, through various financial service partners, we offer money transfers, digital payment platforms, bill payment,
money orders, check cashing, prepaid access, co-branded credits cards, installment lending, and earned wage access. These
products and services require us to comply with legal and regulatory requirements, including global anti-money laundering and
sanctions laws and regulations as well as international, federal and state consumer financial laws and regulations. Failure to
comply with these laws and regulations could result in fines, sanctions, penalties and harm to our reputation.
The Company also has compliance obligations associated with privacy laws enacted to protect and regulate the collection, use,
retention, disclosure and transfer of personal information, which include liability for security and privacy breaches. Among
other obligations, breaches may trigger obligations under federal and state laws to notify affected individuals, government
agencies and the media. Consequently, cybersecurity attacks that cause a data breach could subject us to fines, sanctions and
other legal liability and harm our reputation.
Changes in the results of our health and wellness business could adversely affect our overall results of operations, cash
flows and liquidity.
Walmart has retail pharmacy operations in our Walmart U.S. and Sam's Club segments, as well as the recent addition of
Walmart Health locations in a number of states which offer medical, dental, optometry, immunizations, and other health
services. A large majority of our retail pharmacy net sales are generated by filling prescriptions for which we receive payment
through established contractual relationships with third-party payers and payment administrators, such as private insurers,
governmental agencies and pharmacy benefit managers ("PBMs").
These operations are subject to numerous risks, including: reductions in the third-party reimbursement rates for drugs; changes
in our payer mix (i.e., shifts in the relative distribution of our pharmacy customers across drug insurance plans and programs
toward plans and programs with less favorable reimbursement terms); changes in third-party payer drug formularies (i.e., the
schedule of prescription drugs approved for reimbursement or which otherwise receive preferential coverage treatment); growth
in, and our participation in or exclusion from, pharmacy payer network arrangements including exclusive and preferred
pharmacy network arrangements operated by PBMs and/or any insurance plan or program; increases in the prices we pay for
brand name and generic prescription drugs we sell; increases in the administrative burdens associated with seeking third-party
reimbursement; changes in the frequency with which new brand name pharmaceuticals become available to consumers;
introduction of lower cost generic drugs as substitutes for existing brand name drugs for which there was no prior generic drug
competition; changes in drug mix (i.e., the relative distribution of drugs customers purchase at our pharmacies between brands
and generics); changes in the health insurance market generally; changes in the scope of or the elimination of Medicare Part D
or Medicaid drug programs; increased competition from other retail pharmacy operations including competitors offering online
retail pharmacy options with or without home delivery options; further consolidation and strategic alliances among third-party
payers, PBMs or purchasers of drugs; overall economic conditions and the ability of our pharmacy customers to pay for drugs
prescribed for them to the extent the costs are not reimbursed by a third-party; failure to meet any performance or incentive
thresholds to which our level of third-party reimbursement may be subject; changes in laws or regulations or the practices of
third-party payers and PBMs related to the use of third-party financial assistance to assist our pharmacy customers with paying
for drugs prescribed for them; and any additional changes in the regulatory environment for the retail pharmacy industry and
the pharmaceutical industry, including as a result of restrictions on the further implementation of or the repeal of the Patient
Protection and Affordable Care Act or the enactment and implementation of a law replacing such act, and other changes in
laws, rules and regulations that affect our retail pharmacy business.
If the supply of certain pharmaceuticals provided by one or more of our vendors were to be disrupted for any reason, our
pharmacy operations could be severely affected until at least such time as we could obtain a new supplier for such
pharmaceuticals. Any such disruption could cause reputational damage and result in a significant number of our pharmacy
customers transferring their prescriptions to other pharmacies.
One or a combination of such factors may adversely affect the volumes of brand name and generic pharmaceuticals we sell, our
cost of sales associated with our retail pharmacy operations, and the net sales and gross margin of those operations or result in
the loss of cross-store or cross-club selling opportunities and, in turn, adversely affect our overall net sales, other results of
operations, cash flows and liquidity.
Our failure to attract and retain qualified associates, increases in wage and benefit costs, changes in laws and other
labor issues could materially adversely affect our financial performance.
Our ability to continue to conduct and expand our operations depends on our ability to attract and retain a large and growing
number of qualified associates globally. Our ability to meet our labor needs, including our ability to find qualified personnel to
fill positions that become vacant at our existing stores, clubs, distribution and fulfillment centers and corporate offices, while
21

controlling our associate wage and related labor costs, is generally subject to numerous external factors, including the
availability of a sufficient number of qualified persons in the work force of the markets in which we operate, unemployment
levels within those markets, prevailing wage rates, changing demographics, health and other insurance costs and adoption of
new or revised employment and labor laws and regulations. Additionally, our ability to successfully execute organizational
changes, including management transitions within the Company's senior leadership, and to effectively motivate and retain
associates are critical to our business success. If we are unable to locate, attract or retain qualified personnel, or manage
leadership transition successfully, the quality of service we provide to our customers may decrease and our financial
performance may be adversely affected.
In addition, if our costs of labor or related costs increase for other reasons or if new or revised labor laws, rules or regulations or
healthcare laws are adopted or implemented that further increase our labor costs, our financial performance could be materially
adversely affected.
Financial Risks
Failure to meet market expectations for our financial performance could adversely affect the market price and volatility
of our stock.
We believe that the price of our stock generally reflects high market expectations for our future operating results. Any failure
to meet or delay in meeting these expectations, including our consolidated net sales, consolidated operating income, capital
expenditures, comparable store and club sales growth rates, eCommerce growth rates, gross margin, or earnings and adjusted
earnings per share could cause the market price of our stock to decline, as could changes in our dividend or stock repurchase
programs or policies, changes in our effective tax rates, changes in our financial estimates and recommendations by securities
analysts or, failure of Walmart's performance to compare favorably to that of other retailers may have a negative effect on the
price of our stock.
Fluctuations in foreign exchange rates may materially adversely affect our financial performance and our reported
results of operations.
Our operations in countries other than the U.S. are conducted primarily in the local currencies of those countries. Our
Consolidated Financial Statements are denominated in U.S. dollars, and to prepare those financial statements we must translate
the amounts of the assets, liabilities, net sales, other revenues and expenses of our operations outside of the U.S. from local
currencies into U.S. dollars using exchange rates for the current period. In recent years, fluctuations in currency exchange rates
that were unfavorable have had adverse effects on our reported results of operations.
As a result of such translations, fluctuations in currency exchange rates from period-to-period that are unfavorable to us may
also result in our Consolidated Financial Statements reflecting significant adverse period-over-period changes in our financial
performance or reflecting a period-over-period improvement in our financial performance that is not as robust as it would be
without such fluctuations in the currency exchange rates. Such unfavorable currency exchange rate fluctuations will adversely
affect the reported performance of our Walmart International operating segment and have a corresponding adverse effect on our
reported consolidated results of operations.
We may pay for products we purchase for sale in our stores and clubs around the world with a currency other than the local
currency of the country in which the goods will be sold. When we must acquire the currency to pay for such products and the
exchange rates for the payment currency fluctuate in a manner unfavorable to us, our cost of sales may increase and we may be
unable or unwilling to change the prices at which we sell those goods to address that increase in our costs, with a corresponding
adverse effect on our gross profit. Consequently, unfavorable fluctuations in currency exchange rates have and may continue to
adversely affect our results of operations.
Legal, Tax, Regulatory, Compliance, Reputational and Other Risks
Our international operations subject us to legislative, judicial, accounting, legal, regulatory, tax, political and economic
risks and conditions specific to the countries or regions in which we operate, which could materially adversely affect our
business or financial performance.
In addition to our U.S. operations, we operate our retail business in Africa, Canada, Central America, Chile, China, India and
Mexico.
During fiscal 2022, our Walmart International operations generated approximately 18% of our consolidated net sales. Walmart
International's operations in various countries also source goods and services from other countries. Our future operating results
in these countries could be negatively affected by a variety of factors, most of which are beyond our control. These factors
include political conditions, including political instability, local and global economic conditions, legal and regulatory
constraints (such as regulation of product and service offerings including regulatory restrictions (such as foreign ownership
restrictions) on eCommerce and retail operations in international markets, such as India), restrictive governmental actions (such
as trade protection measures), antitrust and competition law regulatory matters (such as the competition investigations currently
22
underway in Mexico related to our subsidiary Wal-Mart de Mexico, in Canada related to our subsidiary Wal-Mart Canada and
competition proceedings in India related to our Flipkart subsidiary), local product safety and environmental laws, tax
regulations, local labor laws, anti-money laundering laws and regulations, trade policies, currency regulations, laws and
regulations regarding consumer and data protection, and other matters in any of the countries or regions in which we operate,
now or in the future.
The economies of some of the countries in which we have operations have in the past suffered from high rates of inflation and
currency devaluations, which, if they occurred again, could adversely affect our financial performance. Other factors which
may impact our international operations include foreign trade, monetary and fiscal policies of the U.S. and of other countries,
laws, regulations and other activities of foreign governments, agencies and similar organizations, and risks associated with
having numerous facilities located in countries that have historically been less stable than the U.S. Additional risks inherent in
our international operations generally include, among others, the costs and difficulties of managing international operations,
adverse tax consequences and greater difficulty in enforcing intellectual property rights in countries other than the U.S. The
various risks inherent in doing business in the U.S. generally also exist when doing business outside of the U.S., and may be
exaggerated by the difficulty of doing business in numerous sovereign jurisdictions due to differences in culture, laws and
regulations.
In foreign countries in which we have operations, a risk exists that our associates, contractors or agents could, in contravention
of our policies, engage in business practices prohibited by U.S. laws and regulations applicable to us, such as the Foreign
Corrupt Practices Act or the laws and regulations of other countries. We maintain a global policy prohibiting such business
practices and have in place a global anti-corruption compliance program designed to ensure compliance with these laws and
regulations. Nevertheless, we remain subject to the risk that one or more of our associates, contractors or agents, including
those based in or from countries where practices that violate such U.S. laws and regulations or the laws and regulations of other
countries may be customary, will engage in business practices that are prohibited by our policies, circumvent our compliance
programs and, by doing so, violate such laws and regulations. Any such violations, even if prohibited by our internal policies,
could adversely affect our business or financial performance and our reputation.
Changes in tax and trade laws and regulations could materially adversely affect our financial performance.
In fiscal 2022, our Walmart U.S. and Sam's Club operating segments generated approximately 82% of our consolidated net
sales. Significant changes in tax and trade policies, including tariffs and government regulations affecting trade between the
U.S. and other countries where we source many of the products we sell in our stores and clubs could have an adverse effect on
our business and financial performance. A significant portion of the general merchandise we sell in our U.S. stores and clubs is
manufactured in other countries. Any such actions including the imposition of further tariffs on imports could increase the cost
to us of such merchandise (whether imported directly or indirectly) and cause increases in the prices at which we sell such
merchandise to our customers, which could materially adversely affect the financial performance of our U.S. operations and our
business.
We are subject to income taxes and other taxes in both the U.S. and the foreign jurisdictions in which we currently operate or
have historically operated. The determination of our worldwide provision for income taxes and current and deferred tax assets
and liabilities requires judgment and estimation. Our income taxes could be materially adversely affected by earnings being
lower than anticipated in jurisdictions that have lower statutory tax rates and higher than anticipated in jurisdictions that have
higher statutory tax rates, by changes in the valuation of our deferred tax assets and liabilities, or by changes in worldwide tax
laws, tax rates, regulations or accounting principles.
We are also exposed to future tax legislation, as well as the issuance of future regulations and changes in administrative
interpretations of existing tax laws, any of which can impact our current and future years' tax provision. The effect of such
changes in tax law could have a material effect on our business, financial position and results of operations. In the U.S., the Tax
Cuts and Jobs Act of 2017 (the "Tax Act") significantly changed federal income tax laws that affect U.S. corporations. As
further guidance is issued by the U.S. Treasury Department, the IRS, and other standard-setting bodies, any resulting changes in
our estimates will be treated in accordance with the relevant accounting guidance. Compliance with the Tax Act and any other
new tax rules, regulations, guidance, and interpretations, including collecting information not regularly produced by the
Company or unexpected changes in our estimates, may require us to incur additional costs and could affect our results of
operations.
In addition, legislatures and taxing authorities in many jurisdictions in which we operate may enact changes to their tax rules.
These changes could include modifications that have temporary effect and more permanent changes. The impact of these
potential new rules as well as any other changes in domestic and international tax rules and regulations could have a material
effect on our effective tax rate.
Furthermore, we are subject to regular review and audit by both domestic and foreign tax authorities as well as subject to the
prospective and retrospective effects of changing tax regulations and legislation. Although we believe our tax estimates are
reasonable, the ultimate tax outcome may materially differ from the tax amounts recorded in our Consolidated Financial
23
Statements and may materially affect our income tax provision, net income, or cash flows in the period or periods for which
such determination and settlement is made.
Changes in and/or failure to comply with other laws, regulations, and interpretations of such laws and regulations
specific to the businesses and jurisdictions in which we operate could materially adversely affect our reputation, market
position, or our business and financial performance.
We operate in complex regulated environments in the U.S. and in the other countries in which we operate and could be
adversely affected by changes to existing legal requirements including the related interpretations and enforcement practices,
new legal requirements and/or any failure to comply with applicable regulations.
Our operations in the U.S. are subject to numerous federal, state and local regulations including licensing and other
requirements and reimbursement arrangements affecting our health and wellness operations. The laws and regulations to which
we are subject include, but are not limited to: federal and state registration and regulation of pharmacies; dispensing and sale of
controlled substances and products containing pseudoephedrine; applicable governmental payer regulations including Medicare
and Medicaid; data privacy and security laws and regulations including the Health Insurance Portability and Accountability Act
and the Affordable Care Act; laws and regulations relating to the protection of the environment and health and safety matters,
including those governing exposure to, and the management and disposal of, hazardous substances; regulations regarding food
and drug safety including those of the U.S. Food and Drug Administration (the "FDA") and the Drug Enforcement
Administration (the "DEA"); trade regulations including those of the U.S. Federal Trade Commission, the U.S. Department of
the Treasury, and consumer protection and safety regulations including those of the Consumer Product Safety Commission, as
well as state regulatory authorities, governing the availability, sale, advertisement and promotion of products we sell and the
financial services we offer (including through our digital channels and stores and clubs as well as our previously announced
fintech joint venture); anti-kickback laws; anti-money laundering laws; consumer financial protection laws; the Office of
Foreign Assets Control regulations; false claims laws; patient inducement regulations; and federal and state laws governing
health care fraud and abuse, quality and standards of medical equipment, and the qualifications and practice of the professions
of medical, pharmacy, optical care and health care services.
For example, in the U.S., the DEA and various other regulatory authorities regulate the purchase, distribution, maintenance and
dispensing of pharmaceuticals and controlled substances. We are required to hold valid DEA and state-level licenses, meet
various security and operating standards and comply with the federal and various state controlled substance acts and related
regulations governing the sale, dispensing, disposal and holding of controlled substances. The DEA, the FDA and state
regulatory authorities have broad enforcement powers, including the ability to seize or recall products and impose significant
criminal, civil and administrative sanctions for violations of these laws and regulations. In addition, other health-related
legislation at the federal and state level may have an adverse effect on our business or require us to modify certain aspects of
our operations. Also, upon the successful completion of the previously announced pending acquisitions by our fintech joint
venture, there may be an increased degree of scrutiny by financial regulatory authorities over the newly acquired fintech related
businesses, which may result in higher operational costs and an increased possibility for fines and penalties if there is non-
compliance with the applicable laws and regulations.
We are also governed by foreign, national and state laws and regulations of general applicability, including laws and regulations
related to working conditions, health and safety, equal employment opportunity, employee benefit and other labor and
employment matters, laws and regulations related to competition and antitrust matters, and health and wellness related
regulations for our pharmacy operations outside of the U.S. Increasing governmental and societal attention to ESG matters,
including expanding mandatory and voluntary reporting diligence, and disclosure topics such as climate change, sustainability
(including with respect to our supply chain), natural resources, waste reduction, energy, human capital, and risk oversight could
expand the nature, scope, and complexity of matters that we are required to control, assess, and report. In addition, certain
financial services we offer or make available are subject to legal and regulatory requirements, including those intended to help
detect and prevent money laundering, fraud and other illicit activity as well as consumer financial protections laws and U.S.
sanctions. We are also subject to data privacy and protection laws regulating the collection, use, retention, disclosure, transfer
and processing of personal information, such as the California Consumer Privacy Act ("CCPA"), which was significantly
modified by the California Privacy Rights Act ("CPRA"), new comprehensive privacy legislation passed in 2021 in Virginia
and Colorado, as well as the European Union's General Data Protection Regulation ("GDPR") and China's Personal Information
Protection Act. The potential effects of these laws are far-reaching and may require us to modify our data processing practices
and policies and to incur substantial costs and expenses to comply. In the case of non-compliance with a material provision of
the GDPR (such as non-adherence to the core principles of processing personal data), regulators have the authority to levy a
fine in an amount that is up to the greater of €20 million or 4% of global annual turnover in the prior year. These administrative
fines are discretionary and based, in each case, on a multi-factored approach. Residents in jurisdictions with comprehensive
privacy laws have expanded rights to access, correct and require deletion of their personal information, opt out of certain
personal information sharing and receive detailed information about how their personal information is used. The CCPA and
CPRA provide for civil penalties for violations, as well as a private right of action for data breaches. Furthermore, our
marketing and customer engagement activities are subject to communications privacy laws such as the Telephone Consumer
24
Protection Act. We may be subjected to penalties and other consequences for noncompliance, including changing some portions
of our business. Even an unsuccessful challenge by customer or regulatory authorities of our activities could result in adverse
publicity and could require a costly response from and defense by us.
The impact of new laws, regulations and policies and the related interpretations, as well as changes in enforcement practices or
regulatory scrutiny generally cannot be predicted, and changes in applicable laws, regulations and policies and the related
interpretations and enforcement practices may require extensive system and operational changes, be difficult to implement,
increase our operating costs, require significant capital expenditures, or adversely impact the cost or attractiveness of the
products or services we offer, or result in adverse publicity and harm our reputation. If we fail to respond adequately to
changes, including by implementing strategic and operational initiatives, or do not respond as effectively as our competitors,
our business, operations, and financial performance may be adversely affected.
While we strive to adhere our practices and procedures to these laws, they are subject to evolving regulations, interpretations,
enforcement priorities of regulatory authorities, and regulator discretion. The regulatory, political, and media scrutiny we face,
which may continue, amplifies these risks. We may face audits or investigations by one or more government agencies relating
to our compliance with applicable laws and regulations. To the extent a regulator or court disagrees with our interpretation of
these laws and determines that our practices are not in compliance with applicable laws and regulations, we could be subject to
civil and criminal penalties that could adversely affect the continued operation of our businesses, including: suspension of
payments from government programs; loss of required government certifications; loss of authorizations to participate in or
exclusion from government programs, including the Medicare and Medicaid programs in the U.S.; loss of licenses; termination
from contractual relationships, including those with our drug suppliers and third-party payers; and significant fines or monetary
damages and/or criminal and civil penalties. Failure to comply with applicable legal or regulatory requirements in the U.S. or
in any of the countries in which we operate could result in significant legal and financial exposure, damage to our reputation,
and have a material adverse effect on our business operations, financial position and results of operations.
We are subject to risks related to litigation and other legal proceedings that may materially adversely affect our results
of operations, financial position and liquidity.
We operate in a highly regulated and litigious environment. We are involved in legal proceedings, including litigation,
arbitration and other claims, and investigations, inspections, audits, claims, inquiries and similar actions by pharmacy,
healthcare, tax, environmental and other governmental authorities. We may also have indemnification obligations for legal
commitments of certain businesses we have divested. Legal proceedings, in general, and securities, derivative action and class
action and multi-district litigation, in particular, can be expensive and disruptive. Some of these suits may purport or may be
determined to be class actions and/or involve parties seeking large and/or indeterminate amounts, including punitive or
exemplary damages, and may remain unresolved for several years. For example, we are currently a defendant in a number of
cases containing class or collective-action allegations, or both, in which the plaintiffs have brought claims under federal and
state wage and hour laws, as well as a number of cases containing class-action allegations in which the plaintiffs have brought
claims under federal and state consumer laws.
The Company has also been responding to subpoenas, information requests and investigations from governmental entities
related to nationwide controlled substance dispensing and distribution practices involving opioids and is also a defendant in
numerous litigation proceedings related to opioids, including the consolidated multidistrict litigation entitled In re National
Prescription Opiate Litigation (MDL No. 2804) currently pending in the U.S. District Court for the Northern District of Ohio.
Similar cases that name the Company have also been filed in state courts by state, local and tribal governments, health care
providers and other plaintiffs. Plaintiffs are seeking compensatory and punitive damages, as well as injunctive relief including
abatement. On October 22, 2020, the Company filed a declaratory judgment action in the U.S. District Court for the Eastern
District of Texas against the U.S. Department of Justice (the "DOJ") and the U.S. Drug Enforcement Administration, asking a
federal court to clarify the roles and responsibilities of pharmacists and pharmacies as to the dispensing and distribution of
opioids under the Controlled Substances Act (the "CSA"). The Company's action was dismissed. The Company appealed this
decision to the Fifth Circuit. On December 22, 2021, the Fifth Circuit affirmed the dismissal of the action. On December 22,
2020, the DOJ filed a civil complaint against the Company in the U.S. District Court for the District of Delaware alleging that
the Company unlawfully dispensed controlled substances from its pharmacies and unlawfully distributed controlled substances
to those pharmacies in violation of the CSA. The DOJ is seeking civil penalties and injunctive relief. The Company filed a
motion to dismiss the DOJ complaint on February 22, 2021. Since that time, the District Court stayed further proceedings in the
DOJ complaint pending the decision of the United States Supreme Court in two other cases interpreting the CSA, which have
been consolidated into Ruan v. United States, 142 S. Ct. 457 (2021).
In addition, the Company is the subject of a consolidated securities class action alleging violations of the federal securities laws
regarding the Company's disclosures with respect to opioids filed in the U.S. District Court for the District of Delaware on
January 20, 2021 purportedly on behalf of a class of investors who acquired Walmart stock from March 30, 2016 through
December 22, 2020. On May 11, 2021 the U.S. District Court in Delaware consolidated the class actions and appointed a lead
plaintiff and lead counsel. The defendants filed a motion to dismiss the consolidated securities class action on October 8, 2021;
the lead plaintiff responded to the motion on January 10, 2022; and the defendants filed their reply brief on February 10, 2022.
25

Two derivative actions were also filed by certain of the Company's shareholders in the U.S. District Court for the District of
Delaware on February 9, 2021 and April 16, 2021 alleging breach of fiduciary duties against certain of the Company's current
and former directors with respect to oversight of the Company's distribution and dispensing of opioids, and those suits have
been stayed pending further developments in other Opioids litigation matters.
Other shareholders filed a third derivative action making similar allegations in the Delaware Court of Chancery on September
27, 2021. The defendants in this derivative suit filed the opening brief on their motion to dismiss that case on December 21,
2021; and the plaintiffs responded by filing an amended complaint on February 22, 2022.
The Company cannot predict the number of such claims that may be filed, and cannot reasonably estimate any loss or range of
loss that may arise from such claims and the related opioid matters.
We discuss these cases and other litigation to which we are party below under the caption "Item 3. Legal Proceedings" and in
Note 10 in the "Notes to our Consolidated Financial Statements," which are part of this Annual Report on Form 10-K.
Our amended and restated bylaws designate the Court of Chancery of the State of Delaware as the sole and exclusive
forum for certain types of actions and proceedings that may be initiated by our shareholders, which could increase the
costs for our shareholders to bring claims, discourage our shareholders from bringing claims, or limit our shareholders'
ability to obtain a favorable judicial forum for disputes with us or our directors, officers, associates or shareholders in
such capacity.
Our bylaws provide that, unless we consent in writing to the selection of an alternative forum, the Court of Chancery of the
State of Delaware will, to the fullest extent permitted by law, be the sole and exclusive forum for claims, including derivative
claims that are based upon a violation of a duty by a current or former director, officer, associate or shareholder in such capacity
or as to which the Delaware General Corporation Law confers jurisdiction upon the Court of Chancery. The exclusive forum
provision may increase the costs for a shareholder to bring a claim or limit a shareholder's ability to bring a claim in a judicial
forum that the shareholder finds favorable for disputes with us or our directors, officers, associates or shareholders in such
capacity, which may discourage such lawsuits against us and such persons. Alternatively, if a court were to find these
provisions of our bylaws inapplicable to, or unenforceable in respect of, the claims as to which they are intended to apply, then
we may incur additional costs associated with resolving such matters in other jurisdictions, which could adversely affect our
business, financial position or results of operations. While the exclusive forum provision applies to state and federal law claims,
our shareholders will not be deemed to have waived our compliance with, and the exclusive forum provision will not preclude
or contract the scope of exclusive federal or concurrent jurisdiction for actions brought under, the federal securities laws,
including the Securities Exchange Act of 1934, as amended, or the Securities Act of 1933, as amended, and the rules and
regulations promulgated thereunder.
Our reputation may be adversely affected if we are not able to achieve our ESG goals.
We strive to deliver shared value through our business and our diverse stakeholders expect us to make significant progress in
certain ESG priority issue areas. From time to time, we announce certain aspirations and goals relevant to our priority ESG
issues. We periodically publish information about our ESG priorities, strategies, and progress on our corporate website and
update our ESG reporting from time to time. Achievement of these aspirations and goals is subject to risks and uncertainties,
many of which are outside of our control, and it is possible that we may fail, or be perceived to have failed, in the achievement
of our ESG goals or certain of our customers, associates, shareholders, investors, suppliers, business partners, government
agencies, and non-governmental organizations might not be satisfied with our efforts. Certain challenges we face in the
achievement of our ESG objectives are also captured within our ESG reporting, which is not incorporated by reference into and
does not form any part of this Annual Report on Form 10-K. A failure or perceived failure to meet our goals could adversely
affect public perception of our business, associate morale or customer or shareholder support.
ITEM 1B. UNRESOLVED STAFF COMMENTS
None.
26

ITEM 2. PROPERTIES
United States
The Walmart U.S. and Sam's Club segments comprise the Company's operations in the U.S. As of January 31, 2022, unit
counts for Walmart U.S. and Sam's Club are summarized by format for each state and territory as follows:
Walmart U.S. Sam's Club
State or Territory Supercenters Discount Stores
Neighborhood
Markets and
other small
formats Clubs Grand Total
Alabama 101 1 29 13 144
Alaska 7 2 — — 9
Arizona 83 2 28 12 125
Arkansas 76 5 37 9 127
California 144 68 79 30 321
Colorado 70 4 18 17 109
Connecticut 12 21 1 1 35
Delaware 6 3 — 1 10
Florida 233 9 98 46 386
Georgia 154 2 35 24 215
Hawaii — 10 — 2 12
Idaho 23 — 3 1 27
Illinois 139 15 11 25 190
Indiana 97 6 11 13 127
Iowa 58 2 — 9 69
Kansas 58 2 15 9 84
Kentucky 78 7 9 9 103
Louisiana 88 2 34 14 138
Maine 19 3 — 3 25
Maryland 30 17 3 11 61
Massachusetts 27 21 4 — 52
Michigan 90 3 9 23 125
Minnesota 65 3 1 12 81
Mississippi 65 3 11 7 86
Missouri 112 9 18 19 158
Montana 14 — — 2 16
Nebraska 35 — 7 5 47
Nevada 30 2 11 7 50
New Hampshire 19 7 — 2 28
New Jersey 35 27 1 8 71
New Mexico 35 2 9 7 53
New York 81 17 10 12 120
North Carolina 143 6 45 22 216
North Dakota 14 — — 3 17
Ohio 139 6 2 27 174
Oklahoma 81 7 35 13 136
Oregon 29 7 10 — 46
Pennsylvania 116 20 3 24 163
Puerto Rico 13 5 12 7 37
Rhode Island 5 4 — — 9
South Carolina 84 — 26 13 123
South Dakota 15 — — 2 17
Tennessee 117 1 19 14 151
Texas 391 18 110 82 601
Utah 41 — 13 8 62
Vermont 3 3 — — 6
Virginia 110 4 22 15 151
Washington 52 10 5 — 67
Washington D.C. 3 — 2 — 5
West Virginia 38 — 1 5 44
Wisconsin 83 4 2 10 99
Wyoming 12 — — 2 14
U.S. total 3,573 370 799 600 5,342
Square feet (in thousands)
634,754 38,947 29,295 80,351 783,347
27

International
The Walmart International segment comprises the Company's operations outside of the U.S. Unit counts as of January 31,
2022
(1)
for Walmart International are summarized by major category for each geographic market as follows:
Geographic Market Retail Wholesale Total
Square
feet
(2)
Africa
(3)
324 90 414 22,863
Canada 408 — 408 52,976
Central America
(4)
864 — 864 13,767
Chile 373 11 384 17,152
China 361 36 397 64,530
India — 29 29 1,570
Mexico 2,589 166 2,755 104,267
International total
4,919 332 5,251 277,125
(1)
Walmart International unit counts, with the exception of Canada, are as of December 31, 2021, to correspond with the balance sheet date of the related
geographic market. Canada unit counts are as of January 31, 2022.
(2)
Square feet reported in thousands.
(3)
Africa unit counts primarily reside in South Africa, with other locations in Botswana, Ghana, Kenya, Lesotho, Malawi, Mozambique, Namibia, Nigeria,
Swaziland, Tanzania, Uganda and Zambia.
(4)
Central America unit counts reside in Costa Rica, El Salvador, Guatemala, Honduras and Nicaragua.
Owned and Leased Properties
The following table provides further details of our retail units and distribution facilities, including return facilities and dedicated
eCommerce fulfillment centers, as of January 31, 2022
(1)
:
Owned Leased
(2)
Total
U.S. properties
Walmart U.S. retail units 4,065 677 4,742
Sam's Club retail units 513 87 600
Total U.S. retail units
4,578 764 5,342
Walmart U.S. distribution facilities 110 47 157
Sam's Club distribution facilities 11 17 28
Total U.S. distribution facilities
121 64 185
Total U.S. properties 4,699 828 5,527
International properties
Africa 36 378 414
Canada 124 284 408
Central America 367 497 864
Chile 205 179 384
China 2 395 397
India 2 27 29
Mexico 704 2,051 2,755
Total International retail units
1,440 3,811 5,251
International distribution facilities 22 157 179
Total International properties
1,462 3,968 5,430
Total properties 6,161 4,796 10,957
Total retail units
6,018 4,575 10,593
Total distribution facilities
143 221 364
Total properties 6,161 4,796 10,957
(1)
Walmart International properties, with the exception of Canada, are as of December 31, 2021, to correspond with the balance sheet date of the related
geographic market. Canada unit counts are as of January 31, 2022.
(2)
Also includes U.S. and international distribution facilities which are third-party owned and operated.
28

We own office facilities in Bentonville, Arkansas, that serve as our principal office and own and lease office facilities
throughout the U.S. and internationally for operations as well as for field and market management. The land on which our
stores are located is either owned or leased by the Company. We use independent contractors to construct our buildings. All
store leases provide for annual rentals, some of which escalate during the original lease or provide for additional rent based on
sales volume. Substantially all of the Company's store and club leases have renewal options, some of which include rent
escalation clauses. For further information on our distribution centers, see the caption "Distribution" provided for each of our
segments under "Item 1. Business."
29

ITEM 3. LEGAL PROCEEDINGS
I. SUPPLEMENTAL INFORMATION: We discuss certain legal proceedings in Note 10 to our Consolidated Financial
Statements included in "Item 8. Financial Statements and Supplementary Data," which is captioned "Contingencies," under the
sub-caption "Legal Proceedings." We refer you to that discussion for important information concerning those legal
proceedings, including the basis for such actions and, where known, the relief sought. We provide the following additional
information concerning those legal proceedings, including the name of the lawsuit, the court in which the lawsuit is pending,
and the date on which the petition commencing the lawsuit was filed.
Prescription Opiate Litigation: In re National Prescription Opiate Litigation (MDL No. 2804) (the "MDL"). The MDL is
pending in the U.S. District Court for the Northern District of Ohio and includes over 2,150 cases as of March 4, 2022. The
liability phase of a trial in one of the MDL cases began on October 4, 2021 against a number of parties, including the Company,
regarding opioid dispensing claims. On November 23, 2021, the jury found in favor of the plaintiffs as to the liability of all
defendants, including the Company. The abatement phase of the trial, which will determine amounts owed by the defendants,
is currently scheduled to begin on May 10, 2022. The Company intends to appeal the jury verdict from the liability phase upon
completion of the abatement phase of the trial. There is one case in which the Company is named as a defendant that was
remanded from the MDL court to the U.S. District Court for the Eastern District of Oklahoma (The Cherokee Nation v. CVS
Pharmacy, Inc., et al., Case No. CIV-18-56-RAW-SPS (E.D. Okla.)). This case was brought by the Cherokee Nation. Certain
motions have been filed by the parties to this case, and the case is currently stayed pending a ruling on those motions. In
addition, there are over 225 state court cases pending as of March 4, 2022, some of which may be removed to federal court to
seek MDL transfer. The case citations for the state cases are listed on Exhibit 99.1 to this Form 10-K.
DOJ Opioid Civil Litigation: On October 22, 2020, the Company filed a declaratory judgment action in the U.S. District
Court for the Eastern District of Texas against the U.S. Department of Justice (the "DOJ") and the U.S. Drug Enforcement
Administration, asking a federal court to clarify the roles and responsibilities of pharmacists and pharmacies as to the
dispensing and distribution of opioids under the Controlled Substances Act (the "CSA"). The Company's action, Walmart Inc.
v. U.S. Department of Justice et al., USDC, Eastern Dist. of Texas, 10/22/20, was dismissed. The Company had appealed this
decision to the Fifth Circuit. On December 22, 2021, the Fifth Circuit affirmed the dismissal of the action. A civil complaint
pending in the U.S. District Court for the District of Delaware has been filed by the DOJ against the Company, in which the
DOJ alleges violations of the CSA related to nationwide distribution and dispensing of opioids. U.S. v. Walmart Inc., et al.,
USDC, Dist. of DE, 12/22/20. The Company filed a motion to dismiss the DOJ complaint on February 22, 2021. The DOJ
filed its opposition brief on April 23, 2021 and the Company filed its reply brief on May 24, 2021. On November 19, 2021, the
District Court stayed further proceedings in the DOJ complaint pending the decision of the United States Supreme Court in two
other cases interpreting the CSA, which have been consolidated into Ruan v. United States, 142 S. Ct. 457 (2021).
Opioids Related Securities Class Actions and Derivative Litigation: Three derivative complaints and two securities class
actions drawing heavily on the allegations of the DOJ complaint have been filed in Delaware naming the Company and various
current and former directors and certain current and former officers as defendants. The plaintiffs in the derivative suits (in
which the Company is a nominal defendant) allege, among other things, that the defendants breached their fiduciary duties in
connection with oversight of opioids dispensing and distribution and that the defendants violated Section 14(a) of the Securities
Exchange Act of 1934, as amended (the "Exchange Act"), and are liable for contribution under Section 10(b) of the Exchange
Act in connection with the Company's disclosures about opioids. Two of the derivative suits have been filed in the U.S. District
Court in Delaware and those suits have been stayed pending further developments in other Opioids litigation matters. The other
derivative suit has been filed in the Chancery Court in Delaware. The securities class actions, alleging violations of Sections
10(b) and 20(a) of the Exchange Act regarding the Company's disclosures with respect to opioids, were purportedly filed on
behalf of a class of investors who acquired Walmart stock from March 30, 2016 through December 22, 2020. On May 11,
2021, the U.S. District Court in Delaware consolidated the class actions and appointed a lead plaintiff and lead counsel. The
defendants filed a motion to dismiss the consolidated securities class action on October 8, 2021; the lead plaintiff responded to
the motion on January 10, 2022; and the defendants filed their reply brief on February 10, 2022. The defendants in the
derivative suit pending in Delaware Chancery Court filed the opening brief on their motion to dismiss that case on December
21, 2021; and the plaintiffs responded by filing an amended complaint on February 22, 2022.
Derivative Lawsuits: Abt v. Alvarez et al., USDC, Dist. of DE, 2/9/21; Nguyen v. McMillon et al., USDC, Dist. of DE,
4/16/21: Ontario Provincial Council of Carpenters' Pension Trust Fund et al. v. Walton et al., DE Court of Chancery, 9/27/21.
Securities Class Actions: Stanton v. Walmart Inc. et al., USDC, Dist. of DE, 1/20/21 and Martin v. Walmart Inc. et al., USDC,
Dist. of DE, 3/5/21, consolidated into In re Walmart Inc. Securities Litigation, USDC, Dist. of DE, 5/11/21.
30

II. CERTAIN OTHER MATTERS:
Asda Equal Value Claims: Ms S Brierley & Others v ASDA Stores Ltd (2406372/2008 & Others - Manchester Employment
Tribunal); ASDA Stores Ltd v Brierley & Ors (A2/2016/0973 - United Kingdom Court of Appeal); ASDA Stores Ltd v Ms S
Brierley & Others (UKEAT/0059/16/DM - United Kingdom Employment Appeal Tribunal); ASDA Stores Ltd v Ms S Brierley
& Others (UKEAT/0009/16/JOJ - United Kingdom Employment Appeal Tribunal).
Money Transfer Agent Services Proceedings: The Company has received grand jury subpoenas issued by the United States
Attorney's Office for the Middle District of Pennsylvania seeking documents regarding the Company's consumer fraud program
and anti-money laundering compliance related to the Company's money transfer services, where Walmart is an agent. The most
recent subpoena was issued in August 2020. The Company has been responding to these subpoenas and is cooperating with the
government's investigation. The Company has also responded to civil investigative demands from the United States Federal
Trade Commission (the "FTC") in connection with the FTC's investigation related to money transfers and the Company's anti-
fraud program in its capacity as an agent. While the Company had been engaged in discussions with the FTC regarding a
potential resolution of this matter, the parties have not been able to reach a resolution. In November 2021, the FTC Bureau of
Consumer Protection forwarded a draft civil complaint to the FTC seeking authority to file a complaint against the Company
seeking various forms of monetary and injunctive relief. The FTC is currently considering whether to grant such authorization.
The Company is unable to predict the outcome of the investigations or any related actions by the governmental entities
regarding these matters at this time. While the Company does not currently believe that the outcome of these matters will have a
material adverse effect on its business, financial position, results of operations or cash flows, the Company can provide no
assurance as to the scope and outcome of these matters and whether its business, financial position, results of operations or cash
flows will not be materially adversely affected.
Foreign Direct Investment Matters: In July 2021, the Directorate of Enforcement in India issued a show cause notice to
Flipkart Private Limited and one of its subsidiaries ("Flipkart"), and to unrelated companies and individuals, including certain
current and former shareholders and directors of Flipkart. The notice requests the recipients to show cause as to why further
proceedings under India's Foreign Direct Investment rules and regulations (the "Rules") should not be initiated against them
based on alleged violations during the period from 2009 to 2015, prior to the Company's acquisition of a majority stake in
Flipkart in 2018. The notice is an initial stage of proceedings under the Rules which could, depending upon the conclusions at
the end of the initial stage, lead to a hearing to consider the merits of the allegations described in the notice. If a hearing is
initiated and if it is determined that violations of the Rules occurred, the regulatory authority has the authority to impose
monetary and/or non-monetary relief. Flipkart has begun the process of responding to the notice and, if the matter progresses to
a consideration of the merits of the allegations described in the notice is initiated, Flipkart intends to defend against the
allegations vigorously. Due to the fact that this process is in an early stage, the Company is unable to predict whether the notice
will lead to a hearing on the merits or, if it does, the final outcome of the resulting proceedings. While the Company does not
currently believe that this matter will have a material adverse effect on its business, financial condition, results of operations or
cash flows, the Company can provide no assurance as to the scope or outcome of any proceeding that might result from the
notice, the amount of the proceeds the Company may receive in indemnification from individuals and entities that sold shares to
the Company under the 2018 agreement pursuant to which the Company acquired its majority stake in Flipkart, or whether the
Company's business, financial position, results of operations or cash flows will not be materially adversely affected.
III. ENVIRONMENTAL MATTERS: Item 103 of SEC Regulation S-K requires disclosure of certain environmental matters
when a governmental authority is a party to the proceedings and such proceedings involve potential monetary sanctions that the
Company reasonably believes will exceed an applied threshold not to exceed $1 million.
In June 2021, the Company signed a tolling agreement with the Office of the Attorney General of the State of California to toll
the statute of limitations for potential claims regarding Walmart's management of waste consumer products at its California
facilities that are alleged to be hazardous. In December 2021, the Office of the Attorney General of the State of California filed
suit against the Company, bringing enforcement claims regarding Walmart's management of waste consumer products at its
California facilities that are alleged to be hazardous. The Company believes the suit is without merit and is vigorously
defending this litigation matter. While the Company cannot predict the ultimate outcome of this matter, the potential for
penalties or settlement costs could exceed $1 million. Although the Company does not believe that this matter will have a
material adverse effect on its business, financial position, results of operations, or cash flows, the Company can provide no
assurance as to the scope and outcome of these matters and whether its business, financial position, results of operations or cash
flows will not be materially adversely affected.
ITEM 4. MINE SAFETY DISCLOSURES
Not applicable.
31

PART II
ITEM 5. MARKET FOR REGISTRANT'S COMMON EQUITY, RELATED STOCKHOLDER MATTERS AND
ISSUER PURCHASES OF EQUITY SECURITIES
Market for Common Stock
The principal market on which Walmart's common stock is listed for trading is the New York Stock Exchange. The common
stock trades under the symbol "WMT."
Holders of Record of Common Stock
As of March 16, 2022, there were 209,870 holders of record of Walmart's common stock.
Stock Performance Chart
This graph compares the cumulative total shareholder return on Walmart's common stock during the five fiscal years ended
through fiscal 2022 to the cumulative total returns on the S&P 500 Retailing Index and the S&P 500 Index. The comparison
assumes $100 was invested on February 1, 2017 in shares of our common stock and in each of the indices shown and assumes
that all of the dividends were reinvested.
COMPARISON OF 5 YEAR CUMULATIVE TOTAL RETURN*
Among Walmart Inc., the S&P 500 Index
and S&P 500 Retailing Index
(Fiscal Years Ended January 31)
Walmart Inc. S&P 500 Index S&P 500 Retailing Index
2017 2018 2019 2020 2021 2022
$0
$50
$100
$150
$200
$250
$300
$350
*Assumes $100 Invested on February 1, 2017
Assumes Dividends Reinvested
Fiscal Year ended January 31, 2022
Fiscal Years Ended January 31,
2017 2018 2019 2020 2021 2022
Walmart Inc. $ 100.00 $ 163.83 $ 150.78 $ 183.78 $ 229.31 $ 231.82
S&P 500 Index 100.00 126.41 123.48 150.26 176.18 217.21
S&P 500 Retailing Index 100.00 148.34 159.89 190.43 278.09 296.49
Issuer Repurchases of Equity Securities
From time to time, the Company repurchases shares of our common stock under share repurchase programs authorized by the
Company's Board of Directors. All repurchases made prior to February 22, 2021 were made under the plan in effect at the
beginning of fiscal 2022. On February 18, 2021, the Board of Directors approved a new $20.0 billion share repurchase program
which has no expiration date or other restrictions limiting the period over which the Company can make repurchases, and
beginning February 22, 2021, replaced the previous share repurchase program. As of January 31, 2022, authorization for $10.6
billion of share repurchases remained under the share repurchase program. Any repurchased shares are constructively retired
and returned to an unissued status.
32

Share repurchase activity under our share repurchase programs, on a trade date basis, for each month in the quarter ended
January 31, 2022, was as follows:
Fiscal Period
Total Number of
Shares Repurchased
Average Price Paid
per Share
(in dollars)
Total Number of
Shares Repurchased
as Part of Publicly
Announced Plans or
Programs
Approximate Dollar Value of
Shares that May Yet Be
Repurchased Under the
Plans or Programs
(1)
(in billions)
November 1-30, 2021 4,709,717 $ 146.42 4,709,717 $ 12.4
December 1-31, 2021 7,170,376 140.09 7,170,376 11.4
January 1-31, 2022 5,284,996 141.50 5,284,996 10.6
Total
17,165,089 17,165,089
(1)
Represents the approximate dollar value of shares that could have been repurchased at the end of the month.
ITEM 6. RESERVED
33

ITEM 7. MANAGEMENT'S DISCUSSION AND ANALYSIS OF FINANCIAL CONDITION AND RESULTS OF
OPERATIONS
Overview
This discussion, which presents our results for the fiscal years ended January 31, 2022 ("fiscal 2022"), January 31, 2021 ("fiscal
2021") and January 31, 2020 ("fiscal 2020"), should be read in conjunction with our Consolidated Financial Statements and the
accompanying notes. We intend for this discussion to provide the reader with information that will assist in understanding our
financial statements, the changes in certain key items in those financial statements from period to period and the primary factors
that accounted for those changes. We also discuss certain performance metrics that management uses to assess the Company's
performance. Additionally, the discussion provides information about the financial results of each of the three segments to
provide a better understanding of how each of those segments and its results of operations affect the financial position and
results of operations of the Company as a whole.
Throughout this Item 7, we discuss segment operating income, comparable store and club sales and other measures.
Management measures the results of the Company's segments using each segment's operating income, including certain
corporate overhead allocations, as well as other measures. From time to time, we revise the measurement of each segment's
operating income and other measures as determined by the information regularly reviewed by our chief operating decision
maker.
Management also measures the results of comparable store and club sales, or comparable sales, a metric that indicates the
performance of our existing stores and clubs by measuring the change in sales for such stores and clubs, including eCommerce
sales, for a particular period from the corresponding period in the previous year. Walmart's definition of comparable sales
includes sales from stores and clubs open for the previous 12 months, including remodels, relocations, expansions and
conversions, as well as eCommerce sales. We measure the eCommerce sales impact by including all sales initiated digitally,
including omni-channel transactions which are fulfilled through our stores and clubs. Sales at a store that has changed in
format are excluded from comparable sales when the conversion of that store is accompanied by a relocation or expansion that
results in a change in the store's retail square feet of more than five percent. Sales related to divested businesses are excluded
from comparable sales, and sales related to acquisitions are excluded until such acquisitions have been owned for 12 months.
Comparable sales are also referred to as "same-store" sales by others within the retail industry. The method of calculating
comparable sales varies across the retail industry. As a result, our calculation of comparable sales is not necessarily comparable
to similarly titled measures reported by other companies.
In discussing our operating results, the term currency exchange rates refers to the currency exchange rates we use to convert the
operating results for countries where the functional currency is not the U.S. dollar into U.S. dollars. We calculate the effect of
changes in currency exchange rates as the difference between current period activity translated using the current period's
currency exchange rates and the comparable prior year period's currency exchange rates. Additionally, no currency exchange
rate fluctuations are calculated for non-USD acquisitions until owned for 12 months. Throughout our discussion, we refer to
the results of this calculation as the impact of currency exchange rate fluctuations. Volatility in currency exchange rates may
impact the results, including net sales and operating income, of the Company and the Walmart International segment in the
future.
We have taken certain strategic actions to strengthen our Walmart International portfolio for the long-term, including the
following highlights over the last three years:
• In November 2020, we completed the sale of Walmart Argentina and recorded a pre-tax non-cash loss in fiscal 2021 of
$1.0 billion, primarily due to cumulative foreign currency translation losses. Refer to Note 12.
• In February 2021, we completed the sale of Asda for net consideration of $9.6 billion, for which we recognized an
estimated pre-tax loss in fiscal 2021 of $5.5 billion, and an incremental loss of $0.2 billion in fiscal 2022 upon closing
of the transaction. Refer to Note 11 and Note 12.
• In March 2021, we completed the sale of Seiyu for net consideration of $1.2 billion, for which we recognized an
estimated pre-tax loss in fiscal 2021 of $1.9 billion, and an incremental loss of $0.2 billion in fiscal 2022 upon closing
of the transaction. Refer to Note 12.
We operate in the highly competitive omni-channel retail industry in all of the markets we serve. We face strong sales
competition from other discount, department, drug, dollar, variety and specialty stores, warehouse clubs and supermarkets, as
well as eCommerce, health and wellness, financial services, advertising, and data service businesses. Many of these
competitors are national, regional or international chains or have a national or international omni-channel or eCommerce
presence. We compete with a number of companies for attracting and retaining quality associates. We, along with other retail
companies, are influenced by a number of factors including, but not limited to: catastrophic events, weather and other risks
related to climate change, global health epidemics, including the COVID-19 pandemic, competitive pressures, consumer
disposable income, consumer debt levels and buying patterns, consumer credit availability, supply chain disruptions, cost and
availability of goods, currency exchange rate fluctuations, customer preferences, deflation, inflation, fuel and energy prices,
34

general economic conditions, insurance costs, interest rates, labor availability and costs, tax rates, the imposition of tariffs,
cybersecurity attacks and unemployment. Further information on the factors that can affect our operating results and on certain
risks to our Company and an investment in its securities can be found herein under "Item 1A. Risk Factors."
We expect continued uncertainty in our business and the global economy due to the duration and intensity of the COVID-19
pandemic; the duration and extent of economic stimulus measures; effectiveness and extent of administration of vaccinations
and medical treatment; supply chain disruptions; and volatility in employment trends and consumer confidence which may
impact our results. For a detailed discussion on results of operations by reportable segment, refer to "Results of Operations"
below.
Company Performance Metrics
We are committed to helping customers save money and live better through everyday low prices, supported by everyday low
costs. At times, we adjust our business strategies to maintain and strengthen our competitive positions in the countries in which
we operate. We define our financial framework as:
• strong, efficient growth;
• consistent operating discipline; and
• strategic capital allocation.
As we execute on this financial framework, we believe our returns on capital will improve over time.
Strong, Efficient Growth
Our objective of prioritizing strong, efficient growth means we will focus on the most productive growth opportunities,
increasing comparable store and club sales, accelerating eCommerce sales growth and expanding omni-channel initiatives that
complement our flywheel strategy while slowing the rate of growth of new stores and clubs. At times, we make strategic
investments which are focused on the long-term growth of the Company.
Comparable sales is a metric that indicates the performance of our existing stores and clubs by measuring the change in sales
for such stores and clubs, including eCommerce sales, for a particular period over the corresponding period in the previous
year. The retail industry generally reports comparable sales using the retail calendar (also known as the 4-5-4 calendar). To be
consistent with the retail industry, we provide comparable sales using the retail calendar in our quarterly earnings releases.
However, when we discuss our comparable sales below, we are referring to our calendar comparable sales calculated using our
fiscal calendar, which may result in differences when compared to comparable sales using the retail calendar.
Calendar comparable sales, including the impact of fuel, for fiscal 2022 and 2021, were as follows:
Fiscal Years Ended January 31,
2022 2021 2022 2021
With Fuel Fuel Impact
Walmart U.S. 6.4% 8.7% 0.3% (0.2)%
Sam's Club 15.0% 8.7% 5.5% (3.4)%
Total U.S.
7.7% 8.7% 1.2% (0.6)%
Comparable sales in the U.S., including fuel, increased 7.7% and 8.7% in fiscal 2022 and 2021, respectively, when compared to
the previous fiscal year. Walmart U.S. comparable sales increased 6.4% and 8.7% in fiscal 2022 and 2021, respectively. For
fiscal 2022, comparable sales growth was driven by growth in average ticket and transactions, which includes strong consumer
spending from government stimulus and some higher inflation impacts in certain merchandise categories compared to recent
years. In the first quarter of fiscal 2022, average ticket increased while transactions decreased as customers consolidated
shopping trips and purchased larger baskets. Transaction growth turned positive in April 2021 and continued with strong
growth through the rest of the year as customers' pre-pandemic behaviors largely resumed. For fiscal 2021, comparable sales
growth was driven by growth in average ticket primarily resulting from meeting the increased demand due to economic
conditions related to the COVID-19 pandemic while transactions decreased as customers consolidated shopping trips. Walmart
U.S. eCommerce sales positively contributed approximately 0.7% and 5.4% to comparable sales for fiscal 2022 and 2021,
respectively, as we continue to focus on a seamless omni-channel experience for our customers.
Sam's Club comparable sales increased 15.0% and 8.7% in fiscal 2022 and 2021, respectively. For fiscal 2022, Sam's Club
comparable sales benefited from growth in transactions and average ticket and was aided by consumer spending due to
government stimulus, and also includes some higher inflation impacts in certain merchandise categories compared to recent
years. The growth in comparable sales was partially offset by our decision to remove tobacco from certain club locations.
Sam's Club comparable sales for fiscal 2021 benefited from growth in transactions and average ticket resulting from the
COVID-19 pandemic, partially offset by both our decision to remove tobacco from certain club locations and by lower fuel
sales. Sam's Club eCommerce sales positively contributed approximately 1.3% and 2.2% to comparable sales for fiscal 2022
and 2021, respectively.
35

Consistent Operating Discipline
We operate with discipline by managing expenses, optimizing the efficiency of how we work and creating an environment in
which we have sustainable lowest cost to serve. We invest in technology and process improvements to increase productivity,
manage inventory and reduce costs. We measure operating discipline through expense leverage, which we define as net sales
growing at a faster rate than operating, selling, general and administrative ("operating") expenses.
Fiscal Years Ended January 31,
(Amounts in millions, except unit counts) 2022 2021
Net sales $ 567,762 $ 555,233
Percentage change from comparable period 2.3 % 6.8 %
Operating, selling, general and administrative expenses $ 117,812 $ 116,288
Percentage change from comparable period 1.3 % 6.9 %
Operating, selling, general and administrative expenses as a percentage of net sales 20.8 % 20.9 %
For fiscal 2022, operating expenses as a percentage of net sales decreased 19 basis points when compared to the previous fiscal
year. Operating expenses as a percentage of net sales benefited from growth in comparable sales and lower incremental
COVID-19 related costs of $2.5 billion as compared to the previous year, partially offset by increased wage investments
primarily in the Walmart U.S. segment.
For fiscal 2021, operating expenses as a percentage of net sales was flat when compared to the previous fiscal year. Operating
expenses as a percentage of net sales benefited from strong growth in comparable sales, offset by $4.0 billion of incremental
costs related to the COVID-19 pandemic.
Strategic Capital Allocation
Our strategy includes improving our customer-facing initiatives in stores and clubs and creating a seamless omni-channel
experience for our customers. As such, we continue to allocate more capital to supply chain, omni-channel initiatives,
technology and store remodels and less to new store and club openings. The following table provides additional detail:
(Amounts in millions)
Fiscal Years Ended January 31,
Allocation of Capital Expenditures 2022 2021
Supply chain, omni-channel, technology and other $ 7,197 $ 5,681
Remodels 3,278 2,013
New stores and clubs, including expansions and relocations 134 134
Total U.S.
$ 10,609 $ 7,828
Walmart International 2,497 2,436
Total capital expenditures
$ 13,106 $ 10,264
Returns
As we execute our financial framework, we believe our return on capital will improve over time. We measure return on capital
with our return on assets, return on investment and free cash flow metrics. We also provide returns in the form of share
repurchases and dividends, which are discussed in the Liquidity and Capital Resources section.
Return on Assets and Return on Investment
We include Return on Assets ("ROA"), the most directly comparable measure based on our financial statements presented in
accordance with generally accepted accounting principles in the U.S. ("GAAP"), and Return on Investment ("ROI") as metrics
to assess returns on assets. While ROI is considered a non-GAAP financial measure, management believes ROI is a
meaningful metric to share with investors because it helps investors assess how effectively Walmart is deploying its assets.
Trends in ROI can fluctuate over time as management balances long-term strategic initiatives with possible short-term impacts.
ROA was 5.6% for both fiscal 2022 and 2021, respectively. ROI was 14.9% and 14.0% for fiscal 2022 and 2021, respectively,
which increased primarily due to the increase in operating income.
We define ROI as adjusted operating income (operating income plus interest income, depreciation and amortization, and rent
expense) for the trailing twelve months divided by average invested capital during that period. We consider average invested
capital to be the average of our beginning and ending total assets, plus average accumulated depreciation and average
amortization, less average accounts payable and average accrued liabilities for that period.
Our calculation of ROI is considered a non-GAAP financial measure because we calculate ROI using financial measures that
exclude and include amounts that are included and excluded in the most directly comparable GAAP financial measure. For
example, we exclude the impact of depreciation and amortization from our reported operating income in calculating the
numerator of our calculation of ROI. As mentioned above, we consider ROA to be the financial measure computed in
accordance with GAAP most directly comparable to our calculation of ROI. ROI differs from ROA (which is consolidated net
income for the period divided by average total assets for the period) because ROI: adjusts operating income to exclude certain
36

expense items and adds interest income; and adjusts total assets for the impact of accumulated depreciation and amortization,
accounts payable and accrued liabilities to arrive at total invested capital. Because of the adjustments mentioned above, we
believe ROI more accurately measures how we are deploying our key assets and is more meaningful to investors than ROA.
Although ROI is a standard financial measure, numerous methods exist for calculating a company's ROI. As a result, the
method used by management to calculate our ROI may differ from the methods used by other companies to calculate their ROI.
The calculation of ROA and ROI, along with a reconciliation of ROI to the calculation of ROA, the most comparable GAAP
financial measure, is as follows:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021
CALCULATION OF RETURN ON ASSETS
Numerator
Consolidated net income $ 13,940 $ 13,706
Denominator
Average total assets
(1)
$ 248,678 $ 244,496
Return on assets (ROA)
5.6 % 5.6 %
CALCULATION OF RETURN ON INVESTMENT
Numerator
Operating income $ 25,942 $ 22,548
+ Interest income 158 121
+ Depreciation and amortization 10,658 11,152
+ Rent 2,274 2,626
ROI operating income $ 39,032 $ 36,447
Denominator
Average total assets
(1)
$ 248,678 $ 244,496
+ Average accumulated depreciation and amortization
(1)
98,199 94,351
- Average accounts payable
(1)
52,201 48,057
- Average accrued liabilities
(1)
32,013 30,131
Average invested capital $ 262,663 $ 260,659
Return on investment (ROI)
14.9 % 14.0 %
(1)
The average is based on the addition of the account balance at the end of the current period to the account balance at the end of the prior period and dividing
by 2.
As of January 31,
2022 2021 2020
Certain Balance Sheet Data
Total assets $ 244,860 $ 252,496 $ 236,495
Accumulated depreciation and amortization 102,211 94,187 94,514
Accounts payable 55,261 49,141 46,973
Accrued liabilities 26,060 37,966 22,296
Free Cash Flow
Free cash flow is considered a non-GAAP financial measure. Management believes, however, that free cash flow, which
measures our ability to generate additional cash from our business operations, is an important financial measure for use in
evaluating the Company's financial performance. Free cash flow should be considered in addition to, rather than as a substitute
for, consolidated net income as a measure of our performance and net cash provided by operating activities as a measure of our
liquidity. See "Liquidity and Capital Resources" for discussions of GAAP metrics including net cash provided by operating
activities, net cash used in investing activities and net cash used in financing activities.
We define free cash flow as net cash provided by operating activities in a period minus payments for property and equipment
made in that period. We had net cash provided by operating activities of $24.2 billion, $36.1 billion and $25.3 billion for fiscal
2022, 2021 and 2020, respectively. We generated free cash flow of $11.1 billion, $25.8 billion and $14.6 billion for fiscal
2022, 2021 and 2020, respectively. Net cash provided by operating activities for fiscal 2022 decreased when compared to fiscal
2021 primarily due to an increase in inventory costs and purchases to support strong sales and lapping the impact of accelerated
inventory sell-through in fiscal 2021, as well as timing and payment of wages. Free cash flow for fiscal 2022 decreased when
compared to fiscal 2021 due to the same reasons as the decrease in net cash provided by operating activities, as well as $2.8
billion in increased capital expenditures. Net cash provided by operating activities for fiscal 2021 increased when compared to
fiscal 2020 primarily due to the impact of the global health crisis which accelerated inventory sell-through, as well as the timing
and payment of inventory purchases, incremental COVID-19 related expenses and certain benefit payments. Free cash flow for
37

fiscal 2021 increased when compared to fiscal 2020 due to the same reasons as the increase in net cash provided by operating
activities, as well as $0.4 billion in decreased capital expenditures.
Walmart's definition of free cash flow is limited in that it does not represent residual cash flows available for discretionary
expenditures due to the fact that the measure does not deduct the payments required for debt service and other contractual
obligations or payments made for business acquisitions. Therefore, we believe it is important to view free cash flow as a
measure that provides supplemental information to our Consolidated Statements of Cash Flows.
Although other companies report their free cash flow, numerous methods may exist for calculating a company's free cash flow.
As a result, the method used by management to calculate our free cash flow may differ from the methods used by other
companies to calculate their free cash flow.
The following table sets forth a reconciliation of free cash flow, a non-GAAP financial measure, to net cash provided by
operating activities, which we believe to be the GAAP financial measure most directly comparable to free cash flow, as well as
information regarding net cash used in investing activities and net cash used in financing activities.
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Net cash provided by operating activities $ 24,181 $ 36,074 $ 25,255
Payments for property and equipment (13,106) (10,264) (10,705)
Free cash flow
$ 11,075 $ 25,810 $ 14,550
Net cash used in investing activities
(1)
$ (6,015) $ (10,071) $ (9,128)
Net cash used in financing activities (22,828) (16,117) (14,299)
(1)
"Net cash used in investing activities" includes payments for property and equipment, which is also included in our computation of free cash flow.
Results of Operations
Consolidated Results of Operations
Fiscal Years Ended January 31,
(Amounts in millions, except unit counts) 2022 2021 2020
Total revenues $ 572,754 $ 559,151 $ 523,964
Percentage change from comparable period 2.4 % 6.7 % 1.9 %
Net sales $ 567,762 $ 555,233 $ 519,926
Percentage change from comparable period 2.3 % 6.8 % 1.9 %
Total U.S. calendar comparable sales increase 7.7 % 8.7 % 2.7 %
Gross profit rate 24.4 % 24.3 % 24.1 %
Operating income $ 25,942 $ 22,548 $ 20,568
Operating income as a percentage of net sales 4.6 % 4.1 % 4.0 %
Loss on extinguishment of debt $ 2,410 $ — $ —
Other (gains) and losses $ 3,000 $ (210) $ (1,958)
Consolidated net income $ 13,940 $ 13,706 $ 15,201
Unit counts at period end
(1)
10,593 11,443 11,501
Retail square feet at period end
(1)
1,060 1,121 1,129
(1)
Unit counts and associated retail square feet are presented for stores and clubs generally open as of period end, and reflects the removal of stores in the U.K.
and Japan subsequent to closing the divestitures in fiscal 2022. Permanently closed locations are not included.
Our total revenues, which includes net sales and membership and other income, increased $13.6 billion or 2.4% and $35.2
billion or 6.7% for fiscal 2022 and 2021, respectively, when compared to the previous fiscal year. These increases in revenues
were primarily due to increases in net sales, which increased $12.5 billion or 2.3% and $35.3 billion or 6.8% for fiscal 2022 and
2021, respectively, when compared to the previous fiscal year. For fiscal 2022, the increase was primarily due to strong
positive comparable sales for the Walmart U.S. and Sam's Club segments which benefited from strong U.S. consumer spending
and some inflation, along with positive comparable sales in most of our remaining international markets. The increase was
partially offset by a $32.6 billion net sales decrease primarily related to the divestiture of our operations in the U.K. and Japan,
which closed in the first quarter of fiscal 2022. Net sales also benefited from a $4.5 billion positive impact of fluctuations in
currency exchange rates during fiscal 2022. For fiscal 2021, the increase was primarily due to strong positive comparable sales
for the Walmart U.S. and Sam's Club segments as well as positive comparable sales in the majority of our international markets
resulting from increased demand stemming from the COVID-19 pandemic. Overall net sales growth was strong despite certain
operating limitations in several international markets in the second quarter of fiscal 2021 due to government regulations and
precautionary measures taken as a result of the COVID-19 pandemic. The net sales increase was partially offset by a negative
impact from fluctuations in currency exchange rates of $5.0 billion.
Our gross profit rate increased 14 and 20 basis points for fiscal 2022 and 2021, respectively, when compared to the previous
fiscal year. For fiscal 2022, the increase was primarily due to price management in the Walmart U.S. segment driven by cost
38

inflation as well as merchandise mix, partially offset by increased supply chain costs. For fiscal 2021, the increase was
primarily due to strategic sourcing initiatives, strong sales in higher margin categories, and fewer markdowns. This was
partially offset in the Walmart U.S. segment by carryover of prior year price investment as well as the temporary closure of our
Auto Care Centers and Vision Centers in response to the COVID-19 pandemic.
For fiscal 2022, operating expenses as a percentage of net sales decreased 19 basis points when compared to the previous fiscal
year. Operating expenses as a percentage of net sales benefited from growth in comparable sales and lower incremental
COVID-19 related costs of $2.5 billion as compared to the previous year, partially offset by increased wage investments
primarily in the Walmart U.S. segment. For fiscal 2021, operating expenses as a percentage of net sales was flat when
compared to the previous fiscal year. Operating expenses as a percentage of net sales benefited from strong growth in
comparable sales, offset by $4.0 billion of incremental costs related to the COVID-19 pandemic.
Loss on extinguishment of debt was $2.4 billion in fiscal 2022 due to the early retirement of certain higher rate long-term debt
to reduce interest expense in future periods.
Other gains and losses consisted of a net loss of $3.0 billion and a net gain of $0.2 billion for fiscal 2022 and 2021, respectively.
The loss in fiscal 2022 primarily reflects net losses associated with the fair value changes of our equity investments, as well as
$0.4 billion in incremental losses associated with the divestiture of certain international operations which closed in the first
quarter of fiscal 2022. The gain in fiscal 2021 primarily reflects $8.7 billion in net gains associated with the fair value changes
of our equity investments, partially offset by the $8.3 billion pre-tax loss related to the divestiture of certain international
operations classified as held for sale or sold in fiscal 2021.
Our effective income tax rate was 25.4% for fiscal 2022, 33.3% for fiscal 2021, and 24.4% for fiscal 2020. The decrease in our
effective tax rate for fiscal 2022 as compared to fiscal 2021, and the increase in our effective tax rate for fiscal 2021 as
compared to fiscal 2020, is primarily due to the $8.3 billion loss related to the divestiture of certain international operations
classified as held for sale or sold in fiscal 2021, which provided minimal realizable tax benefit. Our effective income tax rate
may also fluctuate as a result of various factors, including changes in our assessment of certain tax contingencies, valuation
allowances, changes in tax law, outcomes of administrative audits, the impact of discrete items and the mix and size of earnings
among our U.S. operations and international operations, which are subject to statutory rates that are generally higher than the
U.S. statutory rate. The reconciliation from the U.S. statutory rate to the effective income tax rates for fiscal 2022, 2021 and
2020 is presented in Note 9.
As a result of the factors discussed above, we reported $13.9 billion and $13.7 billion of consolidated net income for fiscal 2022
and 2021, respectively, which represents an increase of $0.2 billion and a decrease of $1.5 billion for fiscal 2022 and 2021,
respectively, when compared to the previous fiscal year. Diluted net income per common share attributable to Walmart
("EPS") was $4.87, $4.75 and $5.19 for fiscal 2022, 2021 and 2020, respectively.
Walmart U.S. Segment
Fiscal Years Ended January 31,
(Amounts in millions, except unit counts)
2022 2021 2020
Net sales $ 393,247 $ 369,963 $ 341,004
Percentage change from comparable period 6.3 % 8.5 % 2.8 %
Calendar comparable sales increase 6.4 % 8.7 % 2.9 %
Operating income $ 21,587 $ 19,116 $ 17,380
Operating income as a percentage of net sales 5.5 % 5.2 % 5.1 %
Unit counts at period end 4,742 4,743 4,756
Retail square feet at period end 703 703 703
Net sales for the Walmart U.S. segment increased $23.3 billion or 6.3% and $29.0 billion or 8.5% for fiscal 2022 and 2021,
respectively, when compared to the previous fiscal year. The increases in net sales were primarily due to increases in
comparable sales of 6.4% and 8.7% for fiscal 2022 and 2021, respectively. Comparable sales in fiscal 2022 were driven by
growth in average ticket and transactions, which includes strong consumer spending from government stimulus and some
higher inflation impacts in certain merchandise categories compared to recent years. In the first quarter of fiscal 2022, average
ticket increased while transactions decreased as customers consolidated shopping trips and purchased larger baskets.
Transaction growth turned positive in April 2021 and continued with strong growth through the rest of the year as customers'
pre-pandemic behaviors largely resumed. Comparable sales in fiscal 2021 were driven by growth in average ticket primarily
resulting from meeting the increased demand due to economic conditions related to the COVID-19 pandemic while transactions
decreased as customers consolidated shopping trips. Walmart U.S. eCommerce sales positively contributed approximately
0.7% and 5.4% to comparable sales for fiscal 2022 and 2021, respectively, as we continue to focus on a seamless omni-channel
experience for our customers.
Gross profit rate increased 51 basis points for fiscal 2022 and was flat for fiscal 2021, when compared to the respective
previous fiscal year. The increase in fiscal 2022 gross profit rate was primarily due to price management driven by cost
inflation as well merchandise mix, which includes lapping the temporary closures of our Auto Care and Vision Centers and
39

growth in our advertising business, partially offset by increased supply chain costs. Gross profit rate for fiscal 2021 benefited
from strategic sourcing initiatives and fewer markdowns, but was offset by a change in merchandise mix, the carryover effect of
prior price investment and the temporary closure of our Auto Care and Vision Centers in response to the COVID-19 pandemic.
Operating expenses as a percentage of segment net sales increased 31 basis points for fiscal 2022 when compared to the
previous fiscal year. Despite the strong sales growth described above, fiscal 2022 operating expenses as a percentage of
segment net sales increased primarily due to investments in wages, partially offset by lower incremental COVID-19 related
costs of $1.9 billion. For fiscal 2021, operating expenses as a percentage of segment net sales decreased 15 basis points
primarily due to strong sales, which were partially offset by $3.2 billion of incremental costs related to the COVID-19
pandemic including special bonuses, expanded sick and emergency leave pay, costs associated with outfitting our stores and
associates with masks, gloves and sanitizer, and expanded cleaning practices.
As a result of the factors discussed above, segment operating income increased $2.5 billion and increased $1.7 billion for fiscal
2022 and 2021, respectively, when compared to the previous fiscal year.
Walmart International Segment
Fiscal Years Ended January 31,
(Amounts in millions, except unit counts)
2022 2021 2020
Net sales $ 100,959 $ 121,360 $ 120,130
Percentage change from comparable period (16.8) % 1.0 % (0.6) %
Operating income $ 3,758 $ 3,660 $ 3,370
Operating income as a percentage of net sales 3.7 % 3.0 % 2.8 %
Unit counts at period end 5,251 6,101 6,146
Retail square feet at period end 277 337 345
Net sales for the Walmart International segment decreased $20.4 billion or 16.8% and increased $1.2 billion or 1.0% for fiscal
2022 and 2021, respectively, when compared to the previous fiscal year. For fiscal 2022, the reduction in net sales was driven
by a $32.6 billion decrease primarily related to the divestitures of Asda and Seiyu, which closed during the first quarter of fiscal
2022. This decrease was partially offset by positive comparable sales in most of our remaining markets, as well as positive
fluctuations in currency exchange rates of $4.5 billion. For fiscal 2021, the increase was primarily due to positive comparable
sales growth in the majority of our markets driven by changes in consumer behavior in response to the COVID-19 pandemic,
partially offset by negative fluctuations in currency exchange rates of $5.0 billion. The pandemic led to significant economic
pressures and channel and mix shifts due to changes in consumer behavior, including accelerated growth in eCommerce in
several markets. While several of our markets experienced extensive store and operational closures in the second quarter of
fiscal 2021 as a result of government mandates, most closed stores and warehouses had resumed operations by the third quarter
of fiscal 2021.
Gross profit rate decreased 55 basis points and increased 50 basis points for fiscal 2022 and 2021, respectively, when compared
to the previous fiscal year. For fiscal 2022, the decrease was primarily driven by shifts into lower margin formats and the
impact related to our divested markets. For fiscal 2021, the increase was primarily due to Flipkart's improved margin mix and
reduced fuel sales in the U.K.
Operating expenses as a percentage of segment net sales decreased 71 basis points and increased 14 basis points for fiscal 2022
and 2021, respectively, when compared to the previous fiscal year. The decrease in operating expenses as a percentage of
segment net sales for fiscal 2022 was primarily due to impacts from the divested markets and $0.4 billion of lower incremental
COVID-19 related costs. Operating expenses as a percentage of net sales benefited from depreciation and amortization expense
not having been recorded for our operations in the U.K. and Japan subsequent to their held for sale classification at the end of
fiscal 2021 and prior to closing during the first quarter of fiscal 2022. For fiscal 2021, the increase was primarily due to $0.5
billion of incremental costs related to the COVID-19 pandemic, partially offset by positive comparable sales in the majority of
our markets and lapping a $0.4 billion non-cash impairment charge recorded in fiscal 2020.
Operating income for fiscal 2022 included a $0.3 billion impact from positive fluctuations in currency exchange rates, and
fiscal 2021 included a $0.2 billion impact from negative fluctuations in currency exchange rates. As a result of the factors
discussed above, segment operating income increased $0.1 billion and $0.3 billion for fiscal 2022 and 2021, respectively, when
compared to the previous fiscal year.
40

Sam's Club Segment
Fiscal Years Ended January 31,
(Amounts in millions, except unit counts) 2022 2021 2020
Including Fuel
Net sales $ 73,556 $ 63,910 $ 58,792
Percentage change from comparable period 15.1 % 8.7 % 1.6 %
Calendar comparable sales increase 15.0 % 8.7 % 1.6 %
Operating income $ 2,259 $ 1,906 $ 1,642
Operating income as a percentage of net sales 3.1 % 3.0 % 2.8 %
Unit counts at period end 600 599 599
Retail square feet at period end 80 80 80
Excluding Fuel
(1)
Net sales $ 64,860 $ 59,184 $ 52,792
Percentage change from comparable period 9.6 % 12.1 % 0.9 %
Operating income $ 1,923 $ 1,645 $ 1,486
Operating income as a percentage of net sales 3.0 % 2.8 % 2.8 %
(1)
We believe the "Excluding Fuel" information is useful to investors because it permits investors to understand the effect of the Sam's Club segment's fuel
sales on its results of operations, which are impacted by the volatility of fuel prices. Volatility in fuel prices may continue to impact the operating results of
the Sam's Club segment in the future. Management uses such information to better measure underlying operating results in the segment.
Net sales for the Sam's Club segment increased $9.6 billion or 15.1% and $5.1 billion or 8.7% for fiscal 2022 and 2021,
respectively, when compared to the previous fiscal year. For fiscal 2022, the increase was primarily due to comparable sales
growth, including fuel, of 15.0%. Comparable sales benefited from growth in transactions and average ticket due to increased
consumer spending, which was aided by government stimulus, and also includes some higher inflation impacts in certain
merchandise categories compared to recent years. The growth in comparable sales was partially offset by our decision to
remove tobacco from certain club locations. Sam's Club eCommerce sales positively contributed approximately 1.3% to
comparable sales. For fiscal 2021, the increase was primarily due to comparable sales, including fuel, of 8.7%. Comparable
sales benefited from growth in transactions and average ticket resulting from the COVID-19 pandemic, partially offset by our
decision to remove tobacco from certain club locations and by lower fuel sales. Sam's Club eCommerce sales positively
contributed approximately 2.2% to comparable sales.
Gross profit rate decreased 68 basis points and increased 65 basis points for fiscal 2022 and 2021, respectively, when compared
to the previous fiscal year. For fiscal 2022, the decrease in gross profit rate was primarily due to increased fuel sales which
have lower margins, cost inflation, and higher supply chain costs, partially offset by favorable sales mix, including reduced
tobacco sales. For fiscal 2021, gross profit rate increased due to favorable sales mix, including lower fuel and tobacco sales,
and improvement in inventory losses which was partially offset by price investment and higher eCommerce fulfillment costs.
Membership and other income increased 13.1% and 6.8% for fiscal 2022 and 2021, respectively, when compared to the
previous fiscal year. For fiscal 2022, the increase was primarily due to growth in total members and increased Plus Member
penetration. For fiscal 2021, the increase was primarily due to growth in total members, which benefited from higher overall
renewal rates and higher Plus Member penetration.
Operating expenses as a percentage of segment net sales decreased 82 basis points and increased 42 basis points for fiscal 2022
and 2021, respectively, when compared to the previous fiscal year. Fiscal 2022 operating expenses as a percentage of net sales
decreased primarily due to higher sales as well as a benefit from $0.2 billion of lower incremental COVID-19 related costs,
partially offset by reduced tobacco sales. Despite the increased sales growth described above, fiscal 2021 operating expenses as
a percentage of net sales increased primarily due to $0.3 billion of incremental costs related to the pandemic, which included
additional costs such as special bonuses, expanded cleaning practices and security, expanded sick and emergency leave pay, and
outfitting our associates with masks and gloves. Additionally, the increase in operating expense as a percentage of segment net
sales was affected by reduced tobacco and fuel sales.
As a result of the factors discussed above, segment operating income increased $0.4 billion and $0.3 billion for fiscal 2022 and
2021, respectively, when compared to the previous fiscal year.
Liquidity and Capital Resources
Liquidity
The strength and stability of our operations have historically supplied us with a significant source of liquidity. Our cash flows
provided by operating activities, supplemented with our long-term debt and short-term borrowings, have been sufficient to fund
our operations while allowing us to invest in activities that support the long-term growth of our operations. Generally, some or
all of the remaining available cash flow has been used to fund dividends on our common stock and share repurchases. We
believe our sources of liquidity will continue to be sufficient to fund operations, finance our global investment activities, pay
dividends and fund our share repurchases for at least the next 12 months and thereafter for the foreseeable future.
41

Net Cash Provided by Operating Activities
Fiscal Years Ended January 31,
(Amounts in millions)
2022 2021 2020
Net cash provided by operating activities $ 24,181 $ 36,074 $ 25,255
Net cash provided by operating activities was $24.2 billion, $36.1 billion and $25.3 billion for fiscal 2022, 2021 and 2020,
respectively. Net cash provided by operating activities for fiscal 2022 decreased when compared to the previous fiscal year
primarily due to an increase in inventory costs and purchases to support strong sales and lapping the impact of accelerated
inventory sell-through in fiscal 2021, as well as timing and payment of wages. The increase in net cash provided by operating
activities for fiscal 2021, when compared to the previous fiscal year, was primarily due to the impact of the global health crisis
which accelerated inventory sell-through, as well as the timing and payment of inventory purchases, incremental COVID-19
related expenses and certain benefit payments.
Cash Equivalents and Working Capital Deficit
Cash and cash equivalents were $14.8 billion and $17.7 billion as of January 31, 2022 and 2021, respectively. Our working
capital deficit, defined as total current assets less total current liabilities, was $6.3 billion and $2.6 billion as of January 31, 2022
and 2021, respectively. We generally operate with a working capital deficit due to our efficient use of cash in funding
operations, consistent access to the capital markets and returns provided to our shareholders in the form of payments of cash
dividends and share repurchases.
We use intercompany financing arrangements in an effort to ensure cash can be made available in the country in which it is
needed with the minimum cost possible. Additionally, from time-to-time, we repatriate earnings and related cash from
jurisdictions outside of the U.S. Historically, U.S. taxes were due upon repatriation of foreign earnings. Due to the enactment
of U.S. tax reform, repatriations of foreign earnings will generally be free of U.S. federal tax, but may incur other taxes such as
withholding or state taxes. While we are currently evaluating recent regulations issued from the Internal Revenue Service
("IRS") and the U.S. Treasury Department, we do not expect current local laws, other existing limitations on anticipated future
repatriations of cash amounts held outside the U.S. to have a material effect on our overall liquidity, financial position or results
of operations.
As of January 31, 2022 and 2021, cash and cash equivalents of $4.3 billion and $2.8 billion, respectively, may not be freely
transferable to the U.S. due to local laws or other restrictions. Of the $4.3 billion as of January 31, 2022, approximately $2.2
billion can only be accessed through dividends or intercompany financing arrangements subject to approval of the Flipkart
minority shareholders; however, this cash is expected to be utilized by Flipkart.
Net Cash Used in Investing Activities
Fiscal Years Ended January 31,
(Amounts in millions)
2022 2021 2020
Net cash used in investing activities $ (6,015) $ (10,071) $ (9,128)
Net cash used in investing activities was $6.0 billion, $10.1 billion and $9.1 billion for fiscal 2022, 2021 and 2020, respectively,
and generally consisted of capital expenditures. Net cash used in investing activities decreased $4.1 billion for fiscal 2022
when compared to the previous fiscal year primarily due to the net proceeds received from the divestitures of Asda and Seiyu,
partially offset by increased capital expenditures. Net cash used in investing activities increased $0.9 billion for fiscal 2021
when compared to the previous fiscal year, primarily as a result of lapping the net proceeds received from the sale of our
banking operations in Walmart Canada and the change in other investing activities, partially offset by decreased capital
expenditures.
Capital expenditures
Refer to the "Strategic Capital Allocation" section in our Company Performance Metrics for capital expenditure detail for fiscal
2022 and 2021. For the fiscal year ending January 31, 2023 ("fiscal 2023"), we project capital expenditures will be
approximately $18 billion, with a focus on supply chain, automation, customer-facing initiatives and technology.
Net Cash Used in Financing Activities
Fiscal Years Ended January 31,
(Amounts in millions)
2022 2021 2020
Net cash used in financing activities $ (22,828) $ (16,117) $ (14,299)
Net cash from financing activities generally consists of transactions related to our short-term and long-term debt, financing
obligations, dividends paid and the repurchase of Company stock. Transactions with noncontrolling interest shareholders are
also classified as cash flows from financing activities. Fiscal 2022 net cash used in financing activities increased $6.7 billion
when compared to the previous fiscal year. The increase is primarily due to repayments of long-term debt and related payment
42

of premiums for the early extinguishment of certain notes, as well as increased share repurchases, partially offset by new long-
term debt issuances in the current year and equity funding from the sale of subsidiary stock. Fiscal 2021 net cash used in
financing activities increased $1.8 billion for fiscal 2021 when compared to the previous fiscal year. The increase was
primarily due to the timing of issuances and repayments of long-term debt, partially offset by both a reduction in cash used to
pay down short-term borrowings as well as share repurchases.
Sale of Subsidiary Stock
During fiscal 2022, the Company received $3.2 billion primarily related to a new equity funding for the Company's majority-
owned Flipkart subsidiary, which reduced the Company's ownership from approximately 83% as of January 31, 2021 to
approximately 75%.
Short-term Borrowings
We generally utilize the liquidity provided by short-term borrowings to provide funding for our operations, dividend payments,
share repurchases, capital expenditures and other cash requirements. The following table includes additional information related
to the Company's short-term borrowings for fiscal 2022, 2021 and 2020:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Maximum amount outstanding at any month-end $ 716 $ 4,048 $ 13,315
Average daily short-term borrowings 626 1,577 7,120
Annual weighted-average interest rate 3.7 % 3.1 % 2.5 %
Short-term borrowings as of January 31, 2022 and 2021 were $0.4 billion and $0.2 billion, respectively, with weighted-average
interest rates of 2.9% and 1.9%, respectively. We also have $15.0 billion of various undrawn committed lines of credit in the
U.S. as of January 31, 2022 that provide additional liquidity, if needed. Additionally, we maintain access to various credit
facilities outside of the U.S. to further support our Walmart International segment operations, as needed.
As of January 31, 2022, we have $1.8 billion of syndicated and fronted letters of credit available, of which $1.7 billion was
drawn and represents an unrecorded current obligation.
Long-term Debt
The following table provides the changes in our long-term debt for fiscal 2022:
(Amounts in millions)
Long-term debt due
within one year Long-term debt Total
Balances as of February 1, 2021
$ 3,115 $ 41,194 $ 44,309
Proceeds from issuance of long-term debt — 6,945 6,945
Repayments of long-term debt (3,010) (10,000) (13,010)
Reclassifications of long-term debt 2,687 (2,687) —
Currency and other adjustments
11
(588) (577)
Balances as of January 31, 2022
$ 2,803 $ 34,864 $ 37,667
Our total outstanding long-term debt decreased $6.6 billion during fiscal 2022, primarily due to the extinguishment and
maturities of certain long-term debt, partially offset by the issuance of new long-term debt in September 2021. Refer to Note 6
to our Consolidated Financial Statements for details on the maturities, extinguishment and issuances of long-term debt. The
early extinguishment of certain long-term debt allowed us to retire higher rate debt to reduce interest expense in future periods.
In connection with this early extinguishment of debt, the Company paid premiums of $2.3 billion, which represents the majority
of the $2.4 billion loss recorded on the transaction during fiscal 2022.
Estimated contractual interest payments associated with our long-term debt amount to $16.0 billion, with approximately $1.3
billion expected to be paid in fiscal 2023. Estimated interest payments are based on our principal amounts and expected
maturities of all debt outstanding as of January 31, 2022 and assumes interest rates remain at current levels for our variable rate
instruments.
Dividends
Our total dividend payments were $6.2 billion, $6.1 billion and $6.0 billion for fiscal 2022, 2021 and 2020, respectively.
Effective February 17, 2022, the Board of Directors approved the fiscal 2023 annual dividend of $2.24 per share, an increase
over the fiscal 2022 annual dividend of $2.20 per share. For fiscal 2023, the annual dividend will be paid in four quarterly
installments of $0.56 per share, according to the following record and payable dates:
43

Record Date Payable Date
March 18, 2022 April 4, 2022
May 6, 2022 May 31, 2022
August 12, 2022 September 6, 2022
December 9, 2022 January 3, 2023
Company Share Repurchase Program
From time to time, the Company repurchases shares of its common stock under share repurchase programs authorized by the
Company's Board of Directors. All repurchases made prior to February 22, 2021 were made under the plan in effect at the
beginning of fiscal 2022. On February 18, 2021, the Board of Directors approved a new $20.0 billion share repurchase program
which has no expiration date or other restrictions limiting the period over which the Company can make repurchases, and
beginning February 22, 2021, replaced the previous share repurchase program. As of January 31, 2022, authorization for $10.6
billion of share repurchases remained under the share repurchase program. Any repurchased shares are constructively retired
and returned to an unissued status.
We regularly review share repurchase activity and consider several factors in determining when to execute share repurchases,
including, among other things, current cash needs, capacity for leverage, cost of borrowings, our results of operations and the
market price of our common stock. We anticipate that a majority of the ongoing share repurchase program will be funded
through the Company's free cash flow. In fiscal 2023, we plan to spend at least $10 billion in share repurchases.
The following table provides, on a settlement date basis, the number of shares repurchased, average price paid per share and
total amount paid for share repurchases for fiscal 2022, 2021 and 2020:
Fiscal Years Ended January 31,
(Amounts in millions, except per share data) 2022 2021 2020
Total number of shares repurchased 69.7 19.4 53.9
Average price paid per share $ 140.45 $ 135.20 $ 105.98
Total amount paid for share repurchases $ 9,787 $ 2,625 $ 5,717
Material Cash Requirements
Material cash requirements from operating activities primarily consist of inventory purchases, employee related costs, taxes,
interest and other general operating expenses, which we expect to be primarily satisfied by our cash from operations. Other
material cash requirements from known contractual and other obligations include short-term borrowings, long-term debt and
related interest payments, leases and purchase obligations. See Note 6 and Note 7 to our Consolidated Financial Statements for
information regarding outstanding short-term borrowings and long-term debt, and leases, respectively.
As of January 31, 2022, the Company has $27.9 billion of unrecorded purchase obligations outstanding, of which $9.3 billion is
due within one year. Purchase obligations include legally binding contracts, such as firm commitments for inventory and utility
purchases, as well as commitments to make capital expenditures, software acquisition and license commitments and legally
binding service contracts. Contractual obligations for the purchase of goods or services are defined as agreements that are
enforceable and legally binding and that specify all significant terms, including: fixed or minimum quantities to be purchased;
fixed, minimum or variable price provisions; and the approximate timing of the transaction. Contracts that specify the
Company will purchase all or a portion of its requirements of a specific product or service from a supplier, but do not include a
fixed or minimum quantity, are excluded from the obligations quantified above. Accordingly, purchase orders for inventory are
also excluded as purchase orders represent authorizations to purchase rather than binding agreements. Our purchase orders are
based on our current inventory needs and are fulfilled by our suppliers within short time periods. We also enter into contracts
for outsourced services; however, the obligations under these contracts are not significant and the contracts generally contain
clauses allowing for cancellation without significant penalty. Timing of payments and actual amounts paid may be different
depending on the timing of receipt of goods or services or changes to agreed-upon amounts for some obligations.
Capital Resources
We believe our cash flows from operations, current cash position, short-term borrowings and access to capital markets will
continue to be sufficient to meet our anticipated cash requirements and contractual obligations, which includes funding seasonal
buildups in merchandise inventories and funding our capital expenditures, acquisitions, dividend payments and share
repurchases.
We have strong commercial paper and long-term debt ratings that have enabled and should continue to enable us to refinance
our debt as it becomes due at favorable rates in capital markets. As of January 31, 2022, the ratings assigned to our commercial
paper and rated series of our outstanding long-term debt were as follows:
44

Rating agency Commercial paper Long-term debt
Standard & Poor's A-1+ AA
Moody's Investors Service P-1 Aa2
Fitch Ratings F1+ AA
Credit rating agencies review their ratings periodically and, therefore, the credit ratings assigned to us by each agency may be
subject to revision at any time. Accordingly, we are not able to predict whether our current credit ratings will remain consistent
over time. Factors that could affect our credit ratings include changes in our operating performance, the general economic
environment, conditions in the retail industry, our financial position, including our total debt and capitalization, and changes in
our business strategy. Any downgrade of our credit ratings by a credit rating agency could increase our future borrowing costs
or impair our ability to access capital and credit markets on terms commercially acceptable to us. In addition, any downgrade
of our current short-term credit ratings could impair our ability to access the commercial paper markets with the same flexibility
that we have experienced historically, potentially requiring us to rely more heavily on more expensive types of debt financing.
The credit rating agency ratings are not recommendations to buy, sell or hold our commercial paper or debt securities. Each
rating may be subject to revision or withdrawal at any time by the assigning rating organization and should be evaluated
independently of any other rating. Moreover, each credit rating is specific to the security to which it applies.
Other Matters
In Note 10 to our Consolidated Financial Statements, which is captioned "Contingencies" and appears in Part II of this Annual
Report on Form 10-K under the caption "Item 8. Financial Statements and Supplementary Data," we discuss, under the sub-
caption "Opioids Litigation," the Prescription Opiate Litigation and other matters, including certain risks arising therefrom. In
that Note 10, we also discuss, under the sub-caption "Asda Equal Value Claims," the Company's indemnification obligation for
the Asda Equal Value Claims matter. We discuss various legal proceedings related to the Federal and State Prescription Opiate
Litigation, DOJ Opioid Civil Litigation and Opioids Related Securities Class Actions and Derivative Litigation in Part I of this
Annual Report on Form 10-K under the caption "Item 3. Legal Proceedings," under the sub-caption "I. Supplemental
Information." We also discuss items related to the Asda Equal Value Claims matter, the Money Transfer Agent Services
Proceedings matter and the Foreign Direct Investment matters in Part I of this Annual Report on Form 10-K under the caption
"Item 3. Legal Proceedings," under the sub-caption "II. Certain Other Matters." We also discuss an environmental matter with
the State of California in Part I of this Annual Report on Form 10-K under the caption "Item 3. Legal Proceedings," under the
sub-caption "III. Environmental Matters." The foregoing matters and other matters described elsewhere in this Annual Report
on Form 10-K represent contingent liabilities of the Company that may or may not result in the incurrence of a material liability
by the Company upon their final resolution.
Summary of Critical Accounting Estimates
Management strives to report our financial results in a clear and understandable manner, although in some cases accounting and
disclosure rules are complex and require us to use technical terminology. In preparing the Company's Consolidated Financial
Statements, we follow accounting principles generally accepted in the U.S. These principles require us to make certain
estimates and apply judgments that affect our financial position and results of operations as reflected in our financial statements.
These judgments and estimates are based on past events and expectations of future outcomes. Actual results may differ from
our estimates.
Management continually reviews our accounting policies, how they are applied and how they are reported and disclosed in our
financial statements. Following is a summary of our critical accounting estimates and how they are applied in preparation of
the financial statements.
Inventories
We value inventories at the lower of cost or market as determined primarily by the retail inventory method of accounting, using
the last-in, first-out ("LIFO") method for Walmart U.S. segment's inventories. The inventory at the Sam's Club segment is
valued using the weighted-average cost LIFO method. When necessary, we record a LIFO provision for the estimated annual
effect of inflation, and these estimates are adjusted to actual results determined at year-end. Our LIFO provision is calculated
based on inventory levels, markup rates and internally generated retail price indices. As a measure of sensitivity, a 1% increase
to our retail price indices would not have resulted in a decrease to the carrying value of inventory. As of January 31, 2022 and
2021, our inventories valued at LIFO approximated those inventories as if they were valued at first-in, first-out ("FIFO").
45

Impairment of Assets
We evaluate long-lived assets for indicators of impairment whenever events or changes in circumstances indicate their carrying
amounts may not be recoverable. Management's judgments regarding the existence of impairment indicators are based on
market conditions and financial performance. The evaluation of long-lived assets is performed at the lowest level of
identifiable cash flows, which is generally at the individual store level. The variability of these factors depends on a number of
conditions, including uncertainty about future events and changes in demographics. Thus, our accounting estimates may
change from period to period. These factors could cause management to conclude that indicators of impairment exist and
require impairment tests be performed, which could result in management determining the value of long-lived assets is
impaired, resulting in a write-down of the related long-lived assets. Impairment charges on assets held and used were
immaterial in fiscal 2022, 2021 and 2020. As a measure of sensitivity, fiscal 2022 impairment would not change materially
with a 10% decrease in the undiscounted cash flows for the stores or clubs with indicators of impairment.
In fiscal 2021, the Company's operations in Argentina, the United Kingdom and Japan met the held for sale criteria. As a result,
the individual disposal groups were measured at fair value, less costs to sell, which resulted in impairment charges that were
included in the total estimated pre-tax loss of $8.3 billion recorded in fiscal 2021, as well as $0.4 billion in incremental charges
associated with the United Kingdom and Japan divestitures upon closing of the transactions during the first quarter of fiscal
2022. Refer to Note 12.
Business Combinations, Goodwill, and Acquired Intangible Assets
We account for business combinations using the acquisition method of accounting, which requires that once control is obtained,
all the assets acquired and liabilities assumed, including amounts attributable to noncontrolling interests, are recorded at their
respective fair values at the date of acquisition. The determination of fair values of identifiable assets and liabilities requires
estimates and the use of valuation techniques when market value is not readily available. For intangible assets acquired in a
business combination, we typically use the income method. Significant estimates in valuing certain intangible assets include,
but are not limited to, the amount and timing of future cash flows, growth rates, discount rates and useful lives. The excess of
the purchase price over fair values of identifiable assets and liabilities is recorded as goodwill.
Goodwill is typically assigned to the reporting unit which consolidates the acquisition. Components within the same reportable
segment are aggregated and deemed a single reporting unit if the components have similar economic characteristics. As of
January 31, 2022, our reporting units consisted of Walmart U.S., Walmart International and Sam's Club. Goodwill and other
indefinite-lived acquired intangible assets are not amortized but are evaluated for impairment annually or whenever events or
changes in circumstances indicate that the value of a certain asset may be impaired. Generally, this evaluation begins with a
qualitative assessment to determine whether a quantitative impairment test is necessary. If we determine, after performing an
assessment based on the qualitative factors, that the fair value of the reporting unit is more likely than not less than the carrying
amount, or that a fair value of the reporting unit substantially in excess of the carrying amount cannot be assured, then a
quantitative impairment test would be performed. The quantitative test for impairment requires management to make
judgments relating to future cash flows, growth rates and economic and market conditions. These evaluations are based on
determining the fair value of a reporting unit or asset using a valuation method such as discounted cash flow or a relative,
market-based approach. Historically, our reporting units have generated sufficient returns to recover the cost of goodwill, as
the fair value significantly exceeded the carrying value. Our indefinite-lived acquired intangible assets have also historically
generated sufficient returns to recover their cost. Because of the nature of the factors used in these tests, if different conditions
occur in future periods, future operating results could be materially impacted. Due to certain strategic restructuring decisions,
we recorded approximately $0.7 billion in impairment in fiscal 2020 related to acquired trade names and acquired developed
software.
Contingencies
We are involved in a number of legal proceedings. We record a liability when it is probable that a loss has been incurred and the
amount is reasonably estimable. We also perform an assessment of the materiality of loss contingencies where a loss is either
not probable or it is reasonably possible that a loss could be incurred in excess of amounts accrued. If a loss or an additional
loss has at least a reasonable possibility of occurring and the impact on the financial statements would be material, we provide
disclosure of the loss contingency in the footnotes to our financial statements. We review all contingencies at least quarterly to
determine whether the likelihood of loss has changed and to assess whether a reasonable estimate of the loss or the range of the
loss can be made. Although we are not able to predict the outcome or reasonably estimate a range of possible losses in certain
matters described in Note 10 to our Consolidated Financial Statements and have not recorded an associated accrual related to
these matters, an adverse judgment or negotiated resolution in any of these matters could have a material adverse effect on our
business, reputation, financial position, results of operations or cash flows.
46

Income Taxes
Income taxes have a significant effect on our net earnings. We are subject to income taxes in the U.S. and numerous foreign
jurisdictions. Accordingly, the determination of our provision for income taxes requires judgment, the use of estimates in
certain cases and the interpretation and application of complex tax laws. Our effective income tax rate is affected by many
factors, including changes in our assessment of certain tax contingencies, increases and decreases in valuation allowances,
changes in tax law, outcomes of administrative audits, the impact of discrete items and the mix of earnings among our U.S. and
international operations where the statutory rates are generally higher than the U.S. statutory rate, and may fluctuate as a result.
Our tax returns are routinely audited and settlements of issues raised in these audits sometimes affect our tax provisions. The
benefits of uncertain tax positions are recorded in our financial statements only after determining a more likely than not
probability that the uncertain tax positions will withstand challenge, if any, from taxing authorities. When facts and
circumstances change, we reassess these probabilities and record any changes in the financial statements as appropriate. We
account for uncertain tax positions by determining the minimum recognition threshold that a tax position is required to meet
before being recognized in the financial statements. This determination requires the use of judgment in evaluating our tax
positions and assessing the timing and amounts of deductible and taxable items.
Deferred tax assets represent amounts available to reduce income taxes payable on taxable income in future years. Such assets
arise because of temporary differences between the financial reporting and tax bases of assets and liabilities, as well as from net
operating loss and tax credit carryforwards. Deferred tax assets are evaluated for future realization and reduced by a valuation
allowance to the extent that a portion is not more likely than not to be realized. Many factors are considered when assessing
whether it is more likely than not that the deferred tax assets will be realized, including recent cumulative earnings, expectations
of future taxable income, carryforward periods and other relevant quantitative and qualitative factors. The recoverability of the
deferred tax assets is evaluated by assessing the adequacy of future expected taxable income from all sources, including reversal
of taxable temporary differences, forecasted operating earnings and available tax planning strategies. This evaluation relies on
estimates.
As guidance is issued by the U.S. Treasury Department, the IRS, and other standard-setting bodies, any resulting changes to our
estimates will be treated in accordance with the relevant accounting guidance.
ITEM 7A. QUANTITATIVE AND QUALITATIVE DISCLOSURES ABOUT MARKET RISK
Market Risk
In addition to the risks inherent in our operations, we are exposed to certain market risks, including changes in interest rates,
currency exchange rates and the fair value of certain equity investments.
The analysis presented below for each of our market risk sensitive instruments is based on a hypothetical scenario used to
calibrate potential risk and does not represent our view of future market changes. The effect of a change in a particular
assumption is calculated without adjusting any other assumption. In reality, however, a change in one factor could cause a
change in another, which may magnify or negate other sensitivities.
Interest Rate Risk
We are exposed to changes in interest rates as a result of our short-term borrowings and long-term debt. We hedge a portion of
our interest rate risk by managing the mix of fixed and variable rate debt and by entering into interest rate swaps. For fiscal
2022, the net fair value of our interest rate swaps decreased $0.2 billion primarily due to fluctuations in market interest rates.
The table below provides information about our financial instruments that are sensitive to changes in interest rates. For long-
term debt, the table represents the principal cash flows and related weighted-average interest rates by expected maturity dates.
For interest rate swaps, the table represents the contractual cash flows and weighted-average interest rates by the contractual
maturity date, unless otherwise noted. The notional amounts are used to calculate contractual cash flows to be exchanged under
the contracts. The weighted-average variable rates are based upon prevailing market rates as of January 31, 2022.
47

Expected Maturity Date
(Amounts in millions) Fiscal 2023 Fiscal 2024 Fiscal 2025 Fiscal 2026 Fiscal 2027 Thereafter Total
Liabilities
Short-term borrowings:
Variable rate $ 410 $ — $ — $ — $ — $ — $ 410
Weighted-average interest rate 2.9 % — % — % — % — % — % 2.9 %
Long-term debt
(1)
:
Fixed rate $ 2,803 $ 4,224 $ 3,565 $ 857 $ 2,757 $ 23,461 $ 37,667
Weighted-average interest rate 1.7 % 3.2 % 2.9 % 3.6 % 2.0 % 4.1 % 3.6 %
Interest rate derivatives
Interest rate swaps:
Fixed to variable $ — $ 1,750 $ 1,500 $ — $ — $ 4,771 $ 8,021
Weighted-average pay rate — % 0.7 % 1.4 % — % — % 1.3 % 1.2 %
Weighted-average receive rate — % 2.6 % 3.3 % — % — % 2.5 % 2.7 %
(1)
Includes deferred loan costs, discounts, fair value hedges, foreign-held debt and secured debt.
As of January 31, 2022, our variable rate borrowings, including the effect of our commercial paper and interest rate swaps,
represented 22% of our total short-term and long-term debt. Based on January 31, 2022 debt levels, a 100 basis point change in
prevailing market rates would cause our annual interest costs to change by approximately $0.1 billion.
Foreign Currency Risk
We are exposed to fluctuations in currency exchange rates as a result of our investments and operations in countries other than
the U.S., as well as our foreign-currency-denominated long-term debt. For fiscal 2022, movements in currency exchange rates
and the related impact on the translation of the balance sheets resulted in the $0.6 billion net loss in the currency translation and
other category of accumulated other comprehensive loss.
We hedge a portion of our foreign currency risk by entering into currency swaps. The aggregate fair value of these swaps was
in a liability position of $1.0 billion and $0.1 billion as of January 31, 2022 and January 31, 2021, respectively. The change in
the fair value of these swaps was due to fluctuations in currency exchange rates, primarily due to the strengthening of the U.S.
dollar relative to certain currencies in fiscal 2022. The hypothetical result of a uniform 10% weakening in the value of the U.S.
dollar relative to other currencies underlying these swaps would have resulted in a change in the value of the swaps of $1.0
billion. A hypothetical 10% change in interest rates underlying these swaps from the market rates in effect as of January 31,
2022 would have resulted in a change in the value of the swaps of $40 million.
In certain countries, we also enter into immaterial foreign currency forward contracts to hedge the purchase and payment of
purchase commitments denominated in non-functional currencies.
Investment Risk
We are exposed to investment risk primarily related to changes in the stock price of our equity investments with readily
determinable fair values. The change in fair value is recorded within other gains and losses and resulted in a loss of $2.4 billion
in fiscal 2022 due to net decreases in the stock price of those equity investments. As of January 31, 2022, the fair value of our
equity investments with readily determinable fair values was $11.9 billion. As of January 31, 2022, a hypothetical 10% change
in the stock price of such investments would have changed the fair value of such investments by approximately $1.2 billion.
48

ITEM 8. FINANCIAL STATEMENTS AND SUPPLEMENTARY DATA
Consolidated Financial Statements of Walmart Inc.
For the Fiscal Year Ended January 31, 2022
Table of Contents
Page
Report of Independent Registered Public Accounting Firm (PCAOB ID: 42) 50
Report of Independent Registered Public Accounting Firm on Internal Control over Financial Reporting 52
Consolidated Statements of Income 53
Consolidated Statements of Comprehensive Income 54
Consolidated Balance Sheets 55
Consolidated Statements of Shareholders' Equity 56
Consolidated Statements of Cash Flows 57
Notes to Consolidated Financial Statements 58
49
Report of Independent Registered Public Accounting Firm
To the Shareholders and the Board of Directors of Walmart Inc.
Opinion on the Financial Statements
We have audited the accompanying consolidated balance sheets of Walmart Inc. (the Company) as of January 31, 2022 and
2021, the related consolidated statements of income, comprehensive income, shareholders' equity and cash flows for each of the
three years in the period ended January 31, 2022, and the related notes (collectively referred to as the "Consolidated Financial
Statements"). In our opinion, the Consolidated Financial Statements present fairly, in all material respects, the financial
position of the Company at January 31, 2022 and 2021, and the results of its operations and its cash flows for each of the three
years in the period ended January 31, 2022, in conformity with U.S. generally accepted accounting principles.
We also have audited, in accordance with the standards of the Public Company Accounting Oversight Board (United States)
(PCAOB), the Company's internal control over financial reporting as of January 31, 2022, based on criteria established in
Internal Control-Integrated Framework issued by the Committee of Sponsoring Organizations of the Treadway Commission
(2013 framework) and our report dated March 18, 2022 expressed an unqualified opinion thereon.
Basis for Opinion
These financial statements are the responsibility of the Company's management. Our responsibility is to express an opinion on
the Company's financial statements based on our audits. We are a public accounting firm registered with the PCAOB and are
required to be independent with respect to the Company in accordance with the U.S. federal securities laws and the applicable
rules and regulations of the Securities and Exchange Commission and the PCAOB.
We conducted our audits in accordance with the standards of the PCAOB. Those standards require that we plan and perform the
audit to obtain reasonable assurance about whether the financial statements are free of material misstatement, whether due to
error or fraud. Our audits included performing procedures to assess the risks of material misstatement of the financial
statements, whether due to error or fraud, and performing procedures that respond to those risks. Such procedures included
examining, on a test basis, evidence regarding the amounts and disclosures in the financial statements. Our audits also included
evaluating the accounting principles used and significant estimates made by management, as well as evaluating the overall
presentation of the financial statements. We believe that our audits provide a reasonable basis for our opinion.
Critical Audit Matter
The critical audit matter communicated below is a matter arising from the current period audit of the financial statements that
was communicated or required to be communicated to the audit committee and that: (1) relates to accounts or disclosures that
are material to the financial statements and (2) involved our especially challenging, subjective or complex judgments. The
communication of the critical audit matter does not alter in any way our opinion on the Consolidated Financial Statements,
taken as a whole, and we are not, by communicating the critical audit matter below, providing a separate opinion on the critical
audit matter or on the account or disclosure to which it relates.
Contingencies
Description of
the Matter
As described in Note 10 to the Consolidated Financial Statements, at January 31, 2022, the Company is
involved in a number of legal proceedings and has made accruals with respect to these matters, where
appropriate. For some matters, a liability is not probable, or the amount cannot be reasonably estimated
and therefore an accrual has not been made. Where a liability is reasonably possible and may be material,
such matters have been disclosed. Management assessed the probability of occurrence and the estimation
of any potential loss based on the ability to predict the number of claims that may be filed or whether any
loss or range of loss can be reasonably estimated. For example, in assessing the probability of occurrence
in a particular legal proceeding, management exercises judgment to determine if it can predict the
number of claims that may be filed and whether it can reasonably estimate any loss or range of loss that
may arise from that proceeding.
Auditing management's accounting for, and disclosure of, loss contingencies was complex and highly
judgmental as it involved our assessment of the significant judgments made by management when
assessing the probability of occurrence for contingencies or when determining whether an estimate of the
loss or range of loss could be made.
50
How We
Addressed the
Matter in Our
Audit
We obtained an understanding, evaluated the design and tested the operating effectiveness of controls
over the identification and evaluation of contingencies. For example, we tested controls over the
Company's assessment of the likelihood of loss and the Company's determinations regarding the
measurement of loss.
To test the Company's assessment of the probability of occurrence or determination of an estimate of
loss, or range of loss, among other procedures, we read the minutes of the meetings of the Board of
Directors and committees of the Board of Directors, reviewed opinions provided to the Company by
certain outside legal counsel, read letters received directly by us from internal and external counsel, and
evaluated the current status of contingencies based on discussions with internal legal counsel. We also
evaluated the appropriateness of the related disclosures.
/s/ Ernst & Young LLP
We have served as the Company's auditor since 1969.
Rogers, Arkansas
March 18, 2022
51
Report of Independent Registered Public Accounting Firm
To the Shareholders and the Board of Directors of Walmart Inc.
Opinion on Internal Control over Financial Reporting
We have audited Walmart Inc.'s internal control over financial reporting as of January 31, 2022, based on criteria established in
Internal Control—Integrated Framework issued by the Committee of Sponsoring Organizations of the Treadway Commission
(2013 framework) (the COSO criteria). In our opinion, Walmart Inc. (the Company) maintained, in all material respects,
effective internal control over financial reporting as of January 31, 2022, based on the COSO criteria.
We also have audited, in accordance with the standards of the Public Company Accounting Oversight Board (United States)
(PCAOB), the consolidated balance sheets of Walmart Inc. as of January 31, 2022 and 2021, the related consolidated statements
of income, comprehensive income, shareholders' equity and cash flows for each of the three years in the period ended
January 31, 2022, and the related notes and our report dated March 18, 2022 expressed an unqualified opinion thereon.
Basis for Opinion
The Company's management is responsible for maintaining effective internal control over financial reporting and for its
assessment of the effectiveness of internal control over financial reporting included in the accompanying Report on Internal
Control over Financial Reporting. Our responsibility is to express an opinion on the Company's internal control over financial
reporting based on our audit. We are a public accounting firm registered with the PCAOB and are required to be independent
with respect to the Company in accordance with the U.S. federal securities laws and the applicable rules and regulations of the
Securities and Exchange Commission and the PCAOB.
We conducted our audit in accordance with the standards of the PCAOB. Those standards require that we plan and perform the
audit to obtain reasonable assurance about whether effective internal control over financial reporting was maintained in all
material respects.
Our audit included obtaining an understanding of internal control over financial reporting, assessing the risk that a material
weakness exists, testing and evaluating the design and operating effectiveness of internal control based on the assessed risk, and
performing such other procedures as we considered necessary in the circumstances. We believe that our audit provides a
reasonable basis for our opinion.
Definition and Limitations of Internal Control over Financial Reporting
A company's internal control over financial reporting is a process designed to provide reasonable assurance regarding the
reliability of financial reporting and the preparation of financial statements for external purposes in accordance with generally
accepted accounting principles. A company's internal control over financial reporting includes those policies and procedures
that (1) pertain to the maintenance of records that, in reasonable detail, accurately and fairly reflect the transactions and
dispositions of the assets of the company; (2) provide reasonable assurance that transactions are recorded as necessary to permit
preparation of financial statements in accordance with generally accepted accounting principles, and that receipts and
expenditures of the company are being made only in accordance with authorizations of management and directors of the
company; and (3) provide reasonable assurance regarding prevention or timely detection of unauthorized acquisition, use, or
disposition of the company's assets that could have a material effect on the financial statements.
Because of its inherent limitations, internal control over financial reporting may not prevent or detect misstatements. Also,
projections of any evaluation of effectiveness to future periods are subject to the risk that controls may become inadequate
because of changes in conditions, or that the degree of compliance with the policies or procedures may deteriorate.
/s/ Ernst & Young LLP
Rogers, Arkansas
March 18, 2022
52

Walmart Inc.
Consolidated Statements of Income
Fiscal Years Ended January 31,
(Amounts in millions, except per share data) 2022 2021 2020
Revenues:
Net sales $ 567,762 $ 555,233 $ 519,926
Membership and other income 4,992 3,918 4,038
Total revenues 572,754 559,151 523,964
Costs and expenses:
Cost of sales
429,000 420,315 394,605
Operating, selling, general and administrative expenses
117,812 116,288 108,791
Operating income
25,942 22,548 20,568
Interest:
Debt
1,674 1,976 2,262
Finance lease
320 339 337
Interest income
(158) (121) (189)
Interest, net
1,836 2,194 2,410
Loss on extinguishment of debt
2,410 — —
Other (gains) and losses
3,000 (210) (1,958)
Income before income taxes
18,696 20,564 20,116
Provision for income taxes
4,756 6,858 4,915
Consolidated net income
13,940 13,706 15,201
Consolidated net income attributable to noncontrolling interest
(267) (196) (320)
Consolidated net income attributable to Walmart
$ 13,673 $ 13,510 $ 14,881
Net income per common share:
Basic net income per common share attributable to Walmart $ 4.90 $ 4.77 $ 5.22
Diluted net income per common share attributable to Walmart 4.87 4.75 5.19
Weighted-average common shares outstanding:
Basic
2,792 2,831 2,850
Diluted
2,805 2,847 2,868
Dividends declared per common share
$ 2.20 $ 2.16 $ 2.12
See accompanying notes.
53

Walmart Inc.
Consolidated Statements of Comprehensive Income
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Consolidated net income
$ 13,940 $ 13,706 $ 15,201
Consolidated net income attributable to noncontrolling interest (267) (196) (320)
Consolidated net income attributable to Walmart
13,673 13,510 14,881
Other comprehensive income (loss), net of income taxes
Currency translation and other 2,442 842 286
Net investment hedges (1,202) (221) 122
Cash flow hedges (444) 235 (399)
Minimum pension liability 1,974 (30) (1,244)
Other comprehensive income (loss), net of income taxes 2,770 826 (1,235)
Other comprehensive (income) loss attributable to noncontrolling interest 230 213 (28)
Other comprehensive income (loss) attributable to Walmart
3,000 1,039 (1,263)
Comprehensive income, net of income taxes 16,710 14,532 13,966
Comprehensive (income) loss attributable to noncontrolling interest
(37) 17 (348)
Comprehensive income attributable to Walmart
$ 16,673 $ 14,549 $ 13,618
See accompanying notes.
54

Walmart Inc.
Consolidated Balance Sheets
As of January 31,
(Amounts in millions) 2022 2021
ASSETS
Current assets:
Cash and cash equivalents $ 14,760 $ 17,741
Receivables, net 8,280 6,516
Inventories 56,511 44,949
Prepaid expenses and other 1,519 20,861
Total current assets 81,070 90,067
Property and equipment, net 94,515 92,201
Operating lease right-of-use assets 13,758 13,642
Finance lease right-of-use assets, net 4,351 4,005
Goodwill 29,014 28,983
Other long-term assets
22,152 23,598
Total assets
$ 244,860 $ 252,496
LIABILITIES AND EQUITY
Current liabilities:
Short-term borrowings $ 410 $ 224
Accounts payable 55,261 49,141
Accrued liabilities 26,060 37,966
Accrued income taxes 851 242
Long-term debt due within one year 2,803 3,115
Operating lease obligations due within one year 1,483 1,466
Finance lease obligations due within one year 511 491
Total current liabilities 87,379 92,645
Long-term debt 34,864 41,194
Long-term operating lease obligations 13,009 12,909
Long-term finance lease obligations 4,243 3,847
Deferred income taxes and other 13,474 14,370
Commitments and contingencies
Equity:
Common stock 276 282
Capital in excess of par value 4,839 3,646
Retained earnings 86,904 88,763
Accumulated other comprehensive loss (8,766) (11,766)
Total Walmart shareholders' equity 83,253 80,925
Noncontrolling interest 8,638 6,606
Total equity 91,891 87,531
Total liabilities and equity
$ 244,860 $ 252,496
See accompanying notes.
55

Walmart Inc.
Consolidated Statements of Shareholders' Equity
Accumulated Total
Capital in Other Walmart
(Amounts in millions)
Common Stock Excess of Retained Comprehensive Shareholders' Noncontrolling Total
Shares Amount Par Value Earnings Income (Loss) Equity Interest Equity
Balances as of February 1,
2019
2,878 $ 288 $ 2,965 $ 80,785 $ (11,542) $ 72,496 $ 7,138 $ 79,634
Adoption of new accounting
standards, net of income
taxes
— — — (266) — (266) (34) (300)
Consolidated net income — — — 14,881 — 14,881 320 15,201
Other comprehensive income
(loss), net of income taxes
— — — — (1,263) (1,263) 28 (1,235)
Cash dividends declared
($2.12 per share)
— — — (6,048) — (6,048) — (6,048)
Purchase of Company stock (53) (5) (199) (5,435) — (5,639) — (5,639)
Cash dividend declared to
noncontrolling interest
— — — — — — (475) (475)
Sale of subsidiary stock — — 37 — — 37 15 52
Other 7 1 444 26 — 471 (109) 362
Balances as of January 31,
2020
2,832 284 3,247 83,943 (12,805) 74,669 6,883 81,552
Consolidated net income — — — 13,510 — 13,510 196 13,706
Other comprehensive income
(loss), net of income taxes
— — — — 1,039 1,039 (213) 826
Cash dividends declared
($2.16 per share)
— — — (6,116) — (6,116) — (6,116)
Purchase of Company stock (20) (2) (97) (2,559) — (2,658) — (2,658)
Cash dividend declared to
noncontrolling interest
— — — — — — (365) (365)
Sale of subsidiary stock — — 29 — — 29 111 140
Other 9 — 467 (15) — 452 (6) 446
Balances as of January 31,
2021
2,821 282 3,646 88,763 (11,766) 80,925 6,606 87,531
Consolidated net income — — 13,673 — 13,673 267 13,940
Other comprehensive income
(loss), net of income taxes
— — — — 3,000 3,000 (230) 2,770
Cash dividends declared
($2.20 per share)
— — — (6,152) — (6,152) — (6,152)
Purchase of Company stock (70) (7) (426) (9,375) — (9,808) — (9,808)
Cash dividend declared to
noncontrolling interest
— — — — — — (416) (416)
Sale of subsidiary stock — — 952 — — 952 2,287 3,239
Other 10 1 667 (5) — 663 124 787
Balances as of January 31,
2022
2,761 $ 276 $ 4,839 $ 86,904 $ (8,766) $ 83,253 $ 8,638 $ 91,891
See accompanying notes.
56

Walmart Inc.
Consolidated Statements of Cash Flows
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Cash flows from operating activities:
Consolidated net income $ 13,940 $ 13,706 $ 15,201
Adjustments to reconcile consolidated net income to net cash provided by operating activities:
Depreciation and amortization 10,658 11,152 10,987
Net unrealized and realized (gains) and losses 2,440 (8,589) (1,886)
Losses on disposal of business operations 433 8,401 15
Asda pension contribution — — (1,036)
Deferred income taxes (755) 1,911 320
Loss on extinguishment of debt 2,410 — —
Other operating activities 1,652 1,521 1,981
Changes in certain assets and liabilities, net of effects of acquisitions and dispositions:
Receivables, net (1,796) (1,086) 154
Inventories (11,764) (2,395) (300)
Accounts payable 5,520 6,966 (274)
Accrued liabilities 1,404 4,623 186
Accrued income taxes 39 (136) (93)
Net cash provided by operating activities 24,181 36,074 25,255
Cash flows from investing activities:
Payments for property and equipment (13,106) (10,264) (10,705)
Proceeds from the disposal of property and equipment 394 215 321
Proceeds from disposal of certain operations, net of divested cash 7,935 56 833
Payments for business acquisitions, net of cash acquired (359) (180) (56)
Other investing activities (879) 102 479
Net cash used in investing activities (6,015) (10,071) (9,128)
Cash flows from financing activities:
Net change in short-term borrowings 193 (324) (4,656)
Proceeds from issuance of long-term debt 6,945 — 5,492
Repayments of long-term debt (13,010) (5,382) (1,907)
Premiums paid to extinguish debt (2,317) — —
Dividends paid (6,152) (6,116) (6,048)
Purchase of Company stock (9,787) (2,625) (5,717)
Dividends paid to noncontrolling interest (424) (434) (555)
Sale of subsidiary stock 3,239 140 52
Other financing activities (1,515) (1,376) (960)
Net cash used in financing activities (22,828) (16,117) (14,299)
Effect of exchange rates on cash, cash equivalents and restricted cash (140) 235 (69)
Net increase (decrease) in cash, cash equivalents and restricted cash (4,802) 10,121 1,759
Change in cash and cash equivalents reclassified from (to) assets held for sale 1,848 (1,848) —
Cash, cash equivalents and restricted cash at beginning of year 17,788 9,515 7,756
Cash, cash equivalents and restricted cash at end of year $ 14,834 $ 17,788 $ 9,515
Supplemental disclosure of cash flow information:
Income taxes paid $ 5,918 $ 5,271 $ 3,616
Interest paid 2,237 2,216 2,464
See accompanying notes.
57
Walmart Inc.
Notes to Consolidated Financial Statements
Note 1. Summary of Significant Accounting Policies
General
Walmart Inc. ("Walmart" or the "Company") helps people around the world save money and live better – anytime and
anywhere – by providing the opportunity to shop in both retail stores and through eCommerce. Through innovation, the
Company is striving to continuously improve a customer-centric experience that seamlessly integrates eCommerce and retail
stores in an omni-channel offering that saves time for its customers.
The Company's operations comprise three reportable segments: Walmart U.S., Walmart International and Sam's Club.
Principles of Consolidation
The Consolidated Financial Statements include the accounts of Walmart and its subsidiaries as of and for the fiscal years ended
January 31, 2022 ("fiscal 2022"), January 31, 2021 ("fiscal 2021") and January 31, 2020 ("fiscal 2020"). Intercompany
accounts and transactions have been eliminated in consolidation. Certain previously reported amounts have been reclassified to
conform to the current year presentation. The Company consolidates variable interest entities where it has been determined that
the Company is the primary beneficiary of those entities' operations. Investments for which the Company exercises significant
influence but does not have control are accounted for under the equity method. These variable interest entities and equity
method investments are immaterial to the Company's Consolidated Financial Statements.
The Company's Consolidated Financial Statements are based on a fiscal year ending on January 31 for the United States
("U.S.") and Canadian operations. The Company consolidates all other operations generally using a one-month lag and based
on a calendar year. There were no significant intervening events during the month of January 2022 related to the operations
consolidated using a lag that materially affected the Consolidated Financial Statements.
Use of Estimates
The Consolidated Financial Statements have been prepared in conformity with U.S. generally accepted accounting principles.
Those principles require management to make estimates and assumptions that affect the reported amounts of assets and
liabilities. Management's estimates and assumptions also affect the disclosure of contingent assets and liabilities at the date of
the financial statements and the reported amounts of revenues and expenses during the reporting period. Actual results may
differ from those estimates.
Cash and Cash Equivalents
The Company considers investments with a maturity when purchased of three months or less to be cash equivalents. All credit
card, debit card and electronic transfer transactions that process in less than seven days are classified as cash and cash
equivalents. The amounts due from banks for these transactions classified as cash and cash equivalents totaled $1.7 billion and
$4.1 billion as of January 31, 2022 and 2021, respectively.
The Company's cash balances are held in various locations around the world. Of the Company's $14.8 billion and $17.7 billion
in cash and cash equivalents as of January 31, 2022 and January 31, 2021, approximately 50% and 40% were held outside of
the U.S., respectively. Cash and cash equivalents held outside of the U.S. are generally utilized to support liquidity needs in the
Company's non-U.S. operations.
The Company uses intercompany financing arrangements in an effort to ensure cash can be made available in the country in
which it is needed with the minimum cost possible.
As of January 31, 2022 and 2021, cash and cash equivalents of approximately $4.3 billion and $2.8 billion, respectively, may
not be freely transferable to the U.S. due to local laws or other restrictions. Of the $4.3 billion as of January 31, 2022,
approximately $2.2 billion can only be accessed through dividends or intercompany financing arrangements subject to approval
of Flipkart Private Limited ("Flipkart") minority shareholders.
Receivables
Receivables are stated at their carrying values, net of a reserve for doubtful accounts, and are primarily due from the following:
customers, which includes pharmacy insurance companies as well as advertisers, and banks for customer credit, debit cards and
electronic transfer transactions that take in excess of seven days to process; suppliers for marketing or incentive programs;
governments for income taxes; and real estate transactions. As of January 31, 2022 and January 31, 2021, net receivables from
transactions with customers were $3.4 billion and $2.7 billion, respectively.
58

Inventories
The Company values inventories at the lower of cost or market as determined primarily by the retail inventory method of
accounting, using the last-in, first-out ("LIFO") method for the Walmart U.S. segment's inventories. The inventory for the
Walmart International segment is generally valued in most markets by the retail inventory method of accounting, using the first-
in, first-out ("FIFO") method. The retail inventory method of accounting results in inventory being valued at the lower of cost
or market, since permanent markdowns are immediately recorded as a reduction of the retail value of inventory. The inventory
at the Sam's Club segment is valued using the weighted-average cost LIFO method. As of January 31, 2022 and 2021,
inventories valued at LIFO approximated those inventories as if they were valued at first-in, first-out ("FIFO").
Held for Sale
Components and businesses that meet accounting requirements to be classified as held for sale are presented as single asset and
liability amounts in the Company's financial statements with a valuation allowance, if necessary, to recognize the net carrying
amount at the lower of cost or fair value, less costs to sell. The Company reviews its businesses and assets held for sale each
reporting period to determine whether the existing carrying amounts are fully recoverable in comparison to estimated fair
values. As of January 31, 2022, assets and liabilities held for sale were immaterial. As of January 31, 2021, $19.2 billion assets
held for sale and $12.7 billion liabilities held for sale were classified in prepaid expenses and other and accrued liabilities in the
Consolidated Balance Sheets, respectively, reflecting the Company's operations in the U.K. and Japan classified as held for sale
which subsequently closed during fiscal 2022. Refer to Note 12 for additional details.
Property and Equipment
Property and equipment are initially recorded at cost. Gains or losses on disposition are recognized as earned or incurred.
Costs of major improvements are capitalized, while costs of normal repairs and maintenance are expensed as incurred. The
following table summarizes the Company's property and equipment balances and includes the estimated useful lives that are
generally used to depreciate the assets on a straight-line basis:
As of January 31,
(Amounts in millions) Estimated Useful Lives 2022 2021
Land N/A $ 19,204 $ 19,308
Buildings and improvements 3 - 40 years 100,376 97,582
Fixtures and equipment 1 - 30 years 60,282 56,639
Transportation equipment 3 - 15 years 2,263 2,301
Construction in progress N/A 7,199 4,741
Property and equipment
189,324 180,571
Accumulated depreciation (94,809) (88,370)
Property and equipment, net
$ 94,515 $ 92,201
Leasehold improvements are depreciated or amortized over the shorter of the estimated useful life of the asset or the remaining
expected lease term. Total depreciation and amortization expense for property and equipment, property under finance leases
and intangible assets for fiscal 2022, 2021 and 2020 was $10.7 billion, $11.2 billion and $11.0 billion, respectively.
Leases
For any new or modified lease, the Company, at the inception of the contract, determines whether a contract is or contains a
lease. The Company records right-of-use ("ROU") assets and lease obligations for its finance and operating leases, which are
initially recognized based on the discounted future lease payments over the term of the lease. If the rate implicit in the
Company's leases is not easily determinable, the Company's applicable incremental borrowing rate is used in calculating the
present value of the sum of the lease payments.
Lease term is defined as the non-cancelable period of the lease plus any options to extend or terminate the lease when it is
reasonably certain that the Company will exercise the option. The Company has elected not to recognize ROU asset and lease
obligations for its short-term leases, which are defined as leases with an initial term of 12 months or less.
For a majority of all classes of underlying assets, the Company has elected to not separate lease from non-lease components.
For leases in which the lease and non-lease components have been combined, the variable lease expense includes expenses such
as common area maintenance, utilities, and repairs and maintenance.
59

Impairment of Long-Lived Assets
Management reviews long-lived assets for indicators of impairment whenever events or changes in circumstances indicate that
the carrying amount may not be recoverable. The evaluation is performed at the lowest level of identifiable cash flows, which
is at the individual store or club level. Undiscounted cash flows expected to be generated by the related assets are estimated
over the assets' useful lives based on updated projections. If the evaluation indicates that the carrying amount of the assets may
not be recoverable, any potential impairment is measured based upon the fair value of the related asset or asset group as
determined by an appropriate market appraisal or other valuation technique.
Goodwill and Other Acquired Intangible Assets
Goodwill represents the excess of the purchase price over the fair value of net assets acquired in business combinations and is
allocated to the appropriate reporting unit when acquired. Other acquired intangible assets are stated at the fair value acquired
as determined by a valuation technique commensurate with the intended use of the related asset. Goodwill and indefinite-lived
intangible assets are not amortized; rather, they are evaluated for impairment annually and whenever events or changes in
circumstances indicate that the value of the asset may be impaired. Definite-lived intangible assets are considered long-lived
assets and are amortized on a straight-line basis over the periods that expected economic benefits will be provided.
Goodwill is typically assigned to the reporting unit which consolidates the acquisition. Components within the same reportable
segment are aggregated and deemed a single reporting unit if the components have similar economic characteristics. As of
January 31, 2022, the Company's reporting units consisted of Walmart U.S., Walmart International and Sam's Club. Goodwill
is evaluated for impairment using either a qualitative or quantitative approach for each of the Company's reporting units.
Generally, a qualitative assessment is first performed to determine whether a quantitative goodwill impairment test is necessary.
If management determines, after performing an assessment based on the qualitative factors, that the fair value of the reporting
unit is more likely than not less than the carrying amount, or that a fair value of the reporting unit substantially in excess of the
carrying amount cannot be assured, then a quantitative goodwill impairment test would be required. The quantitative test for
goodwill impairment is performed by determining the fair value of the related reporting units. Fair value is measured based on
the discounted cash flow method and relative market-based approaches. Management has performed its evaluation and
determined the fair value of each reporting unit is significantly greater than the carrying amount and, accordingly, the Company
has not recorded any impairment charges related to goodwill.
The following table reflects goodwill activity, by reportable segment, for fiscal 2022 and 2021:
(Amounts in millions) Walmart U.S.
Walmart
International Sam's Club Total
Balances as of February 1, 2020
$ 2,593 $ 28,167 $ 313 $ 31,073
Changes in currency translation and other — 10 — 10
Acquisitions 103 — 8 111
Amounts reclassified related to operations held for sale
(1)
— (2,211) — (2,211)
Balances as of January 31, 2021
2,696 25,966 321 28,983
Changes in currency translation and other — (415) — (415)
Acquisitions 245 201 — 446
Balances as of January 31, 2022
$ 2,941 $ 25,752 $ 321 $ 29,014
(1)
Represents goodwill associated with operations in the U.K. and Japan which were classified as held for sale as of January 31, 2021. Refer to Note 12.
Intangible assets are recorded in other long-term assets in the Company's Consolidated Balance Sheets. As of January 31, 2022
and 2021, the Company had $4.8 billion and $4.9 billion, respectively, in indefinite-lived intangible assets which primarily
consists of acquired trade names. There were no significant impairment charges related to intangible assets for fiscal 2022 or
2021. During fiscal 2020, the Company incurred approximately $0.7 billion in impairment charges related to its intangible
assets. Refer to Note 8 for additional information.
Fair Value Measurement
The Company records and discloses certain financial and non-financial assets and liabilities at fair value. The fair value of an
asset is the price at which the asset could be sold in an orderly transaction between unrelated, knowledgeable and willing parties
able to engage in the transaction. The fair value of a liability is the amount that would be paid to transfer the liability to a new
obligor in a transaction between such parties, not the amount that would be paid to settle the liability with the creditor. Refer to
Note 8 for more information.
Investments
Investments in equity and debt securities are recorded in other long-term assets in the Consolidated Balance Sheets. Changes in
fair value of equity securities measured on a recurring basis are recognized in other gains and losses in the Consolidated
Statements of Income. Refer to Note 8 for details. Equity investments without readily determinable fair values are carried at
cost and adjusted for any observable price changes or impairments within other gains and losses in the Consolidated Statements
60

of Income. Investments in debt securities classified as trading are reported at fair value with interest income recorded in interest
income in the Consolidated Statements of Income. As of January 31, 2022, the Company had $1.0 billion in debt securities
classified as trading.
Indemnification Liabilities
The Company has provided certain indemnifications in connection with its divestitures and has recorded indemnification
liabilities equal to the estimated fair value of the obligations upon inception. As of January 31, 2022 and January 31, 2021, the
Company had $0.7 billion and $0.6 billion, respectively, of certain legal and tax indemnification liabilities recorded within
deferred income taxes and other in the Consolidated Balance Sheets. The maximum amount of potential future payments under
these indemnities was $3.5 billion, based on exchange rates as of January 31, 2022.
Self Insurance Reserves
The Company self-insures a number of risks, including, but not limited to, workers' compensation, general liability, auto
liability, product liability and certain employee-related healthcare benefits. Standard actuarial procedures and data analysis are
used to estimate the liabilities associated with these risks on an undiscounted basis. The recorded liabilities reflect the ultimate
cost for claims incurred but not paid and any estimable administrative run-out expenses related to the processing of these
outstanding claim payments. On a regular basis, the liabilities are evaluated for appropriateness with claims reserve valuations.
To limit exposure to some risks, the Company maintains insurance coverage with varying limits and retentions, including stop-
loss insurance coverage for workers' compensation, general liability and auto liability.
Derivatives
The Company uses derivatives for hedging purposes to manage its exposure to changes in interest and currency exchange rates,
as well as to maintain an appropriate mix of fixed- and variable-rate debt. Use of derivatives in hedging programs subjects the
Company to certain risks, such as market and credit risks. The Company may be exposed to credit-related losses in the event of
nonperformance by its counterparties to derivatives. Credit risk is monitored through established approval procedures,
including setting concentration limits by counterparty, reviewing credit ratings and requiring collateral from the counterparty.
The Company enters into derivatives with counterparties rated generally "A-" or better by nationally recognized credit rating
agencies. The Company is subject to master netting arrangements which provides set-off and close-out netting of exposures
with counterparties, but the Company does not offset derivative assets and liabilities in its Consolidated Balance Sheets. The
Company's collateral arrangements require the counterparty in a net liability position in excess of pre-determined thresholds,
after considering the effects of netting arrangements, to pledge cash collateral. Cash collateral received from counterparties and
cash collateral provided to counterparties under these arrangements was not significant as of January 31, 2022 and 2021.
In order to qualify for hedge accounting, at the inception of the hedging relationship, the Company formally documents its risk
management objective and strategy for undertaking the hedging transaction, as well as its designation of the hedge. If a
derivative is recorded using hedge accounting, depending on the nature of the hedge, derivative gains and losses are recorded
through the same financial statement line item in earnings or are recognized in accumulated other comprehensive loss until the
hedged item is recognized in earnings. Derivatives that do not meet the criteria for hedge accounting, or contracts for which the
Company has not elected hedge accounting, are recorded at fair value with unrealized gains or losses reported in earnings.
Derivatives with an unrealized gain are recorded in the Company's Consolidated Balance Sheets as either current or non-current
assets, based on maturity date, and derivatives with an unrealized loss are recorded as either current or non-current liabilities,
based on maturity date. Refer to Note 8 for the presentation of the Company's derivative assets and liabilities.
Fair Value Hedges
The Company is a party to receive fixed-rate, pay variable-rate interest rate swaps that the Company uses to hedge the fair value
of fixed-rate debt. All interest rate swaps designated as fair value hedges of the related long-term debt meet the shortcut
method requirements under U.S. GAAP. Accordingly, changes in the fair values of these interest rate swaps are considered to
exactly offset changes in the fair value of the underlying long-term debt. These derivatives will mature on dates ranging from
April 2023 to September 2031.
Cash Flow Hedges
The Company is a party to receive fixed-rate, pay fixed-rate cross currency interest rate swaps used to hedge the currency
exposure associated with the forecasted payments of principal and interest of certain non-U.S. denominated debt. The
Company records changes in the fair value of these swaps in accumulated other comprehensive loss which is subsequently
reclassified into earnings in the period that the hedged forecasted transaction affects earnings. These derivatives will mature on
dates ranging from April 2022 to January 2039.
61

Net Investment Hedges
Prior to the divestiture of the Company's operations in the United Kingdom and Japan as discussed in Note 12, the Company
was a party to receive fixed-rate, pay fixed-rate cross currency interest rate swaps used to hedge the currency exposure
associated with net investments of these foreign operations. Changes in fair value attributable to the hedged risk were recorded
in accumulated other comprehensive loss. The Company also previously designated certain foreign currency denominated
long-term debt as a hedge of currency exposure associated with the net investment of these divested operations and recorded
foreign currency gain or loss associated with designated long-term debt in accumulated other comprehensive loss. Upon
closing of the sale of the Company's operations in the U.K. and Japan during the first quarter of fiscal 2022, these amounts were
released from accumulated other comprehensive loss as discussed in Note 4. As of January 31, 2021, the Company had
$3.3 billion of outstanding long-term debt designated as net investment hedges.
Income Taxes
Income taxes are accounted for under the balance sheet method. Deferred tax assets and liabilities are recognized for the
estimated future tax consequences attributable to differences between the financial statement carrying amounts of existing
assets and liabilities and their respective tax bases ("temporary differences"). Deferred tax assets and liabilities are measured
using enacted tax rates in effect for the year in which those temporary differences are expected to be recovered or settled. The
effect on deferred tax assets and liabilities of a change in tax rate is recognized in income in the period that includes the
enactment date.
Deferred tax assets are evaluated for future realization and reduced by a valuation allowance to the extent that a portion is not
more likely than not to be realized. Many factors are considered when assessing whether it is more likely than not that the
deferred tax assets will be realized, including recent cumulative earnings, expectations of future taxable income, carryforward
periods, and other relevant quantitative and qualitative factors. The recoverability of the deferred tax assets is evaluated by
assessing the adequacy of future expected taxable income from all sources, including reversal of taxable temporary differences,
forecasted operating earnings and available tax planning strategies. These sources of income rely on estimates.
In determining the provision for income taxes, an annual effective income tax rate is used based on annual income, permanent
differences between book and tax income, and statutory income tax rates. Discrete events such as audit settlements or changes
in tax laws are recognized in the period in which they occur.
The Company records a liability for unrecognized tax benefits resulting from uncertain tax positions taken or expected to be
taken in a tax return. The Company records interest and penalties related to unrecognized tax benefits in interest expense and
operating, selling, general and administrative expenses, respectively, in the Company's Consolidated Statements of Income.
Refer to Note 9 for additional income tax disclosures.
Revenue Recognition
Net Sales
The Company recognizes sales revenue, net of sales taxes and estimated sales returns, at the time it sells merchandise or
services to the customer. eCommerce sales include shipping revenue and are recorded upon delivery to the customer.
Estimated sales returns are calculated based on expected returns.
Membership Fee Revenue
The Company recognizes membership fee revenue both in the U.S. and internationally over the term of the membership, which
is typically 12 months. Membership fee revenue was $2.2 billion for fiscal 2022, $1.7 billion for fiscal 2021 and $1.5 billion
for fiscal 2020, respectively. Membership fee revenue is included in membership and other income in the Company's
Consolidated Statements of Income. Deferred membership fee revenue is included in accrued liabilities in the Company's
Consolidated Balance Sheets.
Gift Cards
Customer purchases of gift cards are not recognized as sales until the card is redeemed and the customer purchases merchandise
using the gift card. Gift cards in the U.S. and some countries do not carry an expiration date; therefore, customers and members
can redeem their gift cards for merchandise and services indefinitely. Gift cards in some countries where the Company does
business have expiration dates. While gift cards are generally redeemed within 12 months, a certain number of gift cards, both
with and without expiration dates, will not be fully redeemed. Management estimates unredeemed balances and recognizes
revenue for these amounts in membership and other income in the Company's Consolidated Statements of Income over the
expected redemption period.
Financial and Other Services
The Company recognizes revenue from service transactions at the time the service is performed. Generally, revenue from
services is classified as a component of net sales in the Company's Consolidated Statements of Income.
62

Cost of Sales
Cost of sales includes actual product cost, the cost of transportation to the Company's distribution facilities, stores and clubs
from suppliers, the cost of transportation from the Company's distribution facilities to the stores, clubs and customers and the
cost of warehousing for the Sam's Club segment and import distribution centers. Cost of sales is reduced by supplier payments
that are not a reimbursement of specific, incremental and identifiable costs.
Payments from Suppliers
The Company receives consideration from suppliers for various programs, primarily volume incentives, warehouse allowances
and reimbursements for specific programs such as markdowns, margin protection, advertising and supplier-specific fixtures.
Payments from suppliers are accounted for as a reduction of cost of sales, except in certain limited situations when the payment
is a reimbursement of specific, incremental and identifiable costs, and are recognized in the Company's Consolidated
Statements of Income when the related inventory is sold.
Operating, Selling, General and Administrative Expenses
Operating, selling, general and administrative expenses include all operating costs of the Company, except cost of sales, as
described above. As a result, the majority of the cost of warehousing and occupancy for the Walmart U.S. and Walmart
International segments' distribution facilities is included in operating, selling, general and administrative expenses. Because the
Company only includes a portion of the cost of its Walmart U.S. and Walmart International segments' distribution facilities in
cost of sales, its gross profit and gross profit as a percentage of net sales may not be comparable to those of other retailers that
may include all costs related to their distribution facilities in cost of sales and in the calculation of gross profit.
Advertising Costs
Advertising costs are expensed as incurred, consist primarily of digital, television and print advertisements and are recorded in
operating, selling, general and administrative expenses in the Company's Consolidated Statements of Income. Advertising costs
were $3.9 billion, $3.2 billion and $3.7 billion for fiscal 2022, 2021 and 2020, respectively.
Currency Translation
The assets and liabilities of all international subsidiaries are translated from the respective local currency to the U.S. dollar
using exchange rates at the balance sheet date. Related translation adjustments are recorded as a component of accumulated
other comprehensive loss. The Company's Consolidated Statements of Income of all international subsidiaries are translated
from the respective local currencies to the U.S. dollar using average exchange rates for the period covered by the income
statements.
Note 2. Net Income Per Common Share
Basic net income per common share attributable to Walmart is based on the weighted-average common shares outstanding
during the relevant period. Diluted net income per common share attributable to Walmart is based on the weighted-average
common shares outstanding during the relevant period adjusted for the dilutive effect of share-based awards. The Company did
not have significant share-based awards outstanding that were antidilutive and not included in the calculation of diluted net
income per common share attributable to Walmart for fiscal 2022, 2021 and 2020.
The following table provides a reconciliation of the numerators and denominators used to determine basic and diluted net
income per common share attributable to Walmart:
Fiscal Years Ended January 31,
(Amounts in millions, except per share data) 2022 2021 2020
Numerator
Consolidated net income
$ 13,940 $ 13,706 $ 15,201
Consolidated net income attributable to noncontrolling interest (267) (196) (320)
Consolidated net income attributable to Walmart
$ 13,673 $ 13,510 $ 14,881
Denominator
Weighted-average common shares outstanding, basic 2,792 2,831 2,850
Dilutive impact of stock options and other share-based awards
13 16 18
Weighted-average common shares outstanding, diluted 2,805 2,847 2,868
Net income per common share attributable to Walmart
Basic
$ 4.90 $ 4.77 $ 5.22
Diluted
4.87 4.75 5.19
63

Note 3. Shareholders' Equity
The total authorized shares of $0.10 par value common stock is 11.0 billion, of which 2.8 billion were issued and outstanding as
of January 31, 2022 and 2021.
Sale of Subsidiary Stock
During fiscal 2022, the Company received $3.2 billion primarily related to a new equity funding for the Company's majority-
owned Flipkart subsidiary, which reduced the Company's ownership from approximately 83% as of January 31, 2021 to
approximately 75%.
Share-Based Compensation
The Company has awarded share-based compensation to associates and nonemployee directors of the Company. The
compensation expense recognized for all stock incentive plans, including expense associated with plans of the Company's
consolidated subsidiaries granted in the subsidiaries' respective stock, was $1.2 billion, $1.2 billion and $0.9 billion for fiscal
2022, 2021 and 2020, respectively. Share-based compensation expense is generally included in operating, selling, general and
administrative expenses in the Company's Consolidated Statements of Income. The total income tax benefit recognized for
share-based compensation was $0.3 billion, $0.3 billion and $0.2 billion for fiscal 2022, 2021 and 2020, respectively. The
following table summarizes the Company's share-based compensation expense by award type for all plans:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Restricted stock units $ 659 $ 742 $ 553
Restricted stock and performance-based restricted stock units 321 277 270
Other 183 150 31
Share-based compensation expense
$ 1,163 $ 1,169 $ 854
The Walmart Inc. Stock Incentive Plan of 2015 (the "Plan"), as subsequently amended and restated, was established to grant
stock options, restricted (non-vested) stock, restricted stock units, performance share units and other equity compensation
awards for which 260 million shares of Walmart common stock issued or to be issued under the Plan have been registered
under the Securities Act of 1933. The Company believes that such awards serve to align the interests of its associates with
those of its shareholders.
The Plan's award types are summarized as follows:
• Restricted Stock Units. Restricted stock units provide rights to Company stock after a specified service period.
Beginning in fiscal 2020, restricted stock units generally vest at a rate of 25% each year over a four year period from the
date of the grant. Prior to fiscal 2020, 50% of restricted stock units generally vested three years from the grant date and
the remaining 50% were vested five years from the grant date. The fair value of each restricted stock unit is determined
on the date of grant using the stock price discounted for the expected dividend yield through the vesting period and is
recognized ratably over the vesting period. The expected dividend yield is based on the anticipated dividends over the
vesting period. The weighted-average discount for the dividend yield used to determine the fair value of restricted stock
units granted in fiscal 2022, 2021 and 2020 was 3.8%, 4.4% and 4.9%, respectively.
• Restricted Stock and Performance-based Restricted Stock Units. Restricted stock awards are for shares that vest based
on the passage of time and include restrictions related to employment. Performance-based restricted stock units vest
based on the passage of time and achievement of performance criteria and generally range from 0% to 150% of the
original award amount. Vesting periods for these awards are generally between one and three years. Restricted stock
and performance-based restricted stock units may be settled or deferred in stock and are accounted for as equity in the
Company's Consolidated Balance Sheets. The fair value of restricted stock awards is determined on the date of grant
and is expensed ratably over the vesting period. The fair value of performance-based restricted stock units is
determined on the date of grant using the Company's stock price discounted for the expected dividend yield through the
vesting period and is recognized over the vesting period. The weighted-average discount for the dividend yield used to
determine the fair value of performance-based restricted stock units in fiscal 2022, 2021 and 2020 was 4.2%, 4.5% and
5.1%, respectively.
In addition to the Plan, Flipkart has certain share-based compensation plans for associates under which options to acquire
Flipkart common shares may be issued. Share-based compensation expense associated with these plans is included in the Other
line in the table above.
64

The following table shows the activity for restricted stock units and restricted stock and performance-based restricted stock
units during fiscal 2022:
Restricted Stock Units
Restricted Stock and
Performance-based Restricted Stock
Units
(Shares in thousands) Shares
Weighted-Average
Grant-Date Fair
Value Per Share Shares
Weighted-Average
Grant-Date Fair
Value Per Share
Outstanding as of February 1, 2021 19,900 $ 92.13 5,413 $ 108.72
Granted 8,219 131.90 3,057 135.48
Adjustment for performance achievement
(1)
— — 920 107.67
Vested/exercised (8,051) 85.21 (2,614) 100.30
Forfeited (2,785) 110.65 (636) 110.95
Outstanding as of January 31, 2022
17,283 $ 111.42 6,140 $ 125.25
(1)
Represents the adjustment to previously granted performance share units for performance achievement.
The following table includes additional information related to restricted stock units and restricted stock and performance-based
restricted stock units:
Fiscal Years Ended January 31,
(Amounts in millions, except years) 2022 2021 2020
Fair value of restricted stock units vested $ 703 $ 597 $ 442
Fair value of restricted stock and performance-based restricted stock units vested 264 275 365
Unrecognized compensation cost for restricted stock units 1,102 1,062 1,096
Unrecognized compensation cost for restricted stock and performance-based restricted stock units 417 344 326
Weighted average remaining period to expense for restricted stock units (years) 1.2 1.1 1.3
Weighted average remaining period to expense for restricted stock and performance-based restricted stock
units (years)
1.5 1.4 1.4
Share Repurchase Program
From time to time, the Company repurchases shares of its common stock under share repurchase programs authorized by the
Company's Board of Directors. All repurchases made prior to February 22, 2021 were made under the plan in effect at the
beginning of fiscal 2022. On February 18, 2021, the Board of Directors approved a new $20.0 billion share repurchase program
which has no expiration date or other restrictions limiting the period over which the Company can make repurchases, and
beginning February 22, 2021, replaced the previous share repurchase program. Any repurchased shares are constructively
retired and returned to an unissued status.
The Company regularly reviews share repurchase activity and considers several factors in determining when to execute share
repurchases, including, among other things, current cash needs, capacity for leverage, cost of borrowings, results of operations
and the market price of the Company's common stock. The following table provides, on a settlement date basis, the number of
shares repurchased, average price paid per share and total amount paid for share repurchases for fiscal 2022, 2021 and 2020:
Fiscal Years Ended January 31,
(Amounts in millions, except per share data) 2022 2021 2020
Total number of shares repurchased 69.7 19.4 53.9
Average price paid per share
$ 140.45 $ 135.20 $ 105.98
Total cash paid for share repurchases
$ 9,787 $ 2,625 $ 5,717
Note 4. Accumulated Other Comprehensive Loss
The following table provides the changes in the composition of total accumulated other comprehensive loss for fiscal 2022,
2021 and 2020:
65

(Amounts in millions and net of immaterial income
taxes)
Currency
Translation
and Other
Net Investment
Hedges
Cash Flow
Hedges
Minimum
Pension Liability Total
Balances as of February 1, 2019
$ (12,085) $ 1,395 $ (140) $ (712) $ (11,542)
Other comprehensive income (loss) before
reclassifications, net
(1)
281 122 (399) (1,283) (1,279)
Reclassifications to income, net
(23) — — 39 16
Balances as of January 31, 2020
(11,827) 1,517 (539) (1,956) (12,805)
Other comprehensive income (loss) before
reclassifications, net
214 (221) 186 (172) 7
Reclassifications to income, net
(2)
841 — 49 142 1,032
Balances as of January 31, 2021
(10,772) 1,296 (304) (1,986) (11,766)
Other comprehensive loss before reclassifications,
net
(586) (7) (540) — (1,133)
Reclassifications related to business dispositions,
net
(3)
3,258 (1,195) 30 1,966 4,059
Reclassifications to income, net
— — 66 8 74
Balances as of January 31, 2022
$ (8,100) $ 94 $ (748) $ (12) $ (8,766)
(1)
Primarily includes the remeasurement of Asda Group Limited's ("Asda") pension benefit obligation subsequent to the cash contribution made by Asda in
fiscal 2020. Refer to Note 11.
(2)
Includes a cumulative foreign currency translation loss of $0.8 billion, for which there was no related income taxes, upon sale of the majority stake in
Walmart Argentina. Refer to Note 12.
(3)
Upon closing of the sale of the Company's operations in the U.K. and Japan during the first quarter of fiscal 2022, these amounts were released from
accumulated other comprehensive loss, the majority of which was considered in the impairment evaluation when the individual disposal groups met the held
for sale classification in fiscal 2021.
Amounts reclassified from accumulated other comprehensive loss for derivatives are recorded in interest, net, in the Company's
Consolidated Statements of Income, and the amounts for the minimum pension liability, as well as the cumulative translation
resulting from the disposition of a business, are recorded in other gains and losses in the Company's Consolidated Statements of
Income.
Note 5. Accrued Liabilities
The Company's accrued liabilities consist of the following as of January 31, 2022 and 2021:
January 31,
(Amounts in millions) 2022 2021
Accrued wages and benefits
(1)
7,908 7,654
Self-insurance
(2)
4,652 4,698
Accrued non-income taxes
(3)
3,247 3,328
Deferred gift card revenue
2,559 2,310
Liabilities held for sale
(4)
21 12,734
Other
(5)
7,673 7,242
Total accrued liabilities
$ 26,060 $ 37,966
(1)
Accrued wages and benefits include accrued wages, salaries, vacation, bonuses and other incentive plans.
(2)
Self-insurance consists of insurance-related liabilities, such as workers' compensation, general liability, auto liability, product liability and certain
employee-related healthcare benefits.
(3)
Accrued non-income taxes include accrued payroll, property, value-added, sales and miscellaneous other taxes.
(4)
Liabilities held for sale as of January 31, 2021 relate to the Company's operations in Japan and the U.K. classified as held for sale. See Note 12.
(5)
Other accrued liabilities includes items such as deferred membership revenue, interest, advertising, maintenance & utilities, and supply chain.
66

Note 6. Short-term Borrowings and Long-term Debt
Short-term borrowings consist of commercial paper and lines of credit. Short-term borrowings as of January 31, 2022 and 2021
were $0.4 billion and $0.2 billion, respectively, with weighted-average interest rates of 2.9% and 1.9%, respectively.
The Company has various committed lines of credit in the U.S. to support its commercial paper program and are summarized in
the following table:
January 31, 2022 January 31, 2021
(Amounts in millions) Available Drawn Undrawn Available Drawn Undrawn
Five-year credit facility
(1)
$ 5,000 $ — $ 5,000 $ 5,000 $ — $ 5,000
364-day revolving credit facility
(1)
10,000 — 10,000 10,000 — 10,000
Total
$ 15,000 $ — $ 15,000 $ 15,000 $ — $ 15,000
(1)
In April 2021, the Company renewed and extended its existing 364-day revolving credit facility as well as its five year credit facility.
The committed lines of credit in the table above mature in April 2022 and April 2026, carry interest rates of LIBOR plus 50
basis points, and incur commitment fees ranging between 1.5 and 4.0 basis points. In conjunction with the committed lines of
credit listed in the table above, the Company has agreed to observe certain covenants, the most restrictive of which relates to the
maximum amount of secured debt. Additionally, the Company has syndicated and fronted letters of credit available which
totaled $1.8 billion as of January 31, 2022 and 2021, of which $1.7 billion and $1.8 billion was drawn as of January 31, 2022
and 2021, respectively.
The Company's long-term debt, which includes the fair value instruments further discussed in Note 8, consists of the following
as of January 31, 2022 and 2021:
January 31, 2022 January 31, 2021
(Amounts in millions)
Maturity Dates
By Fiscal Year Amount
Average
Rate
(1)
Amount
Average
Rate
(1)
Unsecured debt
Fixed 2023 - 2052 $ 29,957 3.5% $ 35,216 3.9%
Variable — 750 0.5%
Total U.S. dollar denominated
29,957 35,966
Fixed 2023 - 2030 2,787 3.3% 3,034 3.3%
Variable — —
Total Euro denominated
2,787 3,034
Fixed 2031 - 2039 3,601 5.4% 3,682 5.4%
Variable — —
Total Sterling denominated
3,601 3,682
Fixed 2023 - 2028 1,475 0.3% 1,624 0.3%
Variable — —
Total Yen denominated
1,475 1,624
Total unsecured debt
37,820 44,306
Total other
(2)
(153) 3
Total debt
37,667 44,309
Less amounts due within one year (2,803) (3,115)
Long-term debt
$ 34,864 $ 41,194
(1)
The average rate represents the weighted-average stated rate for each corresponding debt category, based on year-end balances and year-end interest rates.
(2)
Includes deferred loan costs, discounts, fair value hedges, foreign-held debt and secured debt.
Annual maturities of long-term debt during the next five years and thereafter are as follows:
(Amounts in millions) Annual
Fiscal Year Maturities
2023 $ 2,803
2024 4,224
2025 3,565
2026 857
2027 2,757
Thereafter 23,461
Total
$ 37,667
67

Debt Issuances
Information on significant long-term debt issued during fiscal 2022, for general corporate purposes and certain eligible green
investment initiatives, is as follows:
(Amounts in millions)
Issue Date Principal Amount Maturity Date Fixed vs. Floating Interest Rate Net Proceeds
September 17, 2021 $1,250 September 17, 2026 Fixed 1.050% $ 1,243
September 22, 2021 $1,250 September 22, 2028 Fixed 1.500% 1,244
September 22, 2021
(1)
$2,000 September 22, 2031 Fixed 1.800% 1,981
September 22, 2021 $1,000 September 22, 2041 Fixed 2.500% 994
September 22, 2021 $1,500 September 22, 2051 Fixed 2.650% 1,483
Total $ 6,945
(1)
Represents a green bond issuance for which an amount equal to the net proceeds is intended to fund certain eligible green investment initiatives through the
maturity date of the bond.
These issuances are senior, unsecured notes which rank equally with all other senior, unsecured debt obligations of the
Company, and are not convertible or exchangeable. These issuances do not contain any financial covenants which restrict the
Company's ability to pay dividends or repurchase company stock. There were no long-term debt issuances in fiscal 2021.
Maturities and Extinguishments
The following table provides details of debt repayments during fiscal 2022:
(Amounts in millions)
Maturity Date Principal Amount Fixed vs. Floating Interest Rate Repayment
April 15, 2021 $510 Fixed 4.250% $ 510
June 23, 2021 $750 Floating Floating 750
June 23, 2021 $1,750 Fixed 3.125% 1,750
Total repayment of matured debt 3,010
June 26, 2023 $2,750 Fixed 3.400% 470
October 15, 2023 $152 Fixed 6.750% 2
July 8, 2024 $1,500 Fixed 2.850% 510
December 15, 2024 $1,000 Fixed 2.650% 370
June 26, 2025 $1,500 Fixed 3.550% 625
July 8, 2026 $1,250 Fixed 3.050% 451
April 5, 2027 $483 Fixed 5.875% 110
June 26, 2028 $2,750 Fixed 3.700% 1,271
July 8, 2029 $1,250 Fixed 3.250% 517
September 24, 2029 $500 Fixed 2.375% 181
February 15, 2030 $588 Fixed 7.550% 119
September 1, 2035 $1,968 Fixed 5.250% 635
August 15, 2037 $1,300 Fixed 6.500% 262
April 15, 2038 $919 Fixed 6.200% 116
June 28, 2038 $1,500 Fixed 3.950% 925
April 1, 2040 $751 Fixed 5.625% 142
July 8, 2040 $378 Fixed 4.875% 101
October 25, 2040 $519 Fixed 5.000% 125
April 15, 2041 $918 Fixed 5.625% 305
April 11, 2043 $709 Fixed 4.000% 296
October 2, 2043 $269 Fixed 4.750% 38
April 22, 2044 $502 Fixed 4.300% 172
December 15, 2047 $1,000 Fixed 3.625% 566
June 29, 2048 $3,000 Fixed 4.050% 1,317
September 24, 2049 $1,000 Fixed 2.950% 371
Total repayment of extinguished debt
(1)
10,000
Total $ 13,010
(1)
Represents portion of the outstanding principal amount which was repaid during fiscal 2022.
Individual repayment amounts may not sum due to rounding.
68

The Company recorded a $2.4 billion loss on extinguishment of debt during fiscal 2022, which included payment of $2.3 billion
in early extinguishment premiums.
The following table provides details of debt repayments during fiscal 2021:
(Amounts in millions)
Maturity Date Principal Amount Fixed vs. Floating Interest Rate Repayment
June 23, 2020 $750 Floating Floating $ 750
June 23, 2020 $1,250 Fixed 2.850% 1,250
July 8, 2020 $840 Fixed 3.630% 840
July 28, 2020 ¥10,000 Fixed 1.600% 95
October 25, 2020 $1,197 Fixed 3.250% 1,197
December 15, 2020 $1,250 Fixed 1.900% 1,250
Total repayment of matured debt $ 5,382
Note 7. Leases
The Company leases certain retail locations, distribution and fulfillment centers, warehouses, office spaces, land and equipment
throughout the U.S. and internationally. The Company's lease costs recognized in the Consolidated Statement of Income consist
of the following:
Fiscal years ended January 31,
(Amounts in millions) 2022 2021 2020
Operating lease cost $ 2,274
$ 2,626 $ 2,670
Finance lease cost:
Amortization of right-of-use assets 565
583 480
Interest on lease obligations 232
298 306
Variable lease cost 823
777 691
Other lease information is as follows:
Fiscal years ended January 31,
(Amounts in millions) 2022 2021 2020
Cash paid for amounts included in measurement of lease obligations:
Operating cash flows from operating leases $ 2,234 2,629 2,614
Operating cash flows from finance leases 225 286 278
Financing cash flows from finance leases 538 546 485
Assets obtained in exchange for operating lease obligations 1,816 2,131 2,151
Assets obtained in exchange for finance lease obligations 1,044 1,547 1,081
As of January 31,
2022 2021
Weighted-average remaining lease term - operating leases
12.2 years 12.5 years
Weighted-average remaining lease term - finance leases
13.4 years 13.7 years
Weighted-average discount rate - operating leases
5.9 % 6.1 %
Weighted-average discount rate - finance leases
6.5 % 6.8 %
The aggregate annual lease obligations at January 31, 2022, are as follows:
(Amounts in millions)
Fiscal Year Operating Leases Finance Leases
2023 $ 2,164 $ 736
2024 2,040 675
2025 1,876 611
2026 1,713 555
2027 1,551 482
Thereafter 11,322 4,987
Total undiscounted lease obligations 20,666 8,046
Less imputed interest (6,174) (3,292)
Net lease obligations $ 14,492 $ 4,754
69
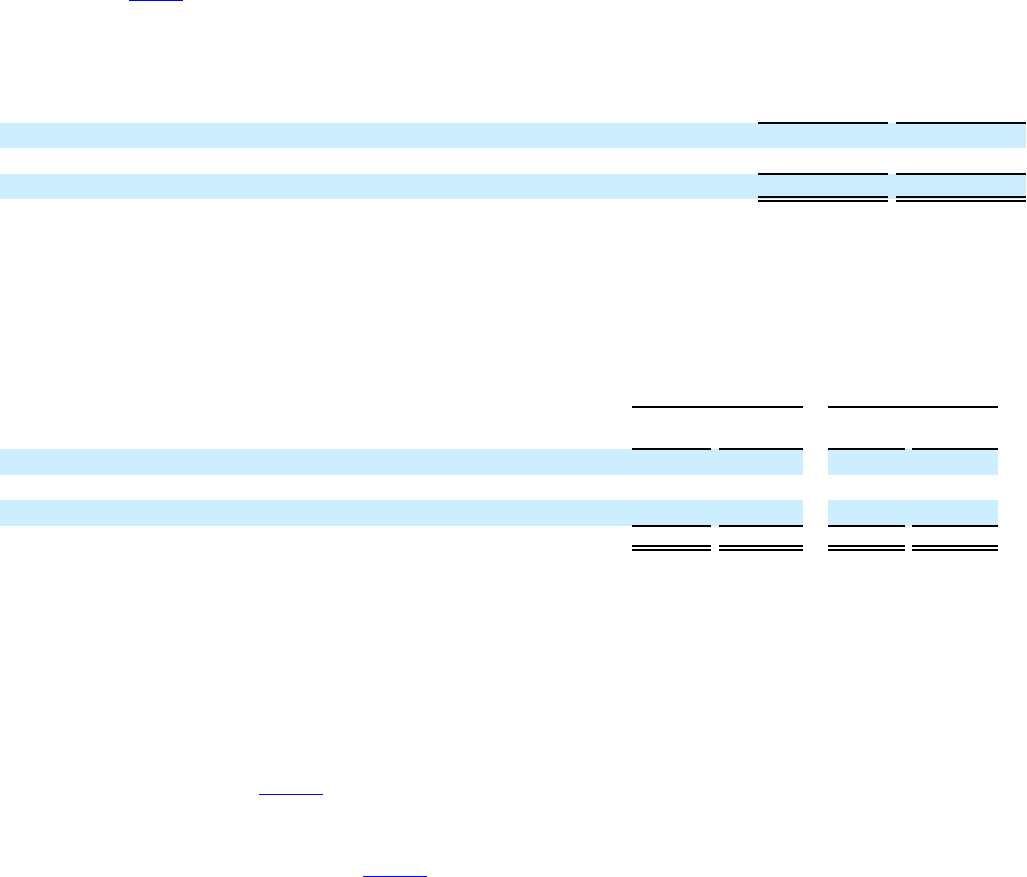
Note 8. Fair Value Measurements
Assets and liabilities recorded at fair value are measured using the fair value hierarchy, which prioritizes the inputs used in
measuring fair value. The levels of the fair value hierarchy are:
• Level 1: observable inputs such as quoted prices in active markets;
• Level 2: inputs other than quoted prices in active markets that are either directly or indirectly observable; and
• Level 3: unobservable inputs for which little or no market data exists, therefore requiring the Company to develop
its own assumptions.
As described in Note 1, the Company measures the fair value of certain equity investments on a recurring basis in the
accompanying Consolidated Balance Sheets. The fair values of the Company's equity investments measured on a recurring
basis are as follows:
(Amounts in millions)
Fair Value as of
January 31, 2022
Fair Value as of
January 31, 2021
Equity investments measured using Level 1 inputs $ 6,069 $ 6,517
Equity investments measured using Level 2 inputs 5,819 7,905
Total
$ 11,888 $ 14,422
Derivatives
The Company also has derivatives recorded at fair value. Derivative fair values are the estimated amounts the Company would
receive or pay upon termination of the related derivative agreements as of the reporting dates. The fair values have been
measured using the income approach and Level 2 inputs, which include the relevant interest rate and foreign currency forward
curves. As of January 31, 2022 and January 31, 2021, the notional amounts and fair values of these derivatives were as follows:
January 31, 2022 January 31, 2021
(Amounts in millions)
Notional
Amount Fair Value
Notional
Amount Fair Value
Receive fixed-rate, pay variable-rate interest rate swaps designated as fair value hedges $ 8,021 $ (47)
(1)
$ 3,250 $ 166
(2)
Receive fixed-rate, pay fixed-rate cross-currency swaps designated as net investment hedges — — 1,250 311
(2)
Receive fixed-rate, pay fixed-rate cross-currency swaps designated as cash flow hedges 7,855 (1,048)
(1)
5,073 (394)
(1)
Total
$ 15,876 $ (1,095) $ 9,573 $ 83
(1)
Primarily classified in deferred income taxes and other in the Company's Consolidated Balance Sheets.
(2)
Primarily classified in other long-term assets in the Company's Consolidated Balance Sheets.
Nonrecurring Fair Value Measurements
In addition to assets and liabilities that are recorded at fair value on a recurring basis, the Company's assets and liabilities are
also subject to nonrecurring fair value measurements. Generally, assets are recorded at fair value on a nonrecurring basis as a
result of impairment charges.
Upon completing the sales of Asda in February 2021 and Seiyu in March 2021, the Company recorded incremental non-
recurring impairment charges of $0.4 billion in the first quarter of fiscal 2022 within other gains and losses in the Consolidated
Statements of Income. Refer to Note 12. The Company did not have other material assets or liabilities resulting in
nonrecurring fair value measurements as of January 31, 2022.
For the fiscal year ended January 31, 2021, the Company's operations in Argentina, Japan and the U.K. met the held for sale
criteria in fiscal 2021, as further discussed in Note 12. As a result, the individual disposal groups were measured at fair value,
less costs to sell, which is considered a Level 3 fair value measurement based on each transaction's expected consideration. The
carrying value of the Argentina, Japan and U.K. disposal groups exceeded their fair value, less costs to sell, and as a result, the
Company recognized non-recurring impairment charges. The aggregate pre-tax loss of $8.3 billion associated with the
divestiture of these operations in the Walmart International segment was recorded in other gains and losses in the Consolidated
Statements of Income for the year ended January 31, 2021 and included these impairment charges as well as a $2.3 billion
charge related to the Asda pension plan. These impairment charges included the anticipated release of non-cash cumulative
foreign currency translation losses associated with the disposal groups. Other impairment charges for assets measured at fair
value on a nonrecurring basis during fiscal 2021 were immaterial.
70

For the fiscal year ended January 31, 2020, the Company recorded impairment charges related to assets measured at fair value
on a non-recurring basis primarily related to the following:
• in the Walmart U.S. segment, $0.5 billion in impairment charges for impaired assets consisting primarily of trade
names and acquired developed software due to strategic decisions that resulted in the write-down of certain
eCommerce assets; and
• in the Walmart International segment, $0.4 billion in impairment charges consisting primarily of the write-off of the
carrying value of one of Flipkart's two fashion trade names, Jabong.com, as a result of a strategic decision to focus on
the Myntra.com fashion platform.
These impairment charges were classified in operating, selling, general and administrative expenses in the Company's
Consolidated Statements of Income. Other impairment charges for assets measured at fair value on a nonrecurring basis during
fiscal 2020 were immaterial.
Other Fair Value Disclosures
The Company records cash and cash equivalents, restricted cash and short-term borrowings at cost. The carrying values of
these instruments approximate their fair value due to their short-term maturities.
The Company's long-term debt is also recorded at cost. The fair value is estimated using Level 2 inputs based on the
Company's current incremental borrowing rate for similar types of borrowing arrangements. The carrying value and fair value
of the Company's long-term debt as of January 31, 2022 and 2021, are as follows:
January 31, 2022 January 31, 2021
(Amounts in millions)
Carrying Value
Fair Value Carrying Value Fair Value
Long-term debt, including amounts due within one year $ 37,667 $ 42,381 $ 44,309 $ 54,240
Note 9. Taxes
The components of income before income taxes are as follows:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
U.S. $ 15,536 $ 18,068 $ 15,019
Non-U.S. 3,160 2,496 5,097
Total income before income taxes
$ 18,696 $ 20,564 $ 20,116
A summary of the provision for income taxes is as follows:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Current:
U.S. federal $ 3,313 $ 2,991 $ 2,794
U.S. state and local 649 742 587
International 1,553 1,127 1,205
Total current tax provision
5,515 4,860 4,586
Deferred:
U.S. federal (671) 2,316 663
U.S. state and local 41 23 35
International (129) (341) (369)
Total deferred tax expense (benefit)
(759) 1,998 329
Total provision for income taxes
$ 4,756 $ 6,858 $ 4,915
71

Effective Income Tax Rate Reconciliation
A reconciliation of the significant differences between the U.S. statutory tax rate and the effective income tax rate on pre-tax
income from continuing operations is as follows:
Fiscal Years Ended January 31,
2022 2021 2020
U.S. statutory tax rate 21.0 % 21.0 % 21.0 %
U.S. state income taxes, net of federal income tax benefit 2.8 % 2.9 % 2.2 %
Income taxed outside the U.S. (1.5) % (0.1) % (1.0) %
Disposal and wind-down of certain business operations 0.5 % 7.1 % — %
Valuation allowance 4.4 % 2.3 % 2.3 %
Net impact of repatriated international earnings (0.3) % (0.4) % 0.4 %
Federal tax credits (1.1) % (0.9) % (0.8) %
Enacted change in tax laws — % — % (1.9) %
Change in reserve for tax contingencies 0.2 % 0.8 % 2.5 %
Other, net (0.6) % 0.6 % (0.3) %
Effective income tax rate
25.4 % 33.3 % 24.4 %
The following sections regarding deferred taxes, unremitted earnings, net operating losses, tax credit carryforwards, valuation
allowances and uncertain tax positions exclude amounts related to operations classified as held for sale.
Deferred Taxes
The significant components of the Company's deferred tax account balances are as follows:
January 31,
(Amounts in millions) 2022 2021
Deferred tax assets:
Loss and tax credit carryforwards $ 9,456 $ 9,179
Accrued liabilities 2,752 2,582
Share-based compensation 231 224
Lease obligations 4,320 4,450
Other 893 589
Total deferred tax assets
17,652 17,024
Valuation allowances (9,542) (8,782)
Deferred tax assets, net of valuation allowances
8,110 8,242
Deferred tax liabilities:
Property and equipment 4,414 4,802
Acquired intangibles 1,065 1,071
Inventory 1,588 1,235
Lease right of use assets 4,355 4,390
Mark-to-market investments 1,825 2,678
Other 307 675
Total deferred tax liabilities
13,554 14,851
Net deferred tax liabilities
$ 5,444 $ 6,609
The deferred taxes noted above are classified as follows in the Company's Consolidated Balance Sheets:
January 31,
(Amounts in millions) 2022 2021
Balance Sheet classification
Assets:
Other long-term assets
$ 1,473 $ 1,836
Liabilities:
Deferred income taxes and other 6,917 8,445
Net deferred tax liabilities
$ 5,444 $ 6,609
72

Unremitted Earnings
Prior to the Tax Cuts and Jobs Act of 2017 (the "Tax Act"), the Company asserted that all unremitted earnings of its foreign
subsidiaries were considered indefinitely reinvested. As a result of the Tax Act, the Company reported and paid U.S. tax on the
majority of its previously unremitted foreign earnings, and repatriations of foreign earnings will generally be free of U.S.
federal tax, but may incur other taxes such as withholding or state taxes. As of January 31, 2022, the Company has not
recorded approximately $3 billion of deferred tax liabilities associated with remaining unremitted foreign earnings considered
indefinitely reinvested, for which U.S. and foreign income and withholding taxes would be due upon repatriation.
Net Operating Losses, Tax Credit Carryforwards and Valuation Allowances
As of January 31, 2022, the Company's net operating loss and capital loss carryforwards totaled approximately $39.3 billion.
Of these carryforwards, approximately $26.6 billion will expire, if not utilized, in various years through 2042. The remaining
carryforwards have no expiration.
The recoverability of these future tax deductions and credits is evaluated by assessing the adequacy of future expected taxable
income from all sources, including taxable income in prior carryback years, reversal of taxable temporary differences,
forecasted operating earnings and available tax planning strategies. To the extent the Company does not consider it more likely
than not that a deferred tax asset will be recovered, a valuation allowance is generally established. To the extent that a
valuation allowance was established and it is subsequently determined that it is more likely than not that the deferred tax assets
will be recovered, the change in the valuation allowance is recognized in the Consolidated Statements of Income.
The Company had valuation allowances of $9.5 billion and $8.8 billion as of January 31, 2022 and 2021, respectively, on
deferred tax assets associated primarily with the net operating loss carryforwards. Activity in the valuation allowance during
fiscal 2022 related to valuation allowance builds in multiple markets, as well as releases due to the expiration of underlying
deferred tax assets.
Uncertain Tax Positions
The benefits of uncertain tax positions are recorded in the Company's Consolidated Financial Statements only after determining
a more-likely-than-not probability that the uncertain tax positions will withstand challenge, if any, from taxing authorities.
As of January 31, 2022 and 2021, the amount of gross unrecognized tax benefits related to continuing operations was $3.2
billion and $3.1 billion, respectively. The amount of unrecognized tax benefits that would affect the Company's effective
income tax rate was $1.8 billion and $1.7 billion as of January 31, 2022 and 2021, respectively.
A reconciliation of gross unrecognized tax benefits from continuing operations is as follows:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Gross unrecognized tax benefits, beginning of year
$ 3,135 $ 1,817 $ 1,305
Increases related to prior year tax positions 170 92 516
Decreases related to prior year tax positions (97) (264) (15)
Increases related to current year tax positions 75 1,582 66
Settlements during the period (5) (64) (29)
Lapse in statutes of limitations (33) (28) (26)
Gross unrecognized tax benefits, end of year
$ 3,245 $ 3,135 $ 1,817
The Company classifies interest and penalties related to uncertain tax benefits as interest expense and as operating, selling,
general and administrative expenses, respectively. Interest expense and penalties related to these positions were immaterial for
fiscal 2022, 2021 and 2020. During the next twelve months, it is reasonably possible that tax audit resolutions could reduce
unrecognized tax benefits by an immaterial amount, either because the tax positions are sustained on audit or because the
Company agrees to their disallowance. The Company is focused on resolving tax audits as expeditiously as possible. As a
result of these efforts, unrecognized tax benefits could potentially be reduced beyond the provided range during the next twelve
months. The Company does not expect any change to have a material impact to its Consolidated Financial Statements.
The Company remains subject to income tax examinations for its U.S. federal income taxes generally for fiscal 2014, and 2018
through 2022. The Company also remains subject to income tax examinations for international income taxes for fiscal 2013
through 2022, and for U.S. state and local income taxes generally for the fiscal years ended 2013 through 2022. With few
exceptions, the Company is no longer subject to U.S. federal, state, local, or foreign examinations by tax authorities for years
before fiscal 2013.
73
Other Taxes
The Company is subject to tax examinations for value added, sales-based, payroll and other non-income taxes. A number of
these examinations are ongoing in various jurisdictions. In certain cases, the Company has received assessments and judgments
from the respective taxing authorities in connection with these examinations. Unless otherwise indicated, the possible losses or
range of possible losses associated with these matters are individually immaterial, but a group of related matters, if decided
adversely to the Company, could result in a liability material to the Company's Consolidated Financial Statements.
Note 10. Contingencies
Legal Proceedings
The Company is involved in a number of legal proceedings and certain regulatory matters. The Company has made accruals
with respect to these matters, where appropriate, which are reflected in the Company's Consolidated Financial Statements. For
some matters, a liability is not probable or the amount cannot be reasonably estimated and therefore an accrual has not been
made. However, where a liability is reasonably possible and may be material, such matters have been disclosed. The Company
may enter into discussions regarding settlement of these matters, and may enter into settlement agreements, if it believes
settlement is in the best interest of the Company and its shareholders.
Unless stated otherwise, the matters discussed below, if decided adversely to or settled by the Company, individually or in the
aggregate, may result in a liability material to the Company's financial position, results of operations or cash flows.
Opioids Litigation
In December 2017, the United States Judicial Panel on Multidistrict Litigation consolidated numerous lawsuits filed against a
wide array of defendants by various plaintiffs, including counties, cities, healthcare providers, Native American tribes,
individuals, and third-party payers, asserting claims generally concerning the impacts of widespread opioid abuse. The
consolidated multidistrict litigation is entitled In re National Prescription Opiate Litigation (MDL No. 2804) (the "MDL") and
is pending in the U.S. District Court for the Northern District of Ohio. The Company is named as a defendant in some of the
cases included in this multidistrict litigation. The liability phase of a trial in one of the MDL cases began on October 4, 2021
against a number of parties, including the Company, regarding opioid dispensing claims. On November 23, 2021, the jury
found in favor of the plaintiffs as to the liability of all defendants, including the Company. The abatement phase of the trial,
which will determine amounts owed by the defendants, is currently scheduled to begin on May 10, 2022. The Company intends
to appeal the jury verdict from the liability phase upon completion of the abatement phase of the trial.
Similar cases that name the Company have also been filed in state courts by state, local and tribal governments, health care
providers and other plaintiffs. Plaintiffs are seeking compensatory and punitive damages, as well as injunctive relief including
abatement. The Company cannot predict the number of such claims that may be filed, but believes it has substantial factual and
legal defenses to these claims, and intends to defend the claims vigorously. The Company has also been responding to
subpoenas, information requests and investigations from governmental entities related to nationwide controlled substance
dispensing and distribution practices involving opioids.
On October 22, 2020, the Company filed a declaratory judgment action in the U.S. District Court for the Eastern District of
Texas against the U.S. Department of Justice (the "DOJ") and the U.S. Drug Enforcement Administration, asking a federal
court to clarify the roles and responsibilities of pharmacists and pharmacies as to the dispensing and distribution of opioids
under the Controlled Substances Act (the "CSA"). The Company's action was dismissed. The Company had appealed this
decision to the Fifth Circuit. On December 22, 2021, the Fifth Circuit affirmed the dismissal of the action.
On December 22, 2020, the DOJ filed a civil complaint in the U.S. District Court for the District of Delaware alleging that the
Company unlawfully dispensed controlled substances from its pharmacies and unlawfully distributed controlled substances to
those pharmacies. The complaint alleges that this conduct resulted in violations of the CSA. The DOJ is seeking civil penalties
and injunctive relief. The Company filed a motion to dismiss the DOJ complaint on February 22, 2021. The DOJ filed its
opposition brief on April 23, 2021 and the Company filed its reply brief on May 24, 2021. On November 19, 2021, the District
Court stayed further proceedings in the DOJ complaint pending the decision of the United States Supreme Court in two
consolidated cases (not involving Walmart) interpreting the CSA.
In addition, the Company is the subject of two securities class actions alleging violations of the federal securities laws regarding
the Company's disclosures with respect to opioids, filed in the U.S. District Court for the District of Delaware on January 20,
2021 and March 5, 2021 purportedly on behalf of a class of investors who acquired Walmart stock from March 30, 2016
through December 22, 2020. Those cases have been consolidated. On October 8, 2021, the defendants filed a motion to dismiss
the consolidated securities action; the lead plaintiff responded to the motion on January 10, 2022; and the defendants filed their
reply brief on February 10, 2022. Derivative actions were also filed by two of the Company's shareholders in the U.S. District
Court for the District of Delaware on February 9, 2021 and April 16, 2021 alleging breach of fiduciary duties against certain of
its current and former directors with respect to oversight of the Company's distribution and dispensing of opioids and also
alleging violations of the federal securities laws and other breaches of duty by current directors and two current officers in
connection with the Company's opioids disclosures. Those cases have been stayed pending developments in other Opioids
74

Litigation matters. On September 27, 2021, three shareholders filed a derivative action in the Delaware Court of Chancery
alleging that certain members of the current Board and certain former officers breached their fiduciary duties in failing to
adequately oversee the Company's prescription opioids business. The defendants filed the opening brief on their motion to
dismiss that case on December 21, 2021, and the plaintiffs responded by filing an amended complaint on February 22, 2022.
The Company cannot reasonably estimate any loss or range of loss that may arise from the various Opioids Litigation and
intends to vigorously defend these litigation matters. Accordingly, the Company can provide no assurance as to the scope and
outcome of these matters and no assurance as to whether its business, financial position, results of operations or cash flows will
not be materially adversely affected.
Asda Equal Value Claims
Asda, formerly a subsidiary of the Company, was and still is a defendant in certain equal value claims that began in 2008 and
are proceeding before an Employment Tribunal in Manchester in the United Kingdom on behalf of current and former Asda
store employees (the "Asda Equal Value Claims"), and further claims may be asserted in the future. Subsequent to the
divestiture of Asda in February 2021, the Company will continue to oversee the conduct of the defense of these claims. While
potential liability for these claims remains with Asda, the Company has agreed to provide indemnification with respect to these
claims up to a contractually determined amount. The Company cannot predict the number of such claims that may be filed, and
cannot reasonably estimate any loss or range of loss that may arise related to these proceedings. Accordingly, the Company can
provide no assurance as to the scope and outcomes of these matters.
Note 11. Retirement-Related Benefits
The Company offers a 401(k) plan for associates in the U.S. under which eligible associates can begin contributing to the plan
immediately upon hire. The Company also offers a 401(k) type plan for associates in Puerto Rico under which associates can
begin to contribute generally after one year of employment. Under these plans, after one year of employment, the Company
matches 100% of participant contributions up to 6% of annual eligible earnings. The matching contributions immediately vest
at 100% for each associate. Participants can contribute up to 50% of their pre-tax earnings, but not more than the statutory
limits.
Associates in international countries who are not U.S. citizens are covered by various defined contribution post-employment
benefit arrangements. These plans are administered based upon the legislative and tax requirements in the countries in which
they are established.
The following table summarizes the contribution expense related to the Company's defined contribution plans for fiscal 2022,
2021 and 2020:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Defined contribution plans:
U.S. $ 1,441 $ 1,290 $ 1,184
International 39 200 177
Total contribution expense for defined contribution plans
$ 1,480 $ 1,490 $ 1,361
Additionally, the Company's previously owned subsidiary in the United Kingdom sponsored a defined benefit pension plan. In
fiscal 2020, Asda, Walmart and the Trustee of the Asda Group Pension Scheme (the "Plan") entered into an agreement pursuant
to which Asda made a cash contribution of $1.0 billion to the Plan (the "Asda Pension Contribution") which enabled the Plan to
purchase a bulk annuity insurance contract for the benefit of Plan participants, and released the Plan and Asda from any future
obligations. In connection with the sale of Asda, all accumulated pension components of $2.3 billion were included in the
disposal group and the estimated pre-tax loss recognized during the fourth quarter of fiscal 2021 as discussed in Note 8 and
Note 12.
75

Note 12. Disposals, Acquisitions and Related Items
The following disposals impact the Company's Walmart International segment. Other immaterial transactions have also
occurred or been announced.
Asda
In February 2021, the Company completed the divestiture of Asda, the Company's retail operations in the U.K., for net
consideration of $9.6 billion. Upon closing of the transaction, the Company recorded an incremental pre-tax loss of $0.2 billion
in other gains and losses in its Consolidated Statement of Income in the first quarter of fiscal 2022, primarily related to changes
in the net assets of the disposal group, currency exchange rate fluctuations and customary purchase price adjustments upon
closing. During the first quarter of fiscal 2022, the Company deconsolidated the financial statements of Asda and recognized
its retained investment in Asda as a debt security within other long-term assets and also recognized certain legal and tax
indemnity liabilities within deferred income taxes and other on the Consolidated Balance Sheet.
Asda was classified as held for sale in the Consolidated Balance Sheet as of January 31, 2021, and as a result, the Company
recognized an estimated pre-tax loss of $5.5 billion in other gains and losses in its Consolidated Statement of Income in the
fourth quarter of fiscal 2021. Upon classifying the Asda disposal group as held for sale, $2.3 billion of accumulated pension
components associated with the expected derecognition of the Asda pension plan were included as part of the loss. In
calculating the loss, the fair value of the disposal group was reduced by approximately $0.8 billion related to the estimated fair
value of certain indemnities and other transaction related costs.
Seiyu
In March 2021, the Company completed the divestiture of Seiyu, the Company's retail operations in Japan, for net consideration
of $1.2 billion. Upon closing of the transaction, the Company recorded an incremental pre-tax loss of $0.2 billion in other gains
and losses in its Consolidated Statement of Income in the first quarter of fiscal 2022, primarily related to changes in the net
assets of the disposal group, currency exchange rate fluctuations and customary purchase price adjustments upon closing.
During the first quarter of fiscal 2022, the Company deconsolidated the financial statements of Seiyu and recognized its
retained 15 percent ownership interest in Seiyu as an equity investment within other long-term assets on the Consolidated
Balance Sheet.
Seiyu was classified as held for sale in the Consolidated Balance Sheet as of January 31, 2021, and as a result, the Company
recognized an estimated pre-tax loss of $1.9 billion in other gains and losses in its Consolidated Statement of Income in the
fourth quarter of fiscal 2021.
Assets and liabilities held for sale associated with the Asda and Seiyu disposal groups as of January 31, 2021 were as follows:
January 31,
(Amounts in millions) 2021
Cash and cash equivalents $ 1,848
Other current assets
(1)
2,545
Property and equipment, net 13,193
Operating lease right-of-use assets 4,360
Finance lease right-of-use assets, net 1,395
Goodwill 2,211
Other long-term assets 1,063
Valuation allowance against assets held for sale
(2)
(7,420)
Total assets held for sale
$ 19,195
Current liabilities
(3)
6,535
Operating lease obligations, including amounts due within one year 4,245
Finance lease obligations, including amounts due within one year 1,495
Deferred income taxes and other 459
Total liabilities held for sale
$ 12,734
(1)
Includes inventories, receivables, net and prepaid expenses and other.
(2)
Includes the $2.3 billion loss associated with the derecognition of the Asda pension plan and $1.3 billion cumulative foreign currency and related net
investment hedge and other impacts included within the disposal groups, which were reclassified from accumulated other comprehensive loss upon closure
of each transaction.
(3)
Includes accounts payable and accrued liabilities.
Walmart Argentina
In November 2020, the Company completed the sale of Walmart Argentina. As a result, the Company recorded a pre-tax loss of
$1.0 billion in the third quarter of fiscal 2021 in other gains and losses in its Consolidated Statement of Income primarily due to
the impact of cumulative translation losses on the carrying value of the disposal group.
76

Note 13. Segments and Disaggregated Revenue
Segments
The Company is engaged in the operation of retail and wholesale stores and clubs, as well as eCommerce websites, located
throughout the U.S., Africa, Canada, Central America, Chile, China, India and Mexico. The Company previously operated in
Argentina prior to the sale of Walmart Argentina in the fourth quarter of fiscal 2021 and operated in the United Kingdom and
Japan prior to the sale of those operations in the first quarter of fiscal 2022. Refer to Note 12 for discussion of recent
divestitures. The Company's operations are conducted in three reportable segments: Walmart U.S., Walmart International and
Sam's Club. The Company defines its segments as those operations whose results the chief operating decision maker
("CODM") regularly reviews to analyze performance and allocate resources. The Company sells similar individual products
and services in each of its segments. It is impracticable to segregate and identify revenues for each of these individual products
and services.
The Walmart U.S. segment includes the Company's mass merchant concept in the U.S., as well as eCommerce and omni-
channel initiatives. The Walmart International segment consists of the Company's operations outside of the U.S., as well as
eCommerce and omni-channel initiatives. The Sam's Club segment includes the warehouse membership clubs in the U.S., as
well as eCommerce and omni-channel initiatives. Corporate and support consists of corporate overhead and other items not
allocated to any of the Company's segments.
The Company measures the results of its segments using, among other measures, each segment's net sales and operating
income, which includes certain corporate overhead allocations. From time to time, the Company revises the measurement of
each segment's operating income, including any corporate overhead allocations, as determined by the information regularly
reviewed by its CODM. Information for the Company's segments, as well as for Corporate and support, including the
reconciliation to income before income taxes, is provided in the following table:
(Amounts in millions) Walmart U.S.
Walmart
International Sam's Club
Corporate
and support Consolidated
Fiscal Year Ended January 31, 2022
Net sales $ 393,247 $ 100,959 $ 73,556 $ — $ 567,762
Operating income (loss) 21,587 3,758 2,259 (1,662) 25,942
Interest, net (1,836)
Loss on extinguishment of debt (2,410)
Other gains and (losses) (3,000)
Income before income taxes $ 18,696
Total assets $ 125,044 $ 91,403 $ 14,678 $ 13,735 $ 244,860
Depreciation and amortization 6,773 1,963 601 1,321 10,658
Capital expenditures 8,475 2,497 622 1,512 13,106
Fiscal Year Ended January 31, 2021
Net sales $ 369,963 $ 121,360 $ 63,910 $ — $ 555,233
Operating income (loss) 19,116 3,660 1,906 (2,134) 22,548
Interest, net (2,194)
Other gains and (losses) 210
Income before income taxes $ 20,564
Total assets $ 113,490 $ 109,445 $ 13,415 $ 16,146 $ 252,496
Depreciation and amortization 6,561 2,633 599 1,359 11,152
Capital expenditures 6,131 2,436 488 1,209 10,264
Fiscal Year Ended January 31, 2020
Net sales $ 341,004 $ 120,130 $ 58,792 $ — $ 519,926
Operating income (loss) 17,380 3,370 1,642 (1,824) 20,568
Interest, net (2,410)
Other gains and (losses) 1,958
Income before income taxes $ 20,116
Total assets $ 110,353 $ 105,811 $ 13,494 $ 6,837 $ 236,495
Depreciation and amortization 6,408 2,682 605 1,292 10,987
Capital expenditures 6,315 2,801 525 1,064 10,705
77

Total revenues, consisting of net sales and membership and other income, and long-lived assets, consisting primarily of
property and equipment, net and lease right-of-use assets, aggregated by the Company's U.S. and non-U.S. operations for fiscal
2022, 2021 and 2020, are as follows:
Fiscal Years Ended January 31,
(Amounts in millions) 2022 2021 2020
Revenues
U.S. operations $ 470,295 $ 436,649 $ 402,532
Non-U.S. operations 102,459 122,502 121,432
Total revenues
$ 572,754 $ 559,151 $ 523,964
Long-lived assets
U.S. operations $ 89,795 $ 87,068 $ 86,944
Non-U.S. operations 22,829 22,780 40,105
Total long-lived assets
$ 112,624 $ 109,848 $ 127,049
No individual country outside of the U.S. had total revenues or long-lived assets that were material to the consolidated totals.
Long-lived assets related to operations classified as held for sale are excluded from the table above. Additionally, the Company
did not generate material revenues from any single customer.
Disaggregated Revenues
In the following tables, segment net sales are disaggregated by either merchandise category or market. In addition, net sales
related to eCommerce are provided for each segment, which include omni-channel sales where a customer initiates an order
digitally and the order is fulfilled through a store or club.
(Amounts in millions) Fiscal Years Ended January 31,
Walmart U.S. net sales by merchandise category 2022 2021 2020
Grocery
$ 218,944 $ 208,413 $ 192,428
General merchandise 125,876 119,406 108,687
Health and wellness 42,839 38,522 36,558
Other categories 5,588 3,622 3,331
Total $ 393,247 $ 369,963 $ 341,004
Of Walmart U.S.'s total net sales, approximately $47.8 billion, $43.0 billion and $24.1 billion related to eCommerce for fiscal
2022, 2021 and 2020, respectively.
(Amounts in millions) Fiscal Years Ended January 31,
Walmart International net sales by market 2022 2021 2020
Mexico and Central America
$ 35,964 $ 32,642 $ 33,350
Canada 21,773 19,991 18,420
China 13,852 11,430 10,671
United Kingdom
3,811 29,234 29,243
Other
25,559 28,063 28,446
Total $ 100,959 $ 121,360 $ 120,130
Of Walmart International's total net sales, approximately $18.5 billion, $16.6 billion and $11.8 billion related to eCommerce for
fiscal 2022, 2021 and 2020, respectively.
(Amounts in millions) Fiscal Years Ended January 31,
Sam's Club net sales by merchandise category 2022 2021 2020
Grocery and consumables
$ 46,822 $ 42,148 $ 35,043
Fuel, tobacco and other categories
11,048 7,838 10,571
Home and apparel
8,740 7,092 6,744
Health and wellness
3,956 3,792 3,372
Technology, office and entertainment 2,990 3,040 3,062
Total
$ 73,556 $ 63,910 $ 58,792
Of Sam's Club's total net sales, approximately $6.9 billion, $5.3 billion and $3.8 billion related to eCommerce for fiscal 2022,
2021 and 2020, respectively.
78

Note 14. Subsequent Event
Dividends Declared
The Board of Directors approved, effective February 17, 2022, the fiscal 2023 annual dividend of $2.24 per share, an increase
over the fiscal 2022 dividend of $2.20 per share. For fiscal 2023, the annual dividend will be paid in four quarterly installments
of $0.56 per share, according to the following record and payable dates:
Record Date Payable Date
March 18, 2022 April 4, 2022
May 6, 2022 May 31, 2022
August 12, 2022 September 6, 2022
December 9, 2022 January 3, 2023
79

ITEM 9. CHANGES IN AND DISAGREEMENTS WITH ACCOUNTANTS ON ACCOUNTING AND
FINANCIAL DISCLOSURE
None.
ITEM 9A. CONTROLS AND PROCEDURES
Evaluation of Disclosure Controls and Procedures
We maintain disclosure controls and procedures that are designed to provide reasonable assurance that information, which is
required to be timely disclosed, is accumulated and communicated to management in a timely fashion. In designing and
evaluating such controls and procedures, we recognize that any controls and procedures, no matter how well designed and
operated, can provide only reasonable assurance of achieving the desired control objectives. Our management is necessarily
required to use judgment in evaluating controls and procedures. Also, we have investments in unconsolidated entities. Since
we do not control or manage those entities, our controls and procedures with respect to those entities are substantially more
limited than those we maintain with respect to our consolidated subsidiaries.
In the ordinary course of business, we review our internal control over financial reporting and make changes to our systems and
processes to improve such controls and increase efficiency, while ensuring that we maintain an effective internal control
environment. Changes may include such activities as implementing new, more efficient systems, updating existing systems,
automating manual processes, standardizing controls globally, migrating certain processes to our shared services organizations
and increasing monitoring controls. These changes have not materially affected, and are not reasonably likely to materially
affect, the Company's internal control over financial reporting. However, they allow us to continue to enhance our internal
control over financial reporting and ensure that our internal control environment remains effective.
An evaluation of the effectiveness of the design and operation of our disclosure controls and procedures as of the end of the
period covered by this report was performed under the supervision and with the participation of management, including our
Chief Executive Officer and Chief Financial Officer. Based upon that evaluation, our Chief Executive Officer and Chief
Financial Officer concluded that our disclosure controls and procedures are effective to provide reasonable assurance that
information required to be disclosed by the Company in the reports that it files or submits under the Securities Exchange Act of
1934, as amended, is accumulated and communicated to management, including our Chief Executive Officer and Chief
Financial Officer, as appropriate, to allow timely decisions regarding required disclosure and are effective to provide reasonable
assurance that such information is recorded, processed, summarized and reported within the time periods specified by the SEC's
rules and forms.
Report on Internal Control Over Financial Reporting
Management has responsibility for establishing and maintaining adequate internal control over financial reporting. Internal
control over financial reporting is a process designed to provide reasonable assurance regarding the reliability of financial
reporting and the preparation of financial statements for external reporting purposes in accordance with accounting principles
generally accepted in the United States. Because of its inherent limitations, internal control over financial reporting may not
prevent or detect misstatements. Management has assessed the effectiveness of the Company's internal control over financial
reporting as of January 31, 2022. In making its assessment, management has utilized the criteria set forth by the Committee of
Sponsoring Organizations ("COSO") of the Treadway Commission in Internal Control-Integrated Framework (2013).
Management concluded that based on its assessment, Walmart's internal control over financial reporting was effective as of
January 31, 2022. The Company's internal control over financial reporting as of January 31, 2022, has been audited by Ernst &
Young LLP as stated in their report which appears herein.
Changes in Internal Control Over Financial Reporting
There has been no change in the Company's internal control over financial reporting as of January 31, 2022, that has materially
affected, or is reasonably likely to materially affect, the Company's internal control over financial reporting.
ITEM 9B. OTHER INFORMATION
None.
ITEM 9C. DISCLOSURE REGARDING FOREIGN JURISDICTIONS THAT PREVENT INSPECTIONS
Not applicable.
80

PART III
ITEM 10. DIRECTORS, EXECUTIVE OFFICERS AND CORPORATE GOVERNANCE
Please see the information concerning our executive officers contained in "Item 1. Business" herein under the caption
"Information About Our Executive Officers," which is included in accordance with the Instruction to Item 401 of the SEC's
Regulation S-K.
Information required by this Item 10 with respect to the Company's directors and certain family relationships is incorporated by
reference to such information under the caption "Proposal No. 1 – Election of Directors" included in our Proxy Statement
relating to our 2022 Annual Meeting of Shareholders (our "Proxy Statement").
No material changes have been made to the procedures by which shareholders of the Company may recommend nominees to
our Board of Directors since those procedures were disclosed in our proxy statement relating to our 2021 Annual Shareholders'
Meeting as previously filed with the SEC.
The information regarding our Audit Committee, including our audit committee financial experts, our Reporting Protocols for
Senior Financial Officers and our Code of Conduct applicable to all of our associates, including our Chief Executive Officer,
Chief Financial Officer and our Controller, who is our principal accounting officer, required by this Item 10 is incorporated
herein by reference to the information under the captions "Corporate Governance" and "Proposal No. 3: Ratification of
Independent Accountants" included in our Proxy Statement. "Item 1. Business" above contains information relating to the
availability of a copy of our Reporting Protocols for Senior Financial Officers and our Code of Conduct and the posting of
amendments to and any waivers of the Reporting Protocols for Senior Financial Officers and our Code of Conduct on our
website.
ITEM 11. EXECUTIVE COMPENSATION
The information required by this Item 11 is incorporated herein by reference to the information under the captions "Corporate
Governance – Director Compensation" and "Executive Compensation" included in our Proxy Statement.
ITEM 12. SECURITY OWNERSHIP OF CERTAIN BENEFICIAL OWNERS AND MANAGEMENT AND
RELATED STOCKHOLDER MATTERS
The information required by this Item 12 is incorporated herein by reference to the information that appears under the caption
"Stock Ownership" included in our Proxy Statement.
ITEM 13. CERTAIN RELATIONSHIPS AND RELATED TRANSACTIONS, AND DIRECTOR
INDEPENDENCE
The information required by this Item 13 is incorporated herein by reference to the information under the caption "Corporate
Governance – Board Processes and Practices" included in our Proxy Statement.
ITEM 14. PRINCIPAL ACCOUNTING FEES AND SERVICES
The information required by this Item 14 is incorporated herein by reference to the information under the caption "Proposal No.
3 – Ratification of Independent Accountants" included in our Proxy Statement.
81

PART IV
ITEM 15. EXHIBITS, FINANCIAL STATEMENT SCHEDULES
(a) Documents filed as part of this report are as follows:
1. Financial Statements: See the Financial Statements in "Item 8. Financial Statements and Supplementary Data."
2. Financial Statement Schedules:
Certain schedules have been omitted because the required information is not present or is not present in
amounts sufficient to require submission of the schedule, or because the information required is included in
the Consolidated Financial Statements, including the notes thereto.
3. Exhibits:
See exhibits listed under part (b) below.
(b) The required exhibits are filed as part of this Form 10-K or are incorporated by reference herein.
(1)
3.1 Restated Certificate of Incorporation of the Company dated February 1, 2018 is incorporated herein by
reference to Exhibit 3.1 to the Report on Form 8-K filed by the Company on February 1, 2018
3.2 Amended and Restated Bylaws of the Company dated July 23, 2019 are incorporated herein by reference to
Exhibit 3.1 to the Report on Form 8-K filed by the Company on July 26, 2019
4.1 Indenture dated as of April 1, 1991, between the Company and J.P. Morgan Trust Company, National
Association, as successor trustee to Bank One Trust Company, NA, as successor trustee to The First National
Bank of Chicago, Trustee, is incorporated herein by reference to Exhibit 4(a) to Registration Statement on
Form S-3 (File Number 33-51344)
(P)
4.2 First Supplemental Indenture dated as of September 9, 1992, to the Indenture dated as of April 1, 1991,
between the Company and J.P. Morgan Trust Company, National Association, as successor trustee to Bank
One Trust Company, NA, as successor trustee to The First National Bank of Chicago, Trustee, is incorporated
herein by reference to Exhibit 4(b) to Registration Statement on Form S-3 (File Number 33-51344)
(P)
4.3 Indenture dated as of December 11, 2002, between the Company and J.P. Morgan Trust Company, National
Association, as successor trustee to Bank One Trust Company, NA, is incorporated by reference to Exhibit 4.5
to Registration Statement on Form S-3 (File Number 333-101847)
4.4 Indenture dated as of July 19, 2005, between the Company and J.P. Morgan Trust Company, National
Association is incorporated by reference to Exhibit 4.5 to Registration Statement on Form S-3 (File Number
333-126512)
4.5 First Supplemental Indenture, dated December 1, 2006, between the Company and The Bank of New York
Trust Company, N.A., as successor-in-interest to J.P. Morgan Trust Company, National Association, as
Trustee, under the Indenture, dated as of July 19, 2005, between the Company and J.P. Morgan Trust
Company, National Association, as Trustee, is incorporated herein by reference to Exhibit 4.6 to Post-
Effective Amendment No. 1 to Registration Statement on Form S-3 (File Number 333-130569)
4.6 Second Supplemental Indenture, dated December 19, 2014, between the Company and The Bank of New York
Trust Company, N.A., as successor-in-interest to J.P. Morgan Trust Company, National Association, as
Trustee, under the Indenture, dated as of July 19, 2005, between the Company and J.P. Morgan Trust
Company, National Association, as Trustee, is incorporated herein by reference to Exhibit 4.3 to Registration
Statement on Form S-3 (File Number 333-201074)
4.7 Third Supplemental Indenture, dated June 26, 2018, between the Company and The Bank of New York Trust
Company, N.A., as successor-in-interest to J.P. Morgan Trust Company, National Association, as Trustee,
under the Indenture, dated as of July 19, 2005, between the Company and J.P. Morgan Trust Company,
National Association, as Trustee, is incorporated herein by reference to Exhibit 4(S) to Current Report on
Form 8-K filed on June 26, 2018
4.8 Description of Registrant's Securities is incorporated herein by reference to Exhibit 4.8 to the Annual Report
on Form 10-K filed on March 20, 2020
82

10.1* Walmart Deferred Compensation Matching Plan, as amended and restated effective November 11, 2021
(C)
10.2 Walmart Inc. Management Incentive Plan, as amended effective February 1, 2018 is incorporated by reference
to Exhibit 10(b) to the Annual Report on Form 10-K of the Company for the fiscal year ended January 31,
2018, filed on March 30, 2018
(C)
10.3 Walmart Inc. 2016 Associate Stock Purchase Plan, as amended effective February 1, 2018 is incorporated by
reference to Exhibit 10(c) to the Annual Report on Form 10-K of the Company for the fiscal year ended
January 31, 2018, filed on March 30, 2018
(C)
10.4 Walmart Inc. Stock Incentive Plan of 2015, as amended effective February 1, 2018 is incorporated by
reference to Exhibit 10(d) to the Annual Report on Form 10-K of the Company for the fiscal year ended
January 31, 2018, filed on March 30, 2018
(C)
10.5 Walmart Inc. Supplemental Executive Retirement Plan, as amended effective February 1, 2018 is incorporated
by reference to Exhibit 10(e) to the Annual Report on Form 10-K of the Company for the fiscal year ended
January 31, 2018, filed on March 30, 2018
(C)
10.6 Walmart Inc. Director Compensation Deferral Plan, as amended effective February 1, 2018 is incorporated by
reference to Exhibit 10(f) to the Annual Report on Form 10-K of the Company for the fiscal year ended
January 31, 2018, filed on March 30, 2018
(C)
10.7 Form of Post-Termination Agreement and Covenant Not to Compete with attached Schedule of Executive
Officers who have executed a Post-Termination Agreement and Covenant Not to Compete is incorporated by
reference to Exhibit 10(p) to the Annual Report on Form 10-K of the Company for the fiscal year ended
January 31, 2011, filed on March 30, 2011
(C)
10.7(a) Amended Schedule of Executive Officers who have executed a Post-Termination Agreement and Covenant
Not to Compete in the form filed as Exhibit 10(p) to the Annual Report on Form 10-K of the Company for the
fiscal year ended January 31, 2011 is incorporated herein by reference to Exhibit 10.7(a) to the Annual Report
on Form 10-K for the fiscal year ended January 31, 2020 filed on March 20, 2020
(C)
10.8* Form of Walmart Inc. Stock Incentive Plan of 2015 Restricted Stock Notification of Award and Terms and
Conditions of Award
(C)
10.9* Form of Walmart Inc. Stock Incentive Plan of 2015 Global Share-Settled Performance-Based Restricted Stock
Unit Notification and Terms and Conditions
(C)
10.10 Walmart Officer Deferred Compensation Plan, as amended effective February 1, 2018 is incorporated by
reference to Exhibit 10(a) of the Annual Report on Form 10-K of the Company for the fiscal year ended
January 31, 2018 filed on March 30, 2018
(C)
10.11 Form of Share Settled Restricted Stock Unit Notification and Terms and Conditions Awarded to Suresh
Kumar on July 9, 2019 is incorporated by reference to Exhibit 10.2 to the Quarterly Report of the Company
for the fiscal quarter ended July 31, 2019 filed on September 6, 2019
(C)
10.12 Post Termination Agreement and Covenant Not to Compete between the Company and Suresh Kumar dated
June 6, 2019 is incorporated herein by reference to Exhibit 10.16 to the Annual Report on Form 10-K for the
fiscal year ended January 31, 2020 filed on March 20, 2020
(C)
10.13 Separation Agreement between the Company and Marc Lore dated January 26, 2021 is incorporated herein by
reference to Exhibit 10.18 to the Annual Report on Form 10-K for the fiscal year ended January 31, 2021 filed
on March 19, 2021
(C)
10.14 Retirement Agreement between the Company and M. Brett Biggs dated November 29, 2021 is incorporated
herein by reference to Exhibit 10.1 to the Current Report on Form 8-K filed on November 29, 2021
(C)
10.15 Share Issuance and Acquisition Agreement by and Between Flipkart Private Limited and Walmart Inc. dated
as of May 9, 2018 is incorporated herein by reference to Exhibit 10.1 to the Quarterly Report of the Company
for the fiscal quarter ended July 31, 2018 filed on September 6, 2018 (portions of this exhibit have been
omitted and filed separately with the SEC pursuant to a request for confidential treatment.)
83

10.16 Counterpart Form of Share Purchase Agreement by and Among Wal-Mart International Holdings, Inc., the
shareholders of Flipkart Private Limited identified on Schedule I thereto, Fortis Advisors LLC and Walmart
Inc. dated as of May 9, 2018 is incorporated herein by reference to Exhibit 10.2 to the Quarterly Report of the
Company for the fiscal quarter ended July 31, 2018 filed on September 6, 2018 (portions of this exhibit have
been omitted and filed separately with the SEC pursuant to a request for confidential treatment.)
21* List of the Company's Significant Subsidiaries
23* Consent of Independent Registered Public Accounting Firm
31.1* Chief Executive Officer Section 302 Certification
31.2* Chief Financial Officer Section 302 Certification
32.1** Chief Executive Officer Section 906 Certification
32.2** Chief Financial Officer Section 906 Certification
99.1* State Court Opioids Litigation Case Citations and Currently Scheduled Trial Dates
101.INS* Inline XBRL Instance Document
101.SCH* Inline XBRL Taxonomy Extension Schema Document
101.CAL* Inline XBRL Taxonomy Extension Calculation Linkbase Document
101.DEF* Inline XBRL Taxonomy Extension Definition Linkbase Document
101.LAB* Inline XBRL Taxonomy Extension Label Linkbase Document
101.PRE* Inline XBRL Taxonomy Extension Presentation Linkbase Document
104 Cover Page Interactive Data File (formatted as Inline XBRL and contained in Exhibit 101)
* Filed herewith as an Exhibit.
** Furnished herewith as an Exhibit.
(C) This Exhibit is a management contract or compensatory plan or arrangement
(P) This Exhibit was originally filed in paper format. Accordingly, a hyperlink has not been provided.
(1) Certain instruments defining the rights of holders of long-term debt securities of the Registrant are omitted pursuant to Item601(b)(4)(iii) of Regulation
S-K. The Company hereby undertakes to furnish to the SEC, upon request, copies of any such instruments.
(c) Financial Statement Schedules: None.
ITEM 16. FORM 10-K SUMMARY
None.
84

SIGNATURES
Pursuant to the requirements of Section 13 or 15(d) of the Securities Exchange Act of 1934, the registrant has duly caused this
report to be signed on its behalf by the undersigned, thereunto duly authorized.
Walmart Inc.
Date: March 18, 2022
By
/s/ C. Douglas McMillon
C. Douglas McMillon
President and Chief Executive Officer
Pursuant to the requirements of the Securities Exchange Act of 1934, this report has been signed below by the following
persons on behalf of the registrant and in the capacities and on the dates indicated:
Date: March 18, 2022
By
/s/ C. Douglas McMillon
C. Douglas McMillon
President and Chief Executive Officer and Director
(Principal Executive Officer)
Date: March 18, 2022
By
/s/ Gregory B. Penner
Gregory B. Penner
Chairman of the Board and Director
Date: March 18, 2022
By
/s/ M. Brett Biggs
M. Brett Biggs
Executive Vice President and Chief Financial Officer
(Principal Financial Officer)
Date: March 18, 2022
By
/s/ David M. Chojnowski
David M. Chojnowski
Senior Vice President and Controller
(Principal Accounting Officer)
Signature Page to Walmart Inc.
Form 10-K for the Fiscal Year Ended January 31, 2022
85

Date: March 18, 2022
By
/s/ Cesar Conde
Cesar Conde
Director
Date: March 18, 2022 By /s/ Timothy P. Flynn
Timothy P. Flynn
Director
Date: March 18, 2022 By /s/ Sarah Friar
Sarah Friar
Director
Date: March 18, 2022 By /s/ Carla A. Harris
Carla A. Harris
Director
Date: March 18, 2022 By /s/ Thomas W. Horton
Thomas W. Horton
Director
Date: March 18, 2022
By /s/ Marissa A. Mayer
Marissa A. Mayer
Director
Date: March 18, 2022
By /s/ Steven S Reinemund
Steven S Reinemund
Director
Date: March 18, 2022
By /s/ Randall L. Stephenson
Randall L. Stephenson
Director
Date: March 18, 2022
By
/s/ S. Robson Walton
S. Robson Walton
Director
Date: March 18, 2022
By
/s/ Steuart L. Walton
Steuart L. Walton
Director
Signature Page to Walmart Inc.
Form 10-K for the Fiscal Year Ended January 31, 2022
86

Exhibit 21
Significant Subsidiaries of Walmart Inc.
The following list details certain of the subsidiaries of Walmart Inc. Subsidiaries not included in the list are omitted because, in
the aggregate, they are not significant as permitted by Item 601(b)(21) of Regulation S-K.
Subsidiary
Organized or
Incorporated
Percent of Equity
Securities Owned
Name Under Which Doing Business
Other Than Subsidiary's
Wal-Mart Stores East, LP Delaware, U.S. 100% Walmart
Wal-Mart Stores Texas, LLC Delaware, U.S. 100% Walmart
Wal-Mart Property Company Delaware, U.S. 100% NA
Wal-Mart Real Estate Business Trust Delaware, U.S. 100% NA
Sam's West, Inc. Arkansas, U.S. 100% Sam's Club
Sam's East, Inc. Arkansas, U.S. 100% Sam's Club
Sam's Property Company Delaware, U.S. 100% NA
Sam's Real Estate Business Trust Delaware, U.S. 100% NA
Wal-Mart de Mexico, S.A.B. de C.V. Mexico 71% Walmex
Wal-Mart Canada Corp. Canada 100% Walmart
Flipkart Private Limited Singapore 75% Flipkart
Walmart Chile S.A.
(1)
Chile 100% Walmart Chile
Massmart Holdings Ltd. South Africa 53% Massmart
Qomolangma Holdings Ltd. Cayman Islands 100% NA
(1)
The Company owns substantially all of Walmart Chile.
Exhibit 23
Consent of Independent Registered Public Accounting Firm
We consent to the incorporation by reference in the following Registration Statements:
(1) Shareholder Investment Plan of Wal-Mart Stores, Inc. Form S-3 File No. 333-02089
(2) Wal-Mart Stores, Inc. Director Compensation Plan Form S-8 File No. 333-24259
(3) Wal-Mart Stores, Inc. 401(k) Retirement Savings Plan Form S-8 File No. 333-29847
(4) Wal-Mart Puerto Rico, Inc., 401(k) Retirement Savings Plan Form S-8 File No. 333-44659
(5) Wal-Mart Stores, Inc. Associate Stock Purchase Plan of 1996 Form S-8 File No. 333-62965
(6) Wal-Mart Stores, Inc. Stock Incentive Plan of 2015, which amended and
restated the 2010 plan
Form S-8 File No. 333-60329
(7) Wal-Mart Profit Sharing and 401(k) Plan Form S-8 File No. 333-109421
(8) Wal-Mart Stores, Inc. Associate Stock Purchase Plan of 1996 Form S-8 File No. 333-109417
(9) Wal-Mart Puerto Rico Profit Sharing and 401(k) Plan Form S-8 File No. 333-109414
(10) Wal-Mart Stores, Inc. Stock Incentive Plan of 2015, which amended and
restated the 2010 plan
Form S-8 File No. 333-128204
(11) Walmart Deferred Compensation Matching Plan Form S-8 File No. 333-178717
(12) Wal-Mart Stores, Inc. Common Stock Form S-3 ASR File No. 333-178385
(13) Walmart 401(k) Plan Form S-8 File No. 333-187577
(14) Wal-Mart Stores, Inc. Associate Stock Purchase Plan Form S-8 File No. 333-214060
(15) Debt Securities of Walmart Inc. Form S-3 ASR File No. 333-251124
(16) Walmart Inc. 2016 Associate Stock Purchase Plan Form S-8 File No. 333-228631
(17) Walmart Inc. Stock Incentive Plan of 2015 Form S-8 File No. 333-228635
(18) Walmart 401(k) Plan Form S-8 File No. 333-233682
of our reports dated March 18, 2022, with respect to the consolidated financial statements of Walmart Inc. and the effectiveness
of internal control over financial reporting of Walmart Inc. included in this Annual Report (Form 10-K) of Walmart Inc. for the
year ended January 31, 2022.
/s/ Ernst & Young LLP
Rogers, Arkansas
March 18, 2022

Exhibit 31.1
I, C. Douglas McMillon, certify that:
1. I have reviewed this Annual Report on Form 10-K of Walmart Inc. (the "registrant");
2. Based on my knowledge, this report does not contain any untrue statement of a material fact or omit to state a
material fact necessary to make the statements made, in light of the circumstances under which such statements
were made, not misleading with respect to the period covered by this report;
3. Based on my knowledge, the financial statements, and other financial information included in this report, fairly
present in all material respects the financial condition, results of operations and cash flows of the registrant as of,
and for, the periods presented in this report;
4. The registrant's other certifying officer and I are responsible for establishing and maintaining disclosure controls
and procedures (as defined in Exchange Act Rules 13a-15(e) and 15d-15(e)) and internal control over financial
reporting (as defined in Exchange Act Rules 13a-15(f) and 15d-15(f)) for the registrant and have:
a) designed such disclosure controls and procedures, or caused such disclosure controls and procedures to be
designed under our supervision, to ensure that material information relating to the registrant, including its
consolidated subsidiaries, is made known to us by others within those entities, particularly during the period
in which this report is being prepared;
b) designed such internal control over financial reporting, or caused such internal control over financial
reporting to be designed under our supervision, to provide reasonable assurance regarding the reliability of
financial reporting and the preparation of financial statements for external purposes in accordance with
generally accepted accounting principles;
c) evaluated the effectiveness of the registrant's disclosure controls and procedures and presented in this report
our conclusions about the effectiveness of the disclosure controls and procedures, as of the end of the period
covered by this report, based on such evaluations; and
d) disclosed in this report any change in the registrant's internal control over financial reporting that occurred
during the registrant's most recent fiscal quarter that has materially affected, or is reasonably likely to
materially affect, the registrant's internal control over financial reporting.
5. The registrant's other certifying officer and I have disclosed, based on our most recent evaluation of internal control
over financial reporting, to the registrant's auditors and the Audit Committee of registrant's Board of Directors:
a) all significant deficiencies and material weaknesses in the design or operation of internal control over
financial reporting which are reasonably likely to adversely affect the registrant's ability to record, process,
summarize and report financial information; and
b) any fraud, whether or not material, that involves management or other employees who have a significant
role in the registrant's internal control over financial reporting.
Date: March 18, 2022 /s/ C. Douglas McMillon
C. Douglas McMillon
President and Chief Executive Officer

Exhibit 31.2
I, M. Brett Biggs, certify that:
1. I have reviewed this Annual Report on Form 10-K of Walmart Inc. (the "registrant");
2. Based on my knowledge, this report does not contain any untrue statement of a material fact or omit to state a
material fact necessary to make the statements made, in light of the circumstances under which such statements
were made, not misleading with respect to the period covered by this report;
3. Based on my knowledge, the financial statements, and other financial information included in this report, fairly
present in all material respects the financial condition, results of operations and cash flows of the registrant as of,
and for, the periods presented in this report;
4. The registrant's other certifying officer and I are responsible for establishing and maintaining disclosure controls
and procedures (as defined in Exchange Act Rules 13a-15(e) and 15d-15(e)) and internal control over financial
reporting (as defined in Exchange Act Rules 13a-15(f) and 15d-15(f)) for the registrant and have:
a) designed such disclosure controls and procedures, or caused such disclosure controls and procedures to be
designed under our supervision, to ensure that material information relating to the registrant, including its
consolidated subsidiaries, is made known to us by others within those entities, particularly during the period
in which this report is being prepared;
b) designed such internal control over financial reporting, or caused such internal control over financial
reporting to be designed under our supervision, to provide reasonable assurance regarding the reliability of
financial reporting and the preparation of financial statements for external purposes in accordance with
generally accepted accounting principles;
c) evaluated the effectiveness of the registrant's disclosure controls and procedures and presented in this report
our conclusions about the effectiveness of the disclosure controls and procedures, as of the end of the period
covered by this report, based on such evaluations; and
d) disclosed in this report any change in the registrant's internal control over financial reporting that occurred
during the registrant's most recent fiscal quarter that has materially affected, or is reasonably likely to
materially affect, the registrant's internal control over financial reporting.
5. The registrant's other certifying officer and I have disclosed, based on our most recent evaluation of internal control
over financial reporting, to the registrant's auditors and the Audit Committee of registrant's Board of Directors:
a) all significant deficiencies and material weaknesses in the design or operation of internal control over
financial reporting which are reasonably likely to adversely affect the registrant's ability to record, process,
summarize and report financial information; and
b) any fraud, whether or not material, that involves management or other employees who have a significant
role in the registrant's internal control over financial reporting.
Date: March 18, 2022 /s/ M. Brett Biggs
M. Brett Biggs
Executive Vice President and Chief Financial Officer

Exhibit 32.1
CERTIFICATION PURSUANT TO
18 U.S.C. SECTION 1350 (AS ADOPTED
PURSUANT TO SECTION 906 OF THE
SARBANES-OXLEY ACT OF 2002)
In connection with the Annual Report of Walmart Inc. (the "Company") on Form 10-K for the period ending January 31,
2022 as filed with the Securities and Exchange Commission on the date hereof (the "Report"), I, C. Douglas McMillon,
President and Chief Executive Officer of the Company, certify to my knowledge and in my capacity as an officer of the
Company, pursuant to 18 U.S.C. 1350, as adopted pursuant to Section 906 of the Sarbanes-Oxley Act of 2002, that:
1. The Report fully complies with the requirements of Section 13(a) or 15(d) of the Securities Exchange Act of 1934, as
amended; and
2. The information contained in the Report fairly presents, in all material respects, the financial condition and results of
operations of the Company as of the dates and for the periods expressed in the Report.
IN WITNESS WHEREOF, the undersigned has executed this Certificate, effective as of March 18, 2022.
/s/ C. Douglas McMillon
C. Douglas McMillon
President and Chief Executive Officer

Exhibit 32.2
CERTIFICATION PURSUANT TO
18 U.S.C. SECTION 1350 (AS ADOPTED
PURSUANT TO SECTION 906 OF THE
SARBANES-OXLEY ACT OF 2002)
In connection with the Annual Report of Walmart Inc. (the "Company") on Form 10-K for the period ending January 31,
2022 as filed with the Securities and Exchange Commission on the date hereof (the "Report"), I, M. Brett Biggs, Executive
Vice President and Chief Financial Officer of the Company, certify to my knowledge and in my capacity as an officer of the
Company, pursuant to 18 U.S.C. 1350, as adopted pursuant to Section 906 of the Sarbanes-Oxley Act of 2002, that:
1. The Report fully complies with the requirements of Section 13(a) or 15(d) of the Securities Exchange Act of 1934, as
amended; and
2. The information contained in the Report fairly presents, in all material respects, the financial condition and results of
operations of the Company as of the dates and for the periods expressed in the Report.
IN WITNESS WHEREOF, the undersigned has executed this Certificate, effective as of March 18, 2022.
/s/ M. Brett Biggs
M. Brett Biggs
Executive Vice President and Chief Financial Officer

Corporate and Stock Information
Listing
New York Stock Exchange
Stock Symbol: WMT
Corporate Information
Stock Registrar and Transfer Agent:
Computershare Trust Company, N.A.
P.O. Box 505000
Louisville, Kentucky 40233-5000
1-800-438-6278
TDD for hearing-impaired inside the U.S. 1-800-952-9245
Internet: http://www.computershare.com
Annual Meeting
Our 2022 Annual Shareholders’ Meeting will be held on Wednesday,
June 1, 2022 at 10:30am CDT in a virual meeting format only, with
no physical in-person meeting. Our Annual Shareholders’ Meeting
will be available for viewing at
www.virualshareholdermeeting.com/WMT2022.
Communication with Shareholders
Walmar Inc. periodically communicates with our shareholders
and other members of the investment community about our
operations. For furher information regarding our policy on
shareholder and investor communications refer to our website,
www.stock.walmar.com.
The following repors are available without charge upon request
by writing the company c/o Investor Relations or by emailing
IR@walmar.com. These repors are also available via the
corporate website.
• Annual Repor on Form 10-K
• Quarerly Repors on Form 10-Q
• Earnings Releases
• Current Repors on Form 8-K
• Annual Shareholders’ Meeting Proxy Statement
• Environmental, Social and Governance Repor
• Culture, Diversity, Equity & Inclusion Repor
Independent Registered Public Accounting Firm
Ernst & Young LLP
5417 Pinnacle Point Dr., Suite 501
Rogers, AR 72758
Market Price of Common Stock
The high market price and low market price per share for the
Company’s common stock for each fiscal quarer in fiscal 2022
and 2021 were as follows:
Fiscal Years Ended January 31,
2022 2021
High Low High Low
st Quarer $. $. $. $.
nd Quarer . . . .
rd Quarer . . . .
th Quarer . . . .
The high market price and low market price per share for the Company’s
common stock for the first fiscal quarer of fiscal 2023, were as follows:
2023
High Low
1st Quarer
(1)
$146.94 $132.01
(1)
Through March 16, 2022
Dividends Payable Per Share
For fiscal 2023, dividends will be paid based on the following schedule:
April 4, 2022 $0.56
May 31, 2022 0.56
September 6, 2022 0.56
January 3, 2023 0.56
Dividends Paid Per Share
For fiscal 2022, dividends were paid based on the following schedule:
April 5, 2021 $0.55
June 1, 2021 0.55
September 7, 2021 0.55
January 3, 2022 0.55
Dividends Paid Per Share
For fiscal 2021, dividends were paid based on the following schedule:
April 6, 2020 $0.54
June 1, 2020 0.54
September 8, 2020 0.54
January 4, 2021 0.54
Stock Perormance Char
This graph compares the cumulative total shareholder return
on Walmar’s common stock during the five fiscal years ending
through fiscal 2022 to the cumulative total returns on the S&P 500
Retailing Index and the S&P 500 Index. The comparison assumes
$100 was invested on February 1, 2017, in shares of our common
stock and in each of the indices shown and assumes that all of the
dividends were reinvested.
Comparison of 5-Year Cumulative Total Return*
Among Walmar Inc., the S&P 500 Index and S&P 500 Retailing Index
* Assumes $100 Invested on February 1, 2017
Assumes Dividends Reinvested
Fiscal Year Ended January 31, 2022
Fiscal Years Ended January 31,
Walmar Inc. $. $. $. $. $. $.
S&P Index . . . . . .
S&P
Retailing Index . . . . . .
Holders of Record of Common Stock
As of March 16, 2022, there were 209,870 holders of record of
Walmar’s common stock.
$350
$300
$250
$200
$150
$100
$ 50
$ 0
20222017 2018 2019 20212020
Fiscal Years
S&P 500 Retailing IndexS&P 500 IndexWalmart Inc.
Comparison of 5-Year Cumulative Total Return – 2022

702 SW 8th St. Bentonville, AR 72716 | corporate.walmar.com
Our ESG Priorities
OPPORTUNITY
• Good jobs and advancement
• Equity and inclusion
• Growth for suppliers and sellers
SUSTAINABILITY
• Climate leadership
• Zero waste
• Regeneration of natural resources
• Sustainable product supply chains
• People in supply chains
COMMUNITY
• Serving communities
• Access to safer, healthier food
• Disaster preparedness
ETHICS & INTEGRITY
• Ethics and compliance
• Strong corporate governance
• Engagement in public policy
• Digital citizenship
• Human rights
Aspirations for Climate Action
Walmar is committed to science-based
targets for emissions and:
Achieving
ZERO EMISSIONS
by 2040
STRENGTHENING
THE RESILIENCE
of our business
against the effects
of climate change
Engaging Suppliers through
Project Gigaton to reduce or avoid
1 BILLION METRIC TONS
of emissions by 2030
GALVANIZING
COLLECTIVE ACTION
through advocacy,
supplier engagement
and philanthropy
